Samsung adds security layer to Android to gain enterprise credibility
In response to lackluster interest in Google's Android platform by corporate enterprise and government users, Samsung has announced plans to shore up its smartphones and tablets with third party security software in an initiative branded as "SAFE," or "Samsung For Enterprise."
Announced at last week's Mobile World Congress, Samsung has partnered with Centrify to add "fundamental security and management enhancements" in order "to address the shortcomings of the current open source Android platform."
Knox is intended "to address the shortcomings of the current open source Android platform"
Branded as "Knox" by Samsung, the new software adds support for a series of enterprise features Android has lagged iOS in supporting. The first of these, support for "Advanced Microsoft Exchange ActiveSync features," was first addressed by Apple five years ago in 2008's iOS 2.0.
The second feature, "on-device AES 256-bit encryption," is a prerequisite of Microsoft's Exchange default policy settings. Apple began supporting hardware device encryption with the iPhone 3GS in 2009.
A third feature touted by Samsung is VPN support, a notable problem for Android users that want to connect to various remote networking systems. It's also a feature Apple began addressing along with Exchange support back in 2008's iOS 2.0. Apple has regularly enhanced its VPN support on iOS devices in subsequent releases over the last half decade.
Welcome to the sandbox, at least for the Galaxy-only version of Android
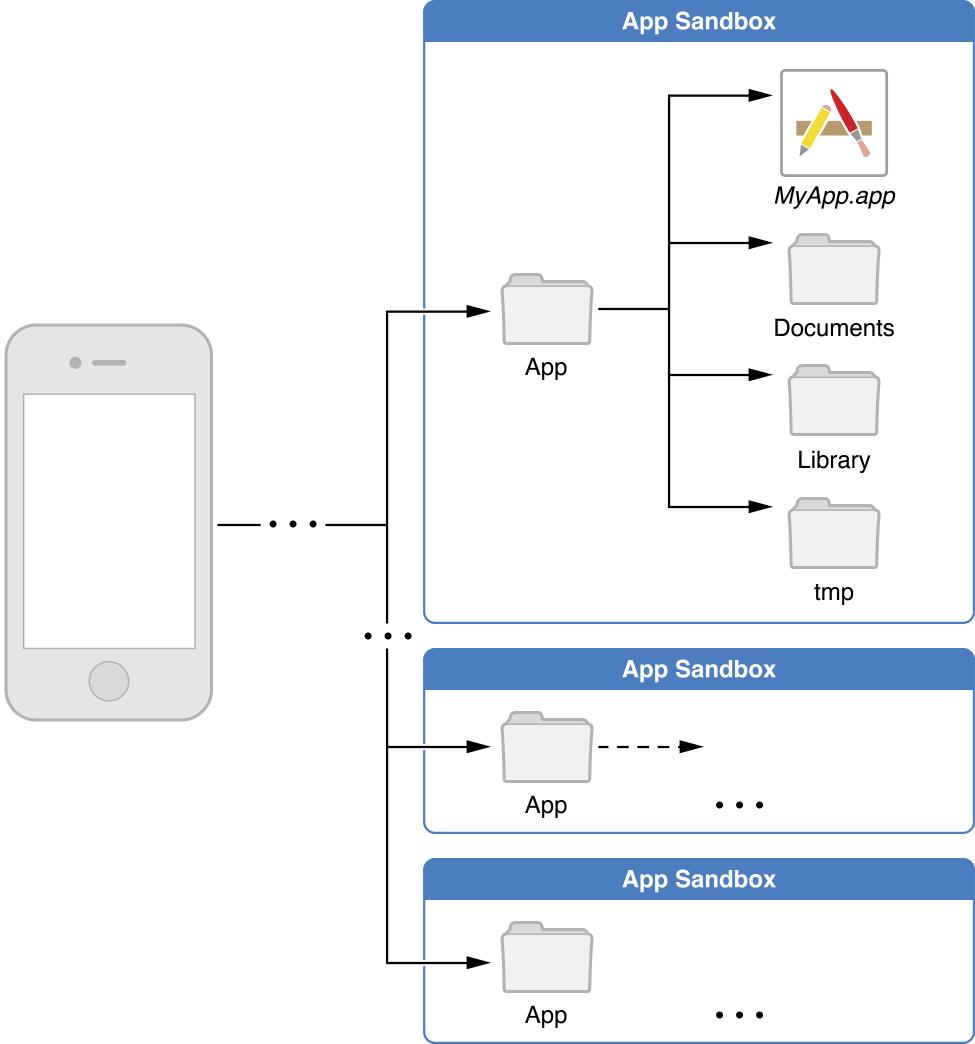
Another primary focus of Samsung's new Knox layer is app "containerization," a security access control feature that Apple refers to as "app sandboxing" on iOS.
