Malware targeting mobile devices is rapidly growing in both the number of variants found in the wild and in their complexity and sophistication, but the only platform being actively targeted is Google's Android, which researchers now say is resembling Windows on the desktop PC.
Source: F-Secure Labs
Android's monopoly on malware
According to malware researchers at F-Secure Labs, the number of active mobile threat families and variants initially spiked in the winter quarter, with Android's share jumping from 49 out of 74 known threats to 96 out of 100, with the balance being related to Nokia's essentially mothballed Symbian platform.
That was enough to rouse a tweet from the rarely used account of Apple's head of worldwide marketing Phil Schiller, who linked to the report with the brief admonition "be safe out there."
However, F-Secure's new report for the latest quarter shows Android now accounts for 136 out of 149 known threats, or 91.3 percent of all malware activity (up from 79 percent in 2012).
The other threats remained related to Symbian, with zero discovered for Blackberry, Microsoft's Windows Mobile/Phone or Apple's iOS. The research noted that mobile threats are overwhelmingly motivated by profits, with 76.5 percent designed specifically to con users out of money, rather than seeking to just cause damage.
Android's malware reaches XP proportions
While researchers say the number of malware types is rising significantly, of greater concern is the rise of "highly specialized suppliers" who "provide commoditized malware services" that specifically target weaknesses in the Android platform, resulting in a situation where the "Android malware ecosystem is beginning to resemble to that which surrounds Windows.""The Android malware ecosystem is beginning to resemble to that which surrounds Windows."
Scammers single out Android users with cons that prompt them to update components like Adobe Flash, or direct them to services or job offers that request installation permissions from the user. Once granted, the malware installs code to either make a series of paid calls when the user is sleeping, or install SMS spyware designed to intercept the user's banking details over what appears to be a secure connection.
Those types of attacks are not possible on iOS, where Apple doesn't give third party developers the ability to ask users for obscure permissions or install the their own backdoors to read users' SMS messages. This foils the "commodity malware" business of creating exploit packages that can be sold, a market that is thriving on Android.
One example cited by F-Secure is "SmSilence,†malware discovered in Samsung's home country of South Korea that uses "the guise of 'coupons' for a popular coffeehouse chain," the firm explained. "If the so-called coupon app is installed, the malware will check if the phone number has a South Korean country code (+82). If the condition is met, SmSilence will harvest information from the device and forward the details to a server located in Hong Kong."
Unlike Apple, Samsung relies on Google and the open community to handle its software integration, leaving "open" the potential for such sophisticated attacks that take advantage of users using mechanisms often identical to those that have targeted Microsoft's desktop Windows platform.
Android's malware not limited to bad apps
Malware authors are also now increasingly targeting the many Android users who treat their device like a simple featurephone, the significant proportion of the Android installed base who never install apps.
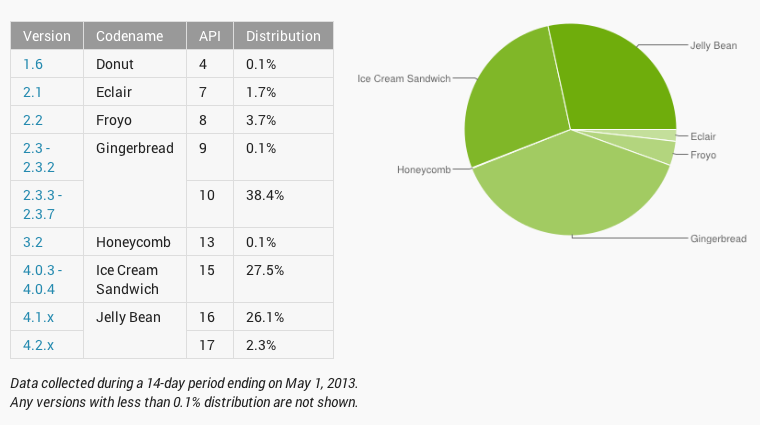
Google stopped counting these users in its installed base statistics for developers (this enhanced version, below) in order to improve the appearance of Android fragmentation, but the majority still use very old versions of Android.
