An iOS security white paper published by Apple on Wednesday offers a deeper understanding of the company's Touch ID fingerprint sensing system and the so-called "Secure Enclave" found in the A7 SoC, both of which were introduced with the iPhone 5s.
The security document (PDF link) details a number of iOS hardware and software security protocols, including new information outlining how Touch ID and the Secure Enclave work together to keep user data safe. First spotted by TechCrunch, the white paper was published to Apple's "iPhone in Business" website.
According to the paper, the A7's Secure Enclave is actually a coprocessor built into Apple's latest system-on-a-chip design. With a secure boot sequence and software update mechanism separate from the application processor, the component is responsible for "all cryptographic operations for Data Protection key management and maintains the integrity of Data Protection even if the kernel has been compromised."
Each Secure Enclave is provisioned during fabrication with its own UID (Unique ID) that is not accessible to other parts of the system and is not known to Apple. When the device starts up, an ephemeral key is created, tangled with its UID, and used to encrypt the Secure Enclave's portion of the device's memory space.Additionally, data that is saved to the file system by the Secure Enclave is encrypted with a key tangled with the UID and an anti-replay counter.
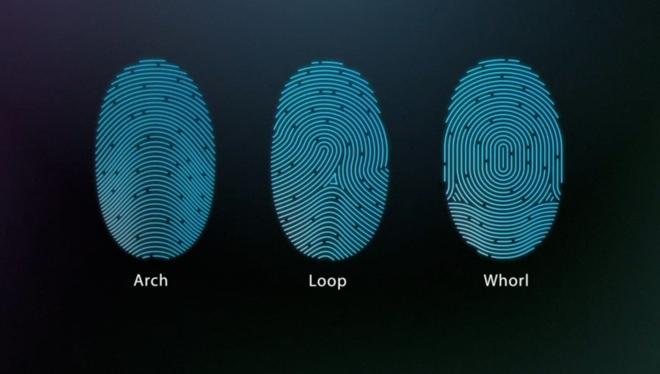
As for Touch ID, Apple notes the iPhone 5s-only technology reads fingerprints from any angle and continuously "learns" a user's fingerprint over time. The paper explains that the sensor expands the stored fingerprint map with each consecutive use by adding newly identified overlapping nodes.
When a user's finger contacts the capacitive steel ring surrounding the home button, the Touch ID sensor performs an 88-by-88-pixel, 500-ppi raster scan that is "temporarily stored in encrypted memory within the Secure Enclave while being vectorized for analysis." The system is sensitive enough that the chance of a random match for one finger is 1 in 50,000.
Once processing and analysis is complete, the data is discarded and is never sent to iCloud, iTunes or Apple.
Explaining how the two technologies work together, Apple says data from the Touch ID module is transferred to the A7 chip via a peripheral interface bus and is subsequently forwarded to the Secure Enclave for decryption.
The application processor cannot read the raw Touch ID data, however, as it is encrypted and protected with a unique session key generated based on a shared key built into the fingerprint sensor and Secure Enclave. Session key exchange uses advanced encryption standard (AES) key wrapping on both ends and AES-CCM transport encryption to provide randomized key generation and enhanced protection.
Unlocking the iPhone 5s is a slightly different process, but uses the same shared secret and data protection key mechanisms:
On iPhone 5s with Touch ID turned on, the keys are not discarded when the device locks; instead, they're wrapped with a key that is given to the Touch ID subsystem. When a user attempts to unlock the device, if Touch ID recognizes the user's fingerprint, it provides the key for unwrapping the Data Protection keys and the device is unlocked. This process provides additional protection by requiring the Data Protection and Touch ID subsystems to cooperate in order to unlock the device.
Decryption keys are stored in memory, meaning the data will be deleted if a device is rebooted. This explains why users must re-enter their password when purchasing an item from the App Store or iTunes. Adding further protection, the Secure Enclave jettisons these keys after 48 hours or five failed Touch ID attempts.
Describing a Touch ID use case in purchasing digital content, Apple explains:
When users choose to authorize a purchase, authentication tokens are exchanged between the device and store. The token and nonce are held in the Secure Enclave. The nonce is signed with a Secure Enclave key shared by all devices and the iTunes Store.
Apple previously detailed a similar shared secret method of authentication in a patent filing pertaining to retail purchases.
The remainder of the white paper focuses on overall iOS security protocols with special attention given to app security layers.