macOS High Sierra App Store settings menu not effectively secured by user password
The macOS High Sierra 10.13.2 App Store settings can be unlocked with any password entered by an administrator account — but Apple appears to have already implemented a fix in the beta releases currently in testing.
Filed on Open Radar on Jan. 8, and first spotted by MacRumors, the vulnerability allows any user with physical access to a machine logged into an account with administrator level access or greater to alter App Store settings at will, without having to enter a legitimate password. Assailants can alter password requirement settings, or disable the computer's automatic installation of macOS patches.
As vulnerabilities go, this is a dramatic mis-step in quality assurance and testing, but not one with dramatic security effects to the user. The previous bug that could create and grant access to a Root account had more profound security implications.
AppleInsider reproduced this issue on High Sierra 10.13.1 and 10.13.2. However, the vulnerability appears to have been patched on High Sierra 10.13.3 beta 4, and appears to have not existed on High Sierra 10.13 prior to updates. We could not reproduce it on Sierra, El Capitan, Mavericks, or Lion.
Users can minimize risk by keeping their Mac physically secure, and logging out when leaving the presence of the machine. Further security can be provided by preventing remote access to the machine by untrusted parties.
 Mike Wuerthele
Mike Wuerthele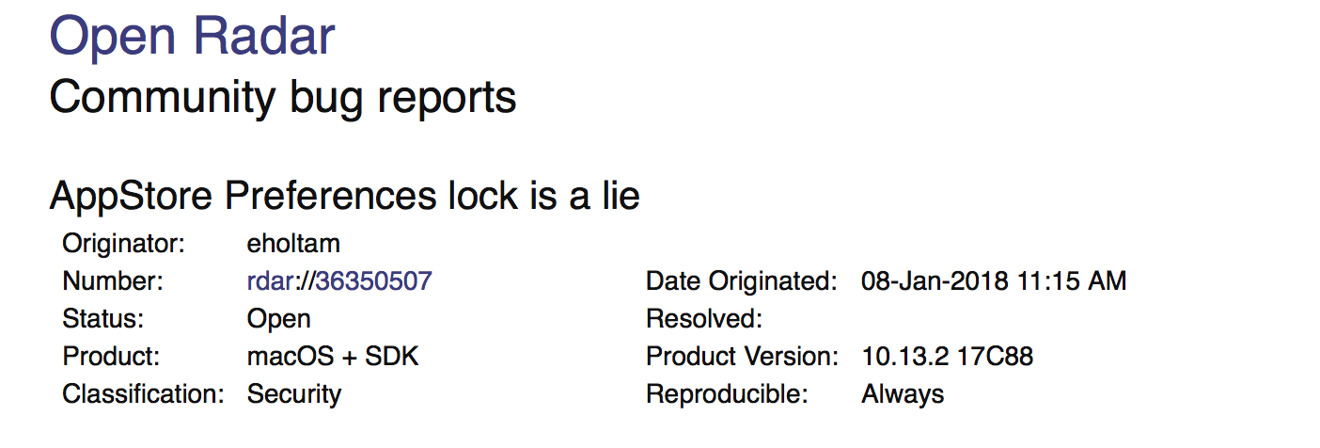







 Charles Martin
Charles Martin
 Malcolm Owen
Malcolm Owen
 William Gallagher and Mike Wuerthele
William Gallagher and Mike Wuerthele
 Christine McKee
Christine McKee
 William Gallagher
William Gallagher
 Marko Zivkovic
Marko Zivkovic








