Software vulnerability brokers have lowered payout rates for iOS exploits, saying a recent "flood" of iPhone zero-days makes the bugs less valuable than comparable attacks designed to penetrate Android.
Exploit reseller Zerodium on Tuesday announced higher going rates for Android vulnerabilities, with the firm now paying out up to $2.5 million for so-called zero-click zero-days, reports Motherboard.
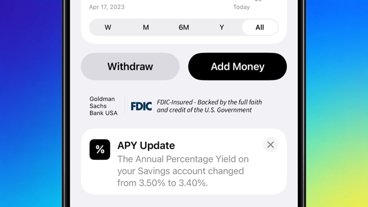
As the value of Android exploits increases, the market health of zero-days designed to thwart iOS protections stagnates due to what can be characterized as a supply glut. Zerodium, for example, pays out $2 million for zero-click vectors targeting iPhone, and decreased payouts for one-click attacks from $1.5 million to $1 million, the report said.
Zero-click exploits refer to vulnerabilities that can be leveraged to hack a device without user interaction, while zero-days are defined as bugs, exploits and other flaws that are as yet unknown to platform operators. Zero-days are particularly prized assets for hackers — both lawful and nefarious — looking to break into locked-down devices like iPhone.
"The zero-day market is flooded by iOS exploits, mostly Safari and iMessage chains, mainly due [to] a lot of security researchers having turned their focus into full time iOS exploitation," said Zerodium founder Chaouki Bekrar. "They've absolutely destroyed iOS security and mitigations. There are so many iOS exploits that we're starting to refuse some of them."
The director of exploit buyer Crowdfense, Andrea Zapparoli Manzoni, agrees with Bekrar's assessment of the market, but notes not all iOS chains are "intelligence-grade." Still, it appears the supply of vulnerabilities more than sates demand.
Bekrar added that Android is becoming increasingly difficult to crack, in part due to fragmentation. The multi-version, multi-device nature of Google's operating system has long been considered a weakness in terms of consistency and stability, but it is this very "feature" that might prove useful in protecting against widespread attack, the report said.
"Android is such a fragmented landscape that a 'universal chain' is almost impossible to find; much harder than on iOS which is a 'monoculture,'" said Zapparoli Manzoni.
Bekrar elaborated, saying Android's constantly improving security is making bug discovery more difficult for researchers. He seemingly implies Apple is not keeping pace with its iOS efforts.
"The security of Android is however improving with every new OS release. It's very hard and time consuming to develop full Android exploit chains and it's even harder for zero-click vectors (not requiring any user interaction)," Bekrar said. "We believe that the time has come to pay the highest bug bounty for Android exploits until Apple re-improves the security of iOS components such as Safari and iMessage."
As noted by Motherboard, brokers like Zerodium and Crowdfense comprise only a subsection of a much wider market dealing in software vulnerabilities. Other players include firms who broker deals solely with law enforcement and government agencies, regional research firms and rogue actors.
Zerodium's new bounty pricing arrives days after Google's Project Zero announced the discovery of a massive iPhone hacking operation. Over a period of what is thought to be years, a series of hacked websites took advantage of multiple vulnerabilities to disseminate a software implant capable of swiping sensitive user information and tracking the location of modern iPhones running the latest versions of iOS.
A follow-up report claimed the Chinese government used the hack to monitor Uyghur Muslims.