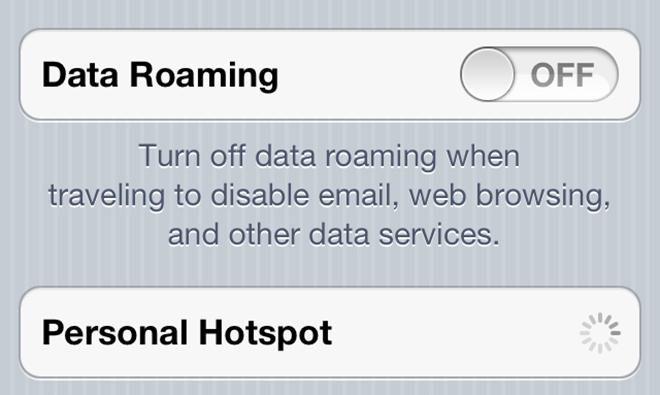
The default generated passwords protecting the mobile hotspot feature of Apple's iPhones and iPads are weak and flawed, according to a group of German researchers claiming to be able to crack iOS Personal Hotspot keys in less than a minute.
In a paper (PDF) titled "Usability vs. Security: The Everlasting trade-OFf in the Context of Apple iOS Mobile Hotspots," researchers from the University of Erlangen demonstrate that iOS generates weak default passwords for its mobile hotspot feature. The researchers found that the mobile hotspot feature is quite susceptible to brute force attacks on the WPA2 handshake.
The paper holds that iOS generates its default passwords based on a word list of roughly 52,500 entries, though iOS apparently relies on about 1,842 of those entries. Additionally, the process for selecting words from the list is insufficiently randomized. That leads to a skewed distribution of words that go into default passwords. That skewed distribution apparently makes it easier to crack a device's password.
Using a GPU cluster with four AMD Radeon HD 7970s, the researchers claimed a 100 percent success rate in cracking iOS-generated passwords. Over the course of the experiment, the researchers got the time to retrieve a password down to around 50 seconds.
The paper notes that "access to a mobile hotspot also results in access to services running on a device." It points to apps like AirDrive HD and other wireless sharing apps as the first easily accessible services once access to the device has been gained.
Besides access to certain apps on the device, the paper also notes that computers and other smart devices connected to the hotspot could also be affected. Additionally, an attacker might be able to intercept messages passing between connected devices and the mobile hotspot.
The researchers write that the entire process of identifying targets, deauthenticating wireless clients, capturing WPA handshakes, and cracking hotspot default passwords could easily be automated. The team even built an app — Hotspot Cracker — in order to automate the word list generation process. The computing power necessary to brute force crack the password, they say, could be supplied by cloud computing services.
In all, the paper notes that the tendency for device manufacturers to make their default hotspot passwords easily memorizable is the main cause of the vulnerability. The researchers call for truly randomized passwords to be the default setting for mobile hotspot-capable devices.
"In the context of mobile hotspots," the report concludes, "there is no need to create easily memorizable passwords. After a device has been paired with once by typing out the displayed hotspot password, the entered credentials are usually cached within the associating device, and are reused within subsequent connections."
The paper also notes that Windows Phone 8 and Android devices can be vulnerable to similar attacks. Android by default generates tougher passwords, but many vendors modify the system for their own devices and change the password settings. Windows Phone 8 passwords consist of only eight-digit numbers, giving hackers a search space of 10^8 candidates.