Hundreds of iOS apps vulnerable to HTTPS-based FREAK attack
A report on Tuesday points out that a recent SSL/TLS vulnerability dubbed "FREAK" is not restricted to Web browsers and can affect mobile apps, leaving hundreds of iOS apps open to potential man-in-the-middle attacks.
Security researchers at FireEye recently went through thousands of iOS and Android apps and found that while a bulk are not vulnerable to the "FREAK" (Factoring RSA Export Keys) attack, a significant number are, reports Ars Technica.
Specifically, 771 of the top 14,079 apps in the iOS App Store are open to attack, while 1,288 Android apps with one million plus downloads are similarly vulnerable. According to researchers, vulnerable apps use affected crypto libraries to connect to servers with weak encryption keys, which are apparently still in use today.
"As an example, an attacker can use a FREAK attack against a popular shopping app to steal a user's login credentials and credit card information," FireEye researchers Yulong Zhang, Zhaofeng Chen, Hui Xue, and Tao Wei said. "Other sensitive apps include medical apps, productivity apps and finance apps."
Following FREAK's discovery, Apple issued patches for OS X, iOS and Apple TV, though apps running on hardware without the latest security update may still be exposed. FireEye said seven of the 771 iOS apps affected are even vulnerable with Apple's patch installed.
Discovered earlier in March, the FREAK exploit takes advantage of legacy support for decades-old — and deprecated — SSL/TLS encryption protocols. Malicious users can force an encryption downgrade to intercept secure communications and harvest sensitive data.
 AppleInsider Staff
AppleInsider Staff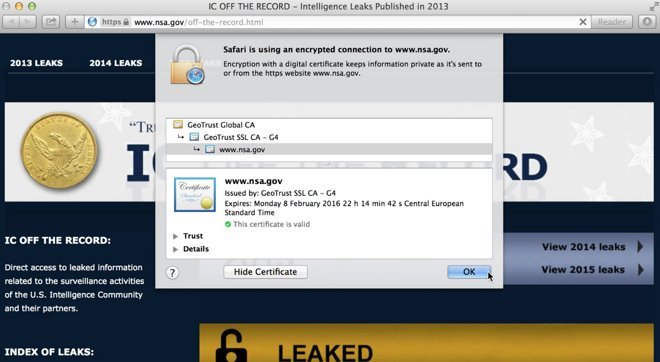







 Malcolm Owen
Malcolm Owen
 William Gallagher and Mike Wuerthele
William Gallagher and Mike Wuerthele
 Christine McKee
Christine McKee
 William Gallagher
William Gallagher
 Marko Zivkovic
Marko Zivkovic









