Apple has been coy in revealing its plans for a touchless payment solution, but a patent filing discovered on Thursday gives clues as to where the company is headed.
Tech companies like Google are looking to streamline real world payments with so-called "e-wallet" solutions based on touchless technology like NFC. Despite a market heavily saturated with smart devices that would serve as optimal platforms for such systems, a clear frontrunner has yet to emerge.
While Apple is said to be working on a mobile payments solution, it has taken a "go slow" approach to the still nascent market. Over the past months, the company has been quietly laying groundwork for a possible reveal, however, first with Passbook, and more recently iBeacon. At this point, the endgame is unknown, but a patent filing discovered today may play a role in Apple's grand design.
The U.S. Patent and Trademark Office published Apple's application for a "Method to send payment data through various air interfaces without compromising user data," which details a readily deployable digital system based on existing mobile hardware technology. Prior to today's filing, most of Apple's payment-minded patents have focused on use case scenarios, not backend infrastructure.
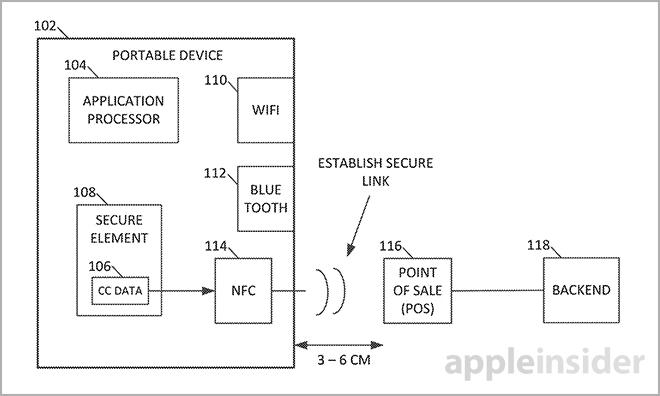
The patent language notes that the invention covers a commercial transaction method in which a purchasing device, such as an iPhone, finds and establishes a secure connection to a point of sale system via a first wireless interface. Following link up, the device identifies a second, different wireless interface to connect to a backend server for transaction completion.
According to the document summary, the first secure connection can be accomplished via near-field communications modules — or like technology — and is provided to initiate the sales process. Here, NFC is used as an example and the patent points out that other wireless protocols can be used as necessary. In addition, the invention notes that a "bump" may be used to start the connection sequence.
It should be noted that Apple has shown more interest in Bluetooth than NFC, especially given the introduction of iBeacon technology, which rolled out in Apple Stores across the U.S. in December. Based on the Bluetooth Low Energy protocol, iBeacon has the potential to combine the benefits of NFC's limited proximity operation with increased range if needed. Bandwidth is also higher than NFC, allowing for more complex security implementations and data transfer.
Because holding a phone next to a cash register may be uncomfortable, a second more robust wireless interface is used to complete the transaction.
Along with Wi-Fi, the patent application names Bluetooth as a candidate wireless protocol for the second secure link with a store's backend server. This secondary connection does the heavy lifting in Apple's invention, including credit card handling, transfer of cryptogrphical data and user verification.
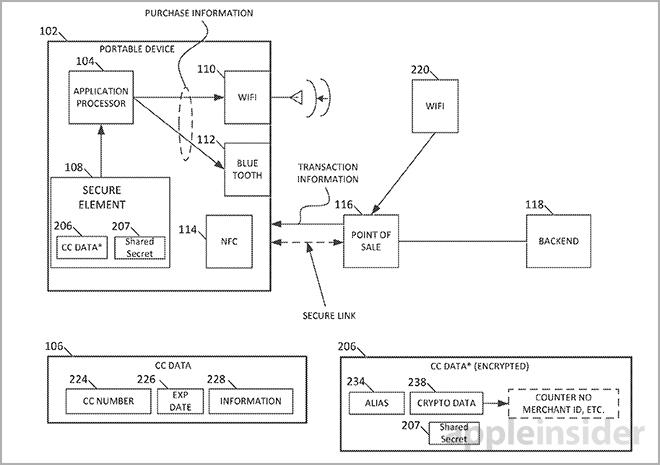
Passing sensitive credit card information stored on board a device through to a POS or backend server is dangerous as rogue apps may steal the data as it moves through the applications processor. Instead, the invention calls on a "secure element" located on-board a device to generate an alias for customer account information, which is then sent to the server along with a shared secret, or crypto key.
Mentioned multiple times in the patent language, the "secure element" appears to operate in a similar fashion as the "secure enclave" found in the iPhone 5s' A7 system-on-a-chip. In its current form, the enclave serves to protect Touch ID fingerprint data from snooping apps, but the system could potentially be used to safeguard payment information as well. As it is, both the patent and the existing secure enclave create aliases for outgoing data.
Once the alias is received at the backend server, it is verified by crypto data. Examples of viable secure solutions include a digitally-signed combination of one or more aliases, random numbers, merchant identifiers or other values.
To verify that the alias and crypto data match, the purchase device and server may communicate a shared secret. A shared secret can be a symmetric key stored in the secure element when the device is manufactured, then transmitted to the server backend behind a secure firewall. Another example is a specific counter value known independently on the device and server.
When a transaction request is received at the server, it generates crypto data from its own version of the shared secret and compares it to the crypto data sent over by the purchasing device to confirm the alias. If a match is found, the transaction is allowed to go through. In the case of a no-match, the transaction is cancelled and the wireless connection is terminated.
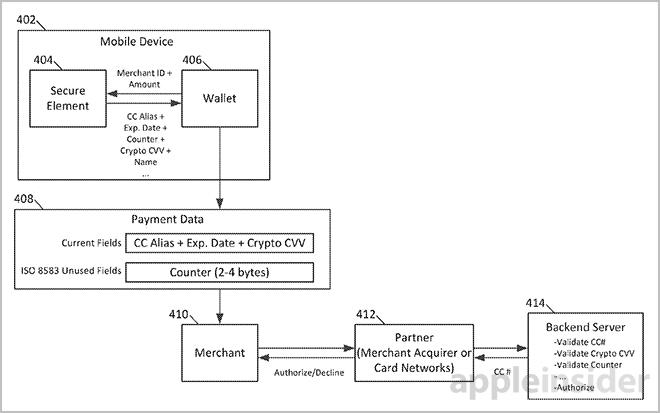
A simplification of the process is as follows: A purchase device initiates a transaction with a POS device via a close-proximity wireless protocol like iBeacon or NFC. The phone then sniffs out and connects to the server backend via a second wireless protocol, sending an alias for credit card information alongside a crypto key generated from a shared secret. These sensitive assets are stored in a secure element on the phone. On the server end, the backend generates a crypto key based on the shared secret and compares it with the data provided by the phone. If everything matches, the transaction is a go.
At this point, it is unclear if Apple will ever institute the above described system in a payments solution, though the company's most recent hardware and software advancements do point in that general direction.
It can be speculated that users may one day be able to use Touch ID to complete transactions by accessing credit card or banking information stored in an on-board secure enclave. Of course, merchants would have to agree to modifications to POS and backend systems for the solution to work. From what can be gathered by early iBeacon adoption, however, it appears that retailers may be ready for an Apple-made answer to mobile payments.
Apple's wireless interface payment patent application was first filed for in 2012 and credits Ahmer A. Khan, Brian J. Tucker, David T. Haggerty and Scott M. Herz as its inventors.