Security researcher finds code signing flaw that opens door for iOS malware
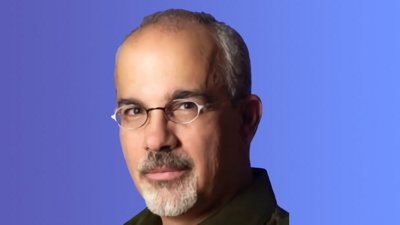
Mac hacker and researcher Charlie Miller has reportedly found a way to sneak malware into the App Store and subsequently onto any iOS device by exploiting a flaw in Apple's restrictions on code signing, allowing the malware to steal user data and take control of certain iOS functions, according to Forbes.
Miller explains that code signing restrictions allow only Apple's approved commands to run in an iOS device's memory, and submitted apps that violate these rules are not allowed on the App Store. However, he has found a method to bypass Apple's security by exploiting a bug in iOS code signing that allows an app to download new unapproved commands from a remote computer.
"Now you could have a program in the App Store like Angry Birds that can run new code on your phone that Apple never had a chance to check,†Miller said. “With this bug, you can’t be assured of anything you download from the App Store behaving nicely.â€
The flaw was introduced when Apple released iOS 4.3, which increased browser speed by allowing javascript code from the internet to run on a much deeper level in a device's memory than in previous iterations of the OS. Miller realized that in exchange for speed, Apple created a new exception for the web browser to run unapproved code. The researcher soon found a bug that allowed him to expand the flawed code beyond the browser, integrating it into apps downloaded from the App Store.
Miller created proof-of-concept app called "Instastock" to showcase the vulnerability, which was submitted to and approved by Apple to be distributed via the App Store. The simple program appears to be an innocuous stock ticker, but it can leverage the code signing bug to communicate with Miller's server to pull unauthorized commands onto the affected device. From there the program has the ability to send back user data including address book contacts, photos and other files, as well as initiate certain iOS functions like vibrating alerts.
The app has since been pulled and according to his Twitter account, Miller has reportedly been banned from the App Store and kicked out of the iOS Developer Program.
Miller, a former NSA analyst who now works for computer security firm Accuvant, is a prominent Apple researcher who previously exposed the MacBook battery vulnerability and a security hole in the mobile version of Safari.
The researcher has refused to publicly reveal the exploit, reportedly giving Apple time to come up with a fix, though he will announce the specifics at the SysCan conference in Taiwan next week.
 Mikey Campbell
Mikey Campbell









 Andrew Orr
Andrew Orr
 Sponsored Content
Sponsored Content
 Malcolm Owen
Malcolm Owen

 William Gallagher
William Gallagher

 Mike Wuerthele
Mike Wuerthele
 Christine McKee
Christine McKee