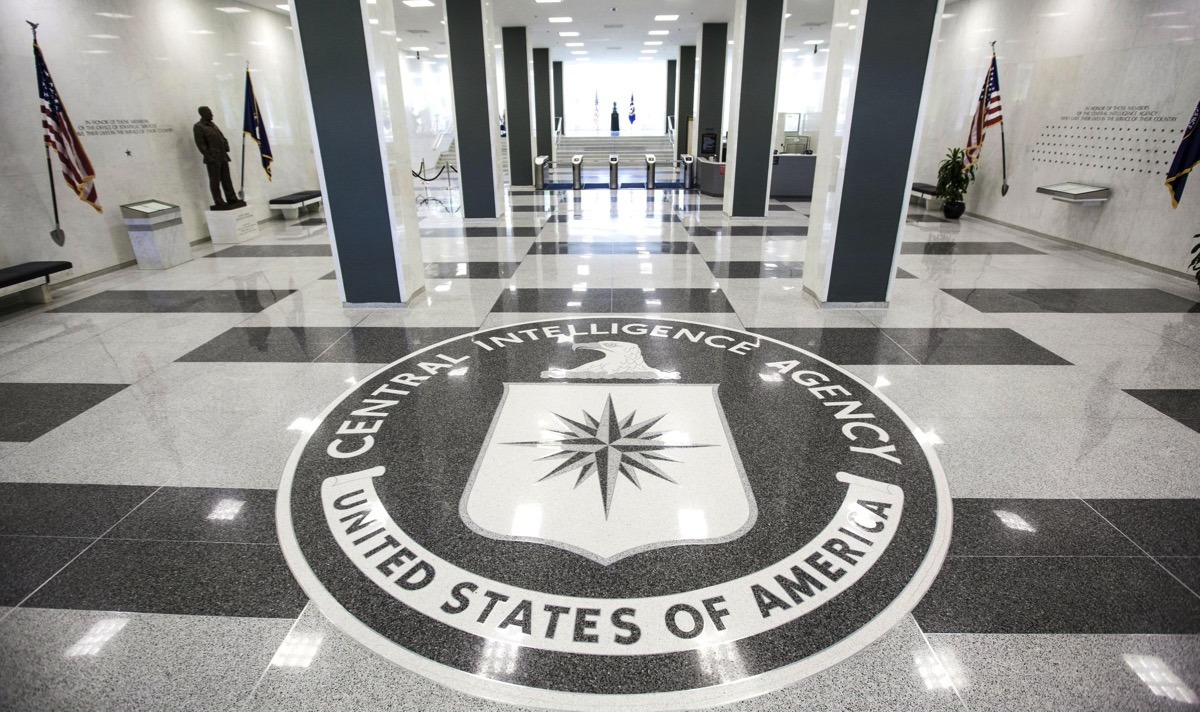
A new batch of 8,761 files was released on Tuesday by WikiLeaks that alleges that the U.S. Central Intelligence Agency has a dedicated iOS exploit team — and lacks the ability to keep the attack vectors under lock and key.
According to the latest document dump by WikiLeaks, the CIA's Center for Cyber Intelligence (CCI) responsible for computer intrusion methods has over 5000 members. The group has allegedly targeted more than 10,000 individuals world-wide, spanning iOS, Windows, and Android devices including smart televisions.
The CIA obtained the hacks by either purchasing them on the open market, or by sharing information with the FBI, NSA, or U.K. GCHQ. WikiLeaks also alleges that the CIA "lost control" of the code archive — which ultimately led to the release of the information to the group.
The "Vault 7" release covers 14 iOS exploits and penetration methods spanning iOS 4 through iOS 9.2, with some not requiring physical device access.
Overall, WikiLeaks claims that the Engineering Development Group inside the agency's CCI has produced more than 1000 hacking systems and "weaponized" malware. Reportedly, the codebase associated with the vectors is larger than Facebook's.
WikiLeaks has chosen to not distribute information on "armed" cyberweapons at this time until "a consensus emerges on the technical and political nature of the CIA's program and how such 'weapons' should analyzed, disarmed and published."
Other documents released in Tuesday's dump includes rules on how malware should be developed as to not point back to the CIA or U.S. government, how to avoid other nation's similar attempts, and how to exfiltrate mass amounts of data gathered in a successful attack.