In what is reportedly the third major version of the secretive country's homegrown Linux distribution, North Korean software makers appear to have looked toward Cupertino for inspiration.
New screenshots from visiting computer scientist Will Scott show an OS X-style interface complete with a reflective dock, gray-gradient application frames, and blue Aqua controls. The shots were first published by ComputerWorld.
Developed by the Korea Computer Center, a Pyongyang-based information technology research center for the North Korean government, Red Star OS formerly featured a Windows-like desktop. Scott — Â a visiting professor at the Pyongyang University of Science and Technology — Â purchased the software at an official KCC retailer in the capital during his stay.
North Korea's Red Star OS. | Source: ComputerWorldRed Star OS is localized for North Korea, which uses slightly different terminology and spelling than its neighbor to the south. Development is said to target low-powered hardware, requiring only a Pentium III processor running at 800 megahertz, 256 megabytes of RAM, and 3 gigabytes of hard disk space.
In addition to localized variant of WINE, which allows some Windows applications to be run on Linux, Red Star OS contains a customized fork of Mozilla's Firefox browser that can be used to access the country's heavily restricted intranet.
North Korea's Red Star OS. | Source: ComputerWorldThe new operating system is not the first Apple connection to North Korea — late dictator Kim Jong-Il was said to be a fan of the company's products. The U.S. government famously sanctioned the country in 2006 by, in part, banning the sale of Apple's iPod music players to the regime.
 Shane Cole
Shane Cole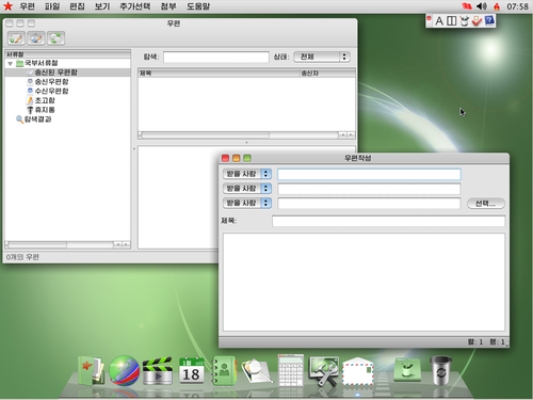



-xl-m.jpg)




 Malcolm Owen
Malcolm Owen
 Marko Zivkovic
Marko Zivkovic

 Chip Loder
Chip Loder
 Christine McKee
Christine McKee
 William Gallagher
William Gallagher
 Amber Neely
Amber Neely



-m.jpg)






56 Comments
I smell a lawsuit coming =)
If North Koreans have this, just Imagine what sort of OS samsung runs on their headquarters, in the South.
OS S 10.9.1, with the famous S-fari browser, and S-tunes. Not to mention the fantastic IDE, sCode, the sBooks app, s-messages, s-photo, s-movie etc.
[quote name="kenfused" url="/t/161894/north-korea-borrows-liberally-from-apples-os-x-in-new-red-star-os-update#post_2467538"]I smell a lawsuit coming =)[/quote] Apple has no jurisdiction to sue in North Korea. Apple's Lawyers will be murdered if flew to North Korea to sue the state.
This can only mean one thing... N Korea has finally perfected its long-range nuclear missile technology. Why else would they so brazenly tempt Apple to declare thermonuclear war?
Seems like Comrade Kim has learned well from Samsung - and yes, it looks much better than any Winblows out there. Congrats, NK!