A newly discovered flaw in Google's Android security model enables rogue apps to gain full access to the Android system and all installed apps, read all data on the device, harvest passwords and create a botnet of "always-on, always-connected and always-moving" spy devices tracking users' location while secretly recording.
The far reaching vulnerability, discovered by San Francisco's Bluebox Security, involves "discrepancies in how Android applications are cryptographically verified & installed, allowing for APK code modification without breaking the cryptographic signature.""A device affected by this exploit could ...become a part of a botnet, eavesdrop with the microphone, export your data to a third party, encrypt your data and hold it hostage, use your device as a stepping stone to another network, attack your connected PC, send premium SMS messages, perform a DDoS attack against a target, or wipe your device."
Android apps (packaged as an "APK") are signed with an encryption key (just like iOS apps) to prevent a malicious party from changing the code. Signed apps are expressly designed to enable the system to detect any tampering or modification.
However, due to the newly discovered Android flaw, a rogue developer can trick the system into thinking that a compromised app is still legitimate, giving it system wide access to do virtually anything.
"A device affected by this exploit could do anything in the realm of computer malice, including become a part of a botnet, eavesdrop with the microphone, export your data to a third party, encrypt your data and hold it hostage, use your device as a stepping stone to another network, attack your connected PC, send premium SMS messages, perform a DDoS attack against a target, or wipe your device," a representative of the company wrote AppleInsider.
Affects everything Android, in a big way
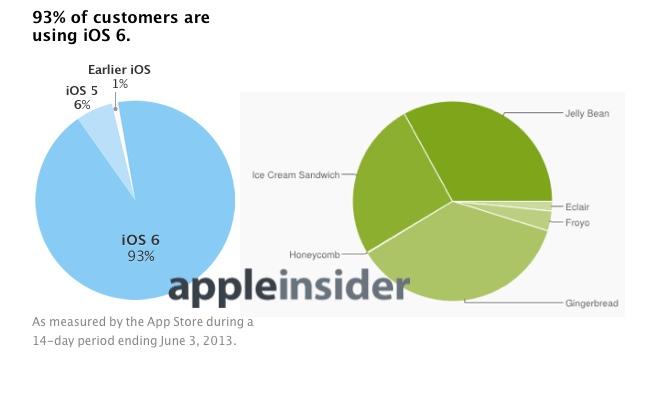
The flaw has been in place since the release of Android 1.6 "Donut," meaning it affects virtually all Android devices sold in over the last four years, essentially all of the installed base of Android devices: Eclair, Froyo, Gingerbread, Honeycomb, Ice Cream Sandwich and Jelly Bean.
A compromised app exploiting the vulnerability can take the appearance of a legitimate app that has been given wide access to system resources. Bluebox notes that many of Android licensees' own apps (such as those from HTC, Samsung, Motorola or LG) as well as many VPN apps (such as Cisco's AnyConnect) are customarily "granted special elevated privileges within Android – specifically System UID access.""most unsettling, is the potential for a hacker to take advantage of the always-on, always-connected, and always-moving (therefore hard-to-detect) nature of these 'zombie' mobile devices to create a botnet."
After bypassing Android's app-signing model to take the place of such an app, rogue malware can obtain "full access to Android system and all applications (and their data) currently installed."
This means the app subsequently "not only has the ability to read arbitrary application data on the device (email, SMS messages, documents, etc.), retrieve all stored account & service passwords, it can essentially take over the normal functioning of the phone and control any function thereof (make arbitrary phone calls, send arbitrary SMS messages, turn on the camera, and record calls)."
Bluebox adds, "finally, and most unsettling, is the potential for a hacker to take advantage of the always-on, always-connected, and always-moving (therefore hard-to-detect) nature of these 'zombie' mobile devices to create a botnet."
A big flaw to fix, requiring 900 million firmware updates
Bluebox disclosed the vulnerability to Google and members of the Open Handset Alliance in February 2013, but the firm notes that "it’s up to device manufacturers to produce and release firmware updates for mobile devices (and furthermore for users to install these updates). The availability of these updates will widely vary depending upon the manufacturer and model in question.""The Android malware ecosystem is beginning to resemble to that which surrounds Windows."
So far, Android licensees have been extremely slow to roll out any updates for their users, often refusing to bother with distributing even significant security patches.
Android's unaddressed security lapses have helped make it the world's leading mobile platform for malware, a problem many of its supporters simply refused to acknowledge. However, this new vulnerability means puts Android users at even more risk, because now they can't even trust apps signed by a legitimate developer.
As security firm F-Secure noted in May, "the Android malware ecosystem is beginning to resemble to that which surrounds Windows."
Bluebox will be detailing the vulnerability in a Black Hat USA 2013 session by its chief technology officer Jeff Forristal.
Partial containment, Google not open to talking about it
Update: a report by Computerworld notes that Samsung has included a patch rectifying the issue for one device: its flagship Galaxy S4. The article noted Forristal as saying that "Google has not released patches for its Nexus devices yet, but the company is working on them."
"Google declined to comment on the matter," the report added. "The Open Handset Alliance did not respond to a request for comment."
However, Google has blocked distribution of apps exploiting the flaw in Google Play, although if user to is tricked into manually installing a malicious update "for an app originally installed through Google Play, the app will be replaced and the new version will no longer interact with the app store."
Addressing the issue of updating the hundreds of millions of Android devices that have already been sold, Computerworld observed, "the slow distribution of patches in the Android ecosystem has long been criticized by both security researchers and Android users.
"Mobile security firm Duo Security estimated last September, based on statistics gathered through its X-Ray Android vulnerability assessment app, that more than half of Android devices are vulnerable to at least one of the known Android security flaws."
 Daniel Eran Dilger
Daniel Eran Dilger

-m.jpg)






 Malcolm Owen
Malcolm Owen
 Marko Zivkovic
Marko Zivkovic

 Chip Loder
Chip Loder
 Christine McKee
Christine McKee
 William Gallagher
William Gallagher
 Amber Neely
Amber Neely


-xl-m.jpg)
-m.jpg)






276 Comments
When your agenda is to collect as much information about users as possible, security will never be prioritized.
That's Android for you.
@hydr - Completely agree. There will always be a way here to get access to data.
The curious part of me wonders how they're going to implement a security fix with so much fragmentation.
Oh it's another Android article with "that graph" they've put up to remind you that Apple belongs somewhere in the conversation.
To all the Walled Garden Apple-hating idiots; welcome to the wide-assed open Android OS where free malware abounds.
I've been waiting for this day, for it was sure to come. Now, 900 million Android customers are re-thinking their earlier choice. I'd not be surprised if Apple sales sees a surge that would put the Sandy hurricane to shame... The new iPhones can't get here soon enough...!!!