Sandboxing prevents one app from being able to read data or modify the code of other apps installed on the system (as portrayed by Apple in its developer documentation, pictured above). This feature helps to contain malware and other security threats, so that even if a vulnerable app is cracked via an exploit (or a malicious app manages to get itself installed on a device), it can't be used to gain further access to other software or data stored on the device.
This feature is critical to enterprise customers who don't want their users to store corporate data on an insecure device loaded with sideloaded home-brew software or malicious software that automatically has full, open access to everything else on the device. In itself, it's a principle reason why Android has such a small showing among enterprise users, despite Android's large presence in low end consumer offerings.
While Google's Android platform offers rudimentary sandboxing security that requires apps to specify what specific permissions they require, it is customary for app developers to request "long lists of permissions that their apps don’t really need."
As a result, users are tasked with approving complex, opaque security requests that essentially give many apps virtually unrestricted access to the user's private information, location and other sensitive data, resulting in issues with developers harvesting inappropriate data from their users, as well as malicious efforts to steal data using phony games and other titles that actually serve as spyware.
Samsung sees little enterprise opportunity; Knox would?
Knox also addresses Android's lack of coherent "single sign on" enterprise mobile authentication and fleet device management features, both of which enable enterprise users to secure their employees' devices with centralized policies (such as disabling Bluetooth or camera features, or preventing app installations) and remotely manage the devices from a central location.
Apple similarly had little previous exposure in the enterprise when it introduced the iPhone in 2007. However, the company immediately made implementing support for enterprise features a central priority, in conjunction with the opening of the App Store back in 2008. Since then, Apple has rapidly introduced new support for related features of interest to business users.
Apple's Macintosh platform had fought for years to be taken seriously in the enterprise; its mobile iOS platform also faced initial barriers of adoption from companies that were heavily invested in enterprise mobile solutions from Blackberry and Microsoft.
However, the usability and desirability of Apple's iPhone, along with an early and focused initiative by Apple to add serious security and management features to iOS, kicked off a global "Bring Your Own Device" trend, rapidly eroding the position of its entrenched competitors and vaulting Apple to the top of corporations' and government agencies' mobile deployment plans. BlackBerry and Microsoft now support more new iOS devices on their own proprietary enterprise servers than their own platforms' devices.
Somewhat ironically, Apple's historical minority share of the enterprise market on the Mac has been reversed with iOS; Apple now accounts for the majority of mobile devices being used in the enterprise, while Microsoft, BlackBerry, Samsung and everyone else share the scraps.
This reversal has also enabled Apple's Macintosh line to gain new access in government and corporate circles, aided by the commonality in software development of the two platforms and the BYOD breakdown of barriers that once protected Windows and BlackBerry from significant new competition.
Good for Samsung, bad for Android
As Android's primary successful and profitable licensee, Samsung is now running into severe barriers of enterprise adoption due to the haphazard and security policies of Google's Android platform, which not only lacks comprehensive, native support for app sandboxing and remote management, but also receives only secondary, limited support from many of the third parties focusing on securing mobile devices.
