Apple on Saturday said it is working to fix a flaw in OS X that could in some cases allow hackers to intercept communication sent using SSL/TSL security protocols. The same error was patched in an iOS update the company rolled out on Friday.
In a statement provided to Reuters, Apple confirmed researcher findings that the same SSL/TSL security flaw fixed with the latest iOS 7.0.2 update is also present in OS X. The Cupertino company said it expects to have a software update ready for release "very soon."
"We are aware of this issue and already have a software fix that will be released very soon," said Apple spokesperson Trudy Muller.
On Friday, Apple quietly pushed out iOS 7.0.2, with accompanying release notes saying the software "provides a fix for SSL connection verification." A support document issued alongside the update read:
iOS 7.0.6Data Security
Available for: iPhone 4 and later, iPod touch (5th generation), iPad 2 and later
Impact: An attacker with a privileged network position may capture or modify data in sessions protected by SSL/TLS
Description: Secure Transport failed to validate the authenticity of the connection. This issue was addressed by restoring missing validation steps.
End users not running the latest patched iOS software may be open to attacks when connected to a shared network. Nefarious users could potentially view, alter or download email and other data sent via the Secure Socket Link protocol, which falls under the umbrella of Transport Layer Security.
As noted in the security document, iOS Secure Transport "failed to validate the authenticity of the connection." At its core, the issue stems from the mishandling and faulty recognition of digital certificates used to establish secure encrypted connections.
In the case of iOS and OS X, Apple's implementation is missing code, causing a failure to verify these certificates. When a user visits what they believe to be a trusted site, hackers can potentially pose as a legitimate certificate holder and collect data sent over the connection before handing it off to the real site.
While it is unclear exactly when Apple discovered the flaw, the CVE (Common Vulnerabilities and Exposures) identification code for the iOS version was reserved and assigned to an unknown party on Jan. 8. The CVE is a publicly available standardized reference for known software security vulnerabilities.
 AppleInsider Staff
AppleInsider Staff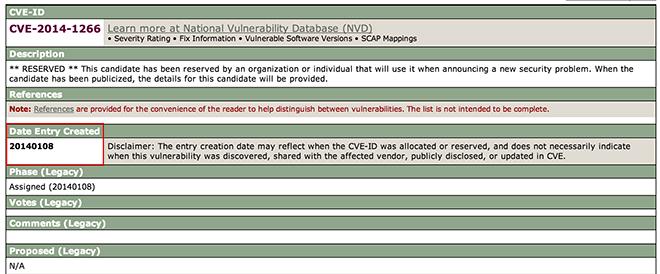

-m.jpg)






 William Gallagher
William Gallagher

 Andrew O'Hara
Andrew O'Hara
 Wesley Hilliard
Wesley Hilliard

 Malcolm Owen
Malcolm Owen
 Marko Zivkovic
Marko Zivkovic





-m.jpg)




66 Comments
1) Still present in latest 10.9.2 beta. 2) As bad as this bug is I would wager that a person using it to read data you assumed secured is very remote.
Seriously... 7.0.2 in the headline and every in-story reference except the copy-n-paste one from Apple?? -- Really... Where's the editorial review, guys?
well, in their defense they did mention 7.0.2 three times and that does add up to 7.0.6.
The headline is wrong. Don't you mean 7.0.6?
7.0.6