A class action suit has been filed that accuses Apple's two-factor authentication of being too disruptive to users, taking too much time out of a user's day when it is needed, and abusive since it can't be rolled back to a less safe login method after 14 days.
The suit, filed by Jay Brodsky in California alleges that Apple doesn't get user consent to enable two-factor authentication. Furthermore, once enabled, two-factor authentication "imposes an extraneous logging in procedure that requires a user to both remember password; and have access to a trusted device or trusted phone number" when a device is enabled.
Filing paperwork associated with the suit also alleges that harm is being done, and potential class members "have been and continue to suffer harm" including economic losses, based on a waste of personal time for an extended login process that has become a multiple-step process.
The filer alleges that a software update enabled two factor authentication on or around September 2015. However, neither macOS El Capitan nor iOS 9 released in the timeframe put forth by the filer mandated two-factor authentication, nor implemented it without an explicit and multiple-step opt-in procedure requiring the user to consent. It is required to take advantage of some of Apple's services, like Home Sharing and HomeKit Hubs, however.
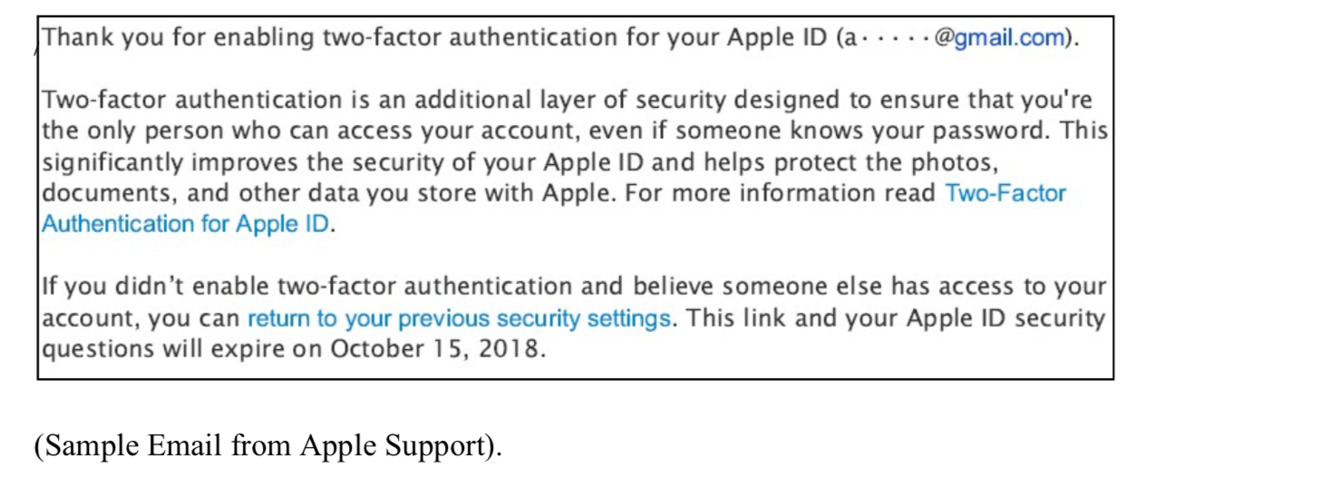
Brodsky alleges that the email that Apple sends after two-factor authentication is enabled is insufficient to warn the user that the setting is irrevocable. The filing calls a link in an email to a page to reset the configuration "unobtrusive" but does not specify what would have been sufficiently noticeable in a three-paragraph email.
According to the suit, when two-factor authentication is demanded, the process as follows takes between two and five minutes.
First, Plaintiff has to enter his selected password on the device he is interested in logging in. Second, Plaintiff has to enter password on another trusted device to login. Third, optionally, Plaintiff has to select a Trust or Don't Trust pop-up message response. Fourth, Plaintiff then has to wait to receive a six-digit verification code on that second device that is sent by an Apple Server on the internet. Finally, Plaintiff has to input the received six-digit verification code on the first device he is trying to log into. Each login process takes an additional estimated 2-5 or more minutes with 2FA."
AppleInsider hasn't been randomly presented with any two-factor authentications on Saturday even following OS updates to an iPhone XS Max, an iPhone X, and two sixth-generation iPads, but was able to force the issue on a new device. The process took 22 seconds in total to accomplish.
The filer believes that Apple has interfered with the use of the device with the "extraneous login process through two-factor authentication" that has been "imposed" on the class. The time it takes to execute the extra login data is said to be "continuous, systematic and ongoing" and Apple has "caused injury to Plaintiff and Class Members' rights to choose the level of security for Plaintiff and Class Member owned devices."
The suit is demanding injunctive relief, fines and penalties assessed on Apple in accordance with the Computer Fraud and Abuse Act, and is seeking "all funds, revenues, and benefits" that Apple has "unjustly received" from the action, but what precisely that entails isn't listed in the filing documents. The filer is also asserting that Apple is violating California's Invasion of Privacy act, but how that applies also isn't immediately clear.