Apart from the antivirus and malware containment software tools that exist (by necessity) almost exclusively for Android, third party mobile security efforts aren't focused on Android. Instead, they target the iOS devices their enterprise clients are actually using, according to the mobile device management vendors AppleInsider has consulted.
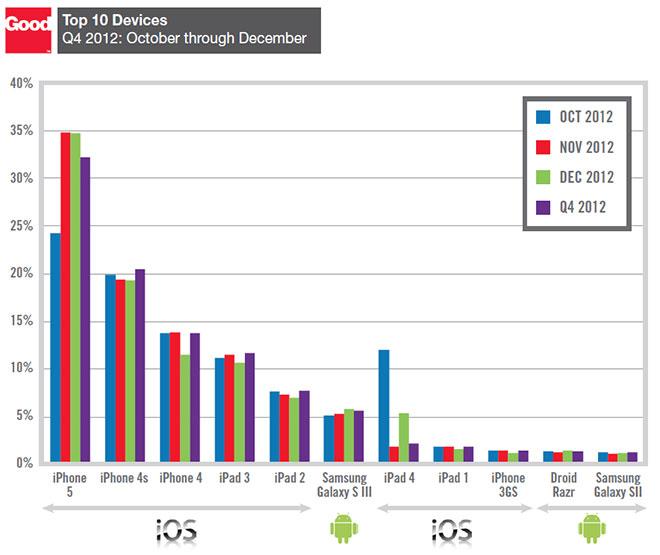
In the regular reports issued by mobile management vendor Good Technology over the past several years, enterprise users have demonstrated "a clear preference" for Apple's iOS. The firm's most recent report noted that Apple held eight of the the top ten spots in mobile phones and tablets (depicted above), a particularly notable metric because Apple has only sold eight different iOS devices since 2010.
Samsung's efforts to make its devices more attractive to the enterprise aren't being shared back with the greater Android community. Instead, Samsung is branding its own "Knox enhanced" version of Android as "safe for business," a phrase that implicitly admits that the stock Android is not safe for business.
The more successful Samsung is in gaining support for its Knox initiative, the harder it will be for Google to have its own Motorola and Nexus branded devices to be taken seriously by enterprise users, not to mention the "white box" market and other smaller brands of Android, Android forks such as Amazon Kindle Fire, and other variants of Android that are collectively pooled to describe an "Android platform," despite various incompatibilities among the fractured third party features and OS API levels of different generations of Android now being sold worldwide.
Two Samsung models are "SAFE," the rest are not
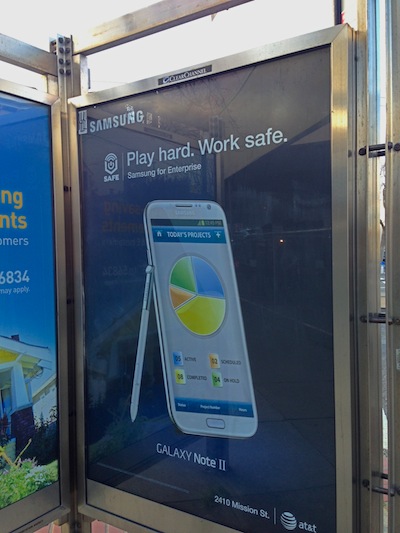
The company has partnered with AT&T to promote Samsung's latest Galaxy SIII and Note II as "safe for business" in new billboards installed in San Francisco (shown below) albeit using advertising that depicts the devices running phony mockups of business presentation and project management software that doesn't really exist.
Samsung hasn't yet taken on the task of developing its own productivity software to rival Apple's touch-centric Pages, Numbers and Keynote. Instead, its "Galaxy at Work" promotional pages depict additional placeholder apps and the stylus doodle pad apps Samsung bundles on its Note II, performing tasks such as drawing a circle over a photo and scribbling "plans approved," or productively typing a "secure email" while watching a video of children playing in the corner of the screen.
