Apple's recent iOS, OS X, tvOS and watchOS updates patch a previously unknown security flaw that allows the surreptitious gathering of sensitive data with a simple text message, an OS-level bug which bears a striking resemblance to last year's much derided Stagefright exploit on Google's Android platform.
Like Stagefright, the iOS vulnerability discovered by Cisco Talos engineer Tyler Bohan involves media files delivered by MMS, specifically specially crafted Tagged Image File Format (TIFF) files that contain nefarious payloads used to trigger buffer overflows.
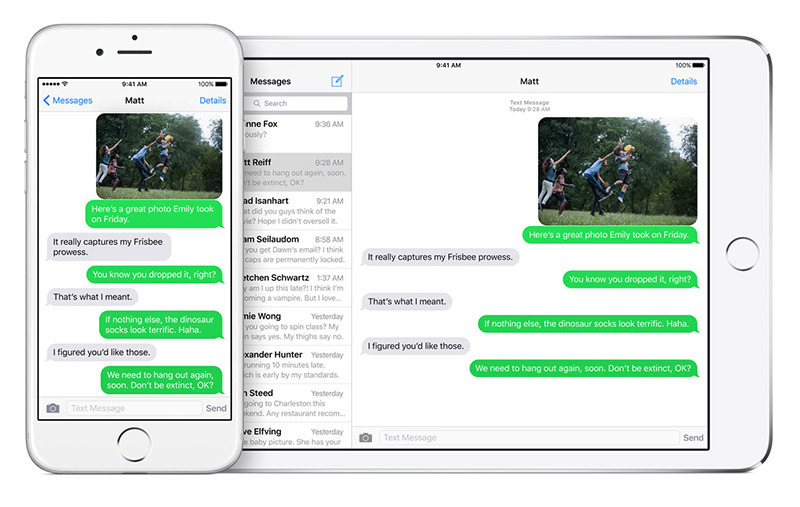
As described by Bohan, when an infected TIFF file is opened on a target device it triggers a buffer overflow in iMessage, or any other app using Apple's Image I/O API to render the image, allowing for remote code execution. Depending on the malicious file's instruction set, nefarious users might be able to gain access to account logins, passwords and other sensitive information.
Bohan notes the vulnerability is especially dangerous as certain iOS apps, including iMessage, automatically attempt to render TIFF images by default. In such cases, payloads would trigger themselves without user intervention. Safari is also vulnerable, though users need to click on a link or load a malicious webpage to trigger the payload.
Forbes reported on the vulnerability's discovery earlier today.
According to Apple's website, the patched flaw impacts image data handler ImageIO, meaning hardware running older versions of iOS, OS X, tvOS and watchOS are at risk. Luckily, Apple on Monday released iOS 9.3.3, OS X 10.11.6, tvOS 9.2.2 and watchOS 2.2.2, all of which patch the bug.