A new strain of Android malware dubbed "Gooligan," thought to be "the largest Google account breach to date," is already in active circulation and three-fourths of the Android installed base is vulnerable. Once infected, devices give hackers access to the users' Gmail, Google Photos, Docs, Drive and other Google services accounts.
Discovered by Check Point Software Technologies, the "new and alarming malware campaign" was found to have already compromised one million Google accounts, and is currently spreading to 13,000 new users each day.
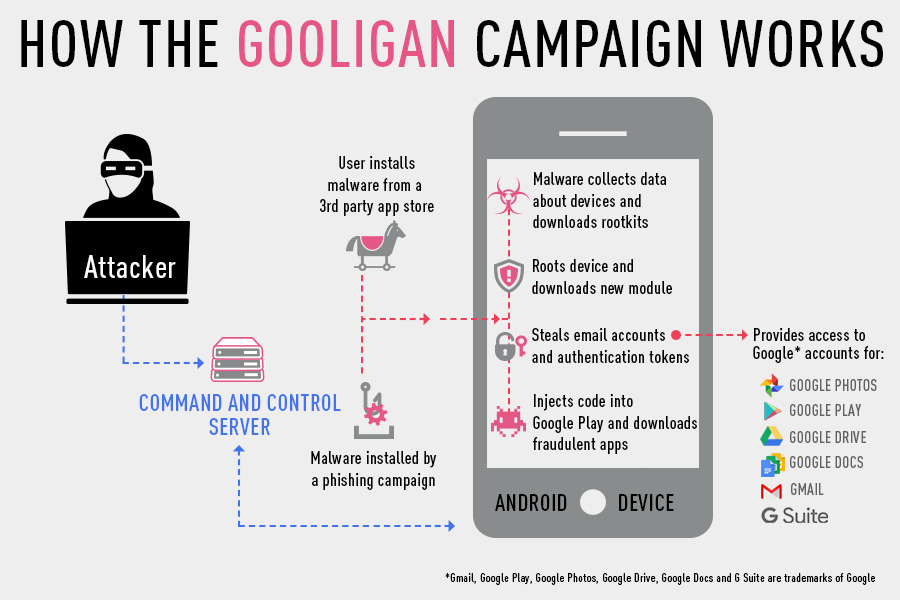
The Gooligan malware is spread through phishing campaigns or malware installed via third party app stores. Once on the device, it sucks up local data, gains root access and downloads a module that enables it to steal the users's email account and Google's authentication tokens that provide it password-free access to the user's Google Photos, Google Play account, files in Google Docs and Google Drive and G Suite.
Stolen authentication tokens bypass various Google security mechanisms, including two-factor-authentication, by allowing the malware that gains control of them to appear to be the already-logged in, legitimate user. Stolen authentication tokens bypass various Google security mechanisms, including two-factor-authentication, by allowing the malware that gains control of them to appear to be the already-logged in, legitimate user
Check Point reported that 57 percent of those hacked are in Asia, but 19 percent are in America and 9 percent are located in Europe. Devices running Android 4 Jelly Bean or KitKat and Android 5 Lollipop are vulnerable. According to Google's latest data from earlier this month, that amounts to 74 percent of all Android users.
The security firm recommends that users who have been compromised do a clean install of the OS via "flashing," which it says "is a complex process."
Check Point added, "we recommend powering off your device and approaching a certified technician, or your mobile service provider, to request that your device be 're-flashed.'"
The group also noted that it "found traces of the Gooligan malware code in dozens of legitimate-looking apps on third-party Android app stores. These stores are an attractive alternative to Google Play because many of their apps are free, or offer free versions of paid apps."
Beyond third party stores, the Gooligan malware "could also be downloaded by Android users directly by tapping malicious links in phishing attack messages," the security firm noted.
The malware exploits two vulnerabilities that Google has patched, but Check Point noted that "these exploits still plague many devices today because security patches that fix them may not be available for some versions of Android, or the patches were never installed by the user."
The malware is monetized both when it logs into Google Play and posts fake app reviews that raise the reputation of apps, and also when it installs further adware to generate direct revenue. The malware also spoofs device IMEI serial numbers to appear to download apps more than once, inflating the app install count of apps that pay for installs.
Apple has benefitted tremendously from Google's inability to secure Android. Apple's iOS holds a commanding share of premium phone sales worldwide and maintains a strong lead in security sensitive market segments including government and corporate enterprise users. Virtually all of Apple's users are on the latest iOS update and most are frequently patched, making it far harder and less lucrative for malware vendors to exploit old iOS security flaws.