Samsung's Knox layer is also being extended to Android developers in a way that will result in apps that only work securely on Samsung phones that include the Knox software layer. This excludes not just the vast majority of devices sold worldwide that make use of some version of Android, but also excludes the rest of Samsung's own phones (apart from the SIII and Note II) many of which ship with outdated versions of Google's platform, and which are unlikely to ever be upgraded to support Knox.
Combined with the fact that Samsung has historically refused to issue timely Android updates for its own users, this means that even among companies with liberal "BYOD" policies, very few Android devices can even qualify as having the minimal security required by enterprise users.
SAFE to replace all your hardware?
Some aspects of Knox, including hardware encryption and the Microsoft Exchange support it enables, can't simply be delivered in a software update. Existing Samsung users will simply have to replace their phones.
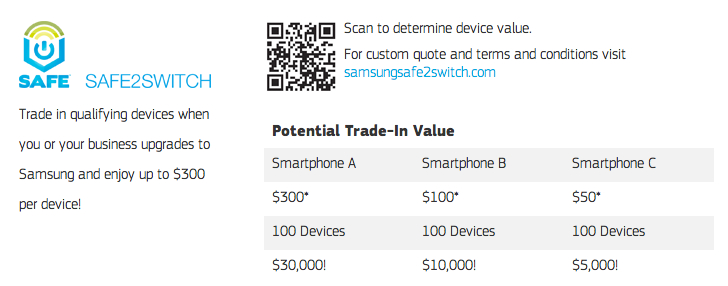
To address this expense in hardware upgrades, Samsung is offering to purchase company's existing devices in a "safe to switch" program that suggests business can defer as much as $30,000 in upgrade expenses on 100 phones valued at $300 each (about half the cost of buying all new "SAFE" hardware from Samsung).
However, this only applies to the repurchase of brand new devices like a $750 16GB iPhone 5 in perfect condition. For other devices (such as an iPhone 3GS in top condition), Samsung is only offering $30. The company values its own 7 inch AT&T Galaxy Tab at a $65 trade in.
 Daniel Eran Dilger
Daniel Eran Dilger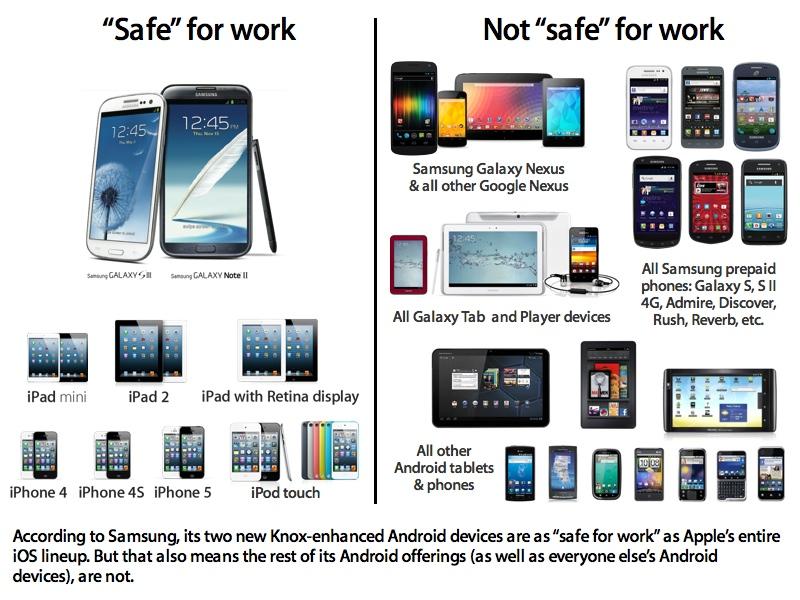












 Wesley Hilliard
Wesley Hilliard
 Andrew Orr
Andrew Orr



 Amber Neely
Amber Neely

 William Gallagher
William Gallagher