As Sean Sullivan, Security Advisor at F-Secure Labs stated in the report, “I’ll put it this way: Until now, I haven’t worried about my mother with her Android because she’s not into apps. Now I have reason to worry because with cases like Stels, Android malware is also being distributed via spam, and my mother checks her email from her phone.â€
Stels, an Android trojan delivered via fake U.S. Internal Revenue Service-themed emails, uses "an Android crimeware kit to steal sensitive information from the device," and also makes calls to premium numbers. Sullivan said the new threat “could be a game changer.â€
Users on any mobile platform, including iOS, can be targeted with spam that directs them to malware websites. However, while previous exploits have been demonstrated to allow a visited website to crack the security on iOS to "jailbreak" the device, Apple has been vigilant about patching these flaws and distributing iOS updates that scuttle the profitability of discovered threats, effectively frustrating the malware business on iOS.
The majority of Android phones are never updated, so even if Google or its partners were made aware of an exploit and chose to address it with a patch, most Android users would never get the updates, leaving lots of fertile ground for scammers to harvest.Apple developed iOS with controls that specifically limit what installed apps can do and tightly regulate what personal information they can access.
This has opened up a booming business for Android malware that shares much in common with the desktop PC platform, a problem Microsoft worked desperately to fix over the past decade with increasingly sophisticated layers of malware filtering and blocking tools. Those tools, however, incur a performance hit and introduce new complications and inconveniences for users.
In contrast, Apple developed iOS with controls that specifically limit what installed apps can do and tightly regulate what personal information they can access.
These measures were initially greeted with contempt from many pundits who demanded a wide open platform that reintroduced all of the well known problems and vulnerabilities of the desktop computer into the new generation of mobile devices, but it has offered differentiated protection from malware for iOS users.
 Daniel Eran Dilger
Daniel Eran Dilger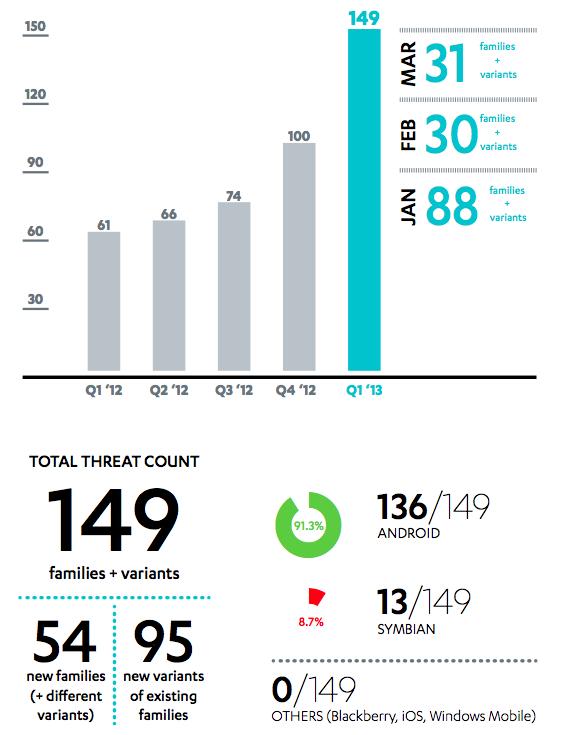







-m.jpg)





 Wesley Hilliard
Wesley Hilliard
 Malcolm Owen
Malcolm Owen
 Andrew Orr
Andrew Orr
 William Gallagher
William Gallagher
 Sponsored Content
Sponsored Content
 Christine McKee
Christine McKee

 Thomas Sibilly
Thomas Sibilly






136 Comments
I'm not a fan of Android, but I hope nobody got hurt by this malware explosion!
I remember XP was so bad when there were "drive-bys" that seemed to infect your PC by visiting top websites with malware infected ads. I'd like to see how Google would block apps that serves malware infected ads.
News flash: Android is a malware, virus infested theme park. What a surprise. But don't worry. If you listen to the know-it-all fandroids, they will just tell you that you should always research the app you want to install and verify that it's from a site you trust. No problem right?? Thanks, but no thanks. I'll let Apple do all that up-front work for me. I have better things to do with my time that to spend it in some fandroid-like basement researching the background of every app I want to install. Kind of like why Android is the dominant mobile OS, yet iOS garners all the web traffic. Android apps are a joke.
laugh out loud, it's deja vu all over again.
But Android is OPEN¡/s