While Apple's robust security practices have made malware a virtual non-factor, iOS device owners should still take care to ensure that they themselves don't become the weak link in the security chain.
A study published this week by internet giant Cisco — Â and tweeted by Apple marketing chief Phil Schiller — paints third-party apps as a leading cause for concern when it comes to security on mobile devices.
"Many users download mobile apps regularly without any thought of security," the report says.
Malware is not Cisco's biggest worry when it comes to mobile apps, though. The honor goes instead to age-old social engineering techniques like phishing, in which malicious individuals try to dupe unsuspecting users into handing over personal information like usernames, passwords, and financial details by pretending to represent legitimate businesses — Â the notorious "Nigerian prince" e-mail scam is one popular example.
"Many users download mobile apps regularly without any thought of security," according to Cisco.
The problem is compounded by the implicit trust users often place in content from the App Store. This week also saw Apple settle with the Federal Trade Commission over in-app purchases, a dispute which boiled down to parents blindly supplying their Apple ID password to their kids without taking the time to understand the implications.
In that case, the parents simply saw a few more charges on their credit cards. The same action in a different context could have much more far-reaching consequences, and this issue has been the subject of a recent kerfuffle in the iOS developer community.
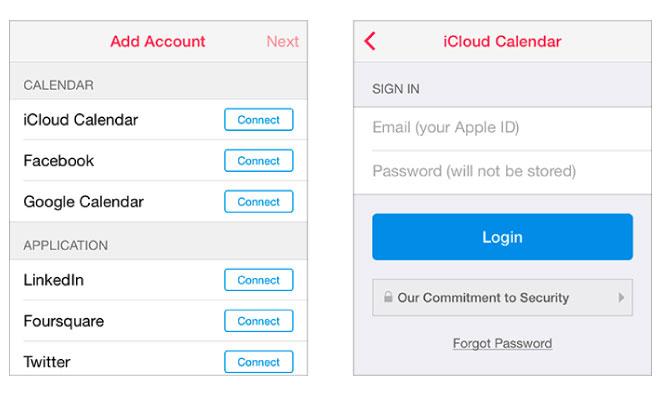
Well-liked social calendaring app Sunrise has come under fire for asking users to enter their Apple ID credentials when adding iCloud calendars, rather than using iOS's built-in calendar access API. Sunrise uses this information for a legitimate purpose — Â services running on their servers facilitate key features that would be difficult or impossible to implement without that access.
The problem, as articulated by Instapaper creator Marco Arment, is that the Apple ID has become a de facto key to many iPhone and iPad users' lives. Consider what happens when an iOS device is restored from an iCloud backup: iMessages, keychain data, email accounts, calendars, contacts, and data-filled apps are all happily retrieved from the cloud.
Of course, users are notified when a new device is added to an account, but even if they take notice of the message, it may be too little too late. Wired reporter Mat Honan had such an experience in 2012:
"In the space of one hour, my entire digital life was destroyed. First my Google account was taken over, then deleted. Next my Twitter account was compromised, and used as a platform to broadcast racist and homophobic messages. And worst of all, my AppleID account was broken into, and my hackers used it to remotely erase all of the data on my iPhone, iPad, and MacBook," Honan wrote.
Surely many people would blanch at the thought of a stranger collecting weeks or months of sensitive iMessage conversations.
The attack on Honan was overt, carried out by hackers whose aim was notoriety, and thus easily noticed. What if it were a more subtle assault, though? Surely many people would blanch at the thought of a stranger collecting weeks or months of sensitive iMessage conversations.
Attackers needn't even go to the trouble of sneaking a phishing app into the App Store. Many services store access credentials on cloud servers, which present an exponentially larger number of attack vectors — Â Sunrise was the victim of an attack on its web infrastructure last November, and was forced to warn users to reset their iCloud passwords.
Fortunately, these potential problems are easily mitigated by the application of common sense. Just as users wouldn't provide their social security number to a stranger on the street, they should carefully evaluate which services have access to their Apple ID. Apple also allows for the use of multiple accounts on a single device — Â one can be used for sensitive information such as iCloud keychain, while another could synchronize less important data like calendars.