The firm says that Java, which can be used to write standalone applications that run across multiple platforms or applets that are embedded in web pages, has a serious flaw that could allow local code on a user's Mac to be executed remotely.
"This can lead to 'drive-by attacks,' where users are attacked simply by visiting a malicious web site and loading a web page," the firm said.
The exploit could allow a third-party to execute code, access or delete files, or run applications on the compromised machine. Combined with other exploits, hackers could even potentially run system-level processes and gain total access over the affected Mac.
Since the vulnerability relies solely on Java, with no native code required, it theoretically exists in all browsers on all platforms that have not been patched. This is the case with Mac OS X 10.5.7 and earlier, meaning the vulnerability affects even the update released just a week ago.
The firm claims that Apple has been aware of the exploit for at least five months, when it was publicly disclosed and fixed by Sun, but has yet to issue a security patch. It was first discovered by Landon Fuller, who has released a proof of concept exemplifying the security hole.
Intego says it has not found any malicious applets in the wild thus far, but the publicity around this vulnerability may entice hackers to target the exploit before Apple issues a security update. The firm's VirusBarrier X5 already blocks potