Security researchers have discovered a new malware for macOS, which can be used to attack over 100 browser extensions that may be installed on the target Mac.
Apple tries hard to make macOS and its other operating systems as secure as possible. While it does what it can to protect us from threats involving third-party malware, browser extensions are always a weak point.
Explained by Elastic Security Labs on Thursday, a malware dubbed Banshee Stealer doesn't directly attack macOS itself, but rather third-party software installed on it, reports Hacker News. This includes a wide range of browsers, including Safari, Chrome, Firefox, Brave, Edge, Vivaldi, Opera, and others.
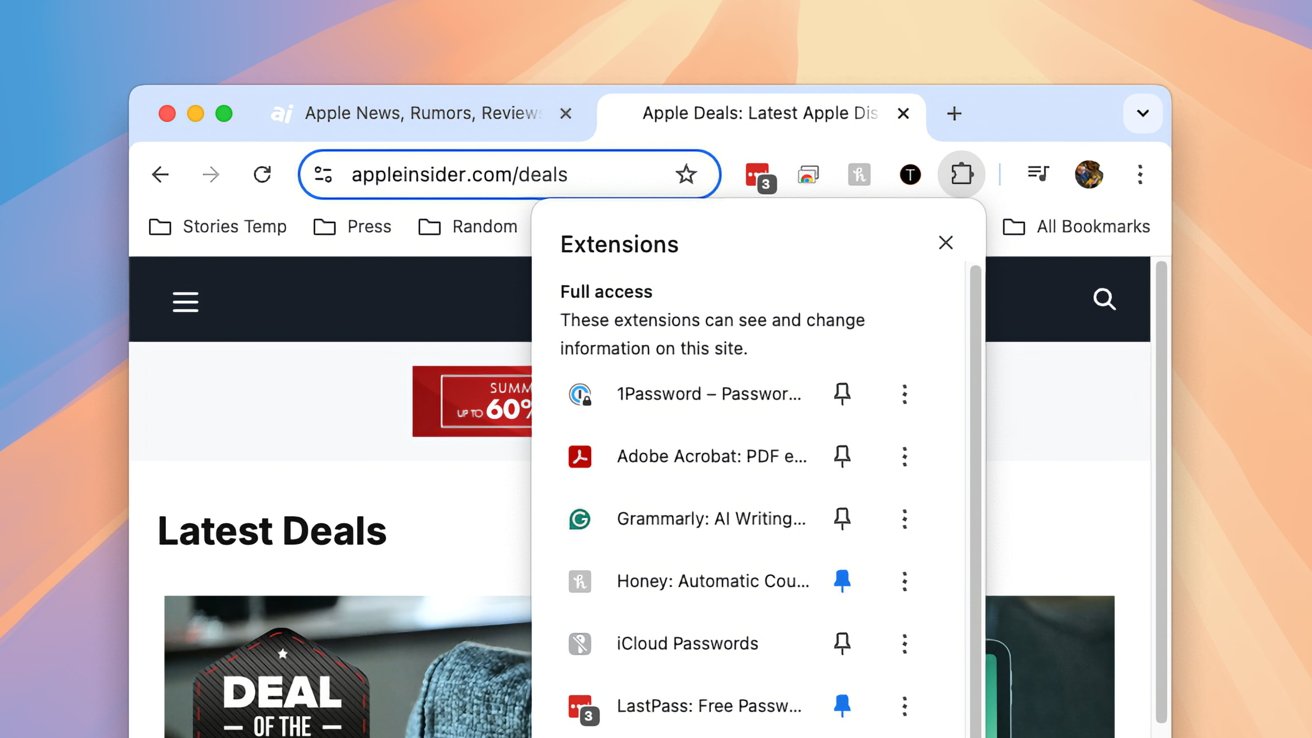
It also goes after cryptocurrency wallets and over 100 browser extensions installed onto said browsers. This makes it a "highly versatile and dangerous threat," said Elastic Security Labs.
The malware's primary task is to collect and steal data, and so it also has the ability to harvest information about the system itself, along with passwords from the Keychain. Data can also be pulled from a variety of file types stored on the desktop and document folders.
It also has capabilities to try and evade being detected in the first place. It can detect if it's running in a virtual environment, and also uses an API to avoid infecting Macs when Russian is the primary language.
During its installation, the malware makes use of a script to display a fake password prompt to the user, to try and escalate its privilege.
"As macOS increasingly becomes a prime target for cybercriminals, Banshee Stealer underscores the rising observance of macOS-specific malware," the researchers added.
It is unclear how widespread the malware has been used, but it seems that it is viewed as a high-quality tool for cybercriminals by its creator. In one forum screenshot, a seller of the tool has priced access to it at $3,000 per month.
To macOS users, there's no specific instructions to help this particular attack vector, other than good computing hygiene. Ensuring you know downloads come from legitimate sources, being wary about unexpected email attachments, and being more thoughtful about installations will take many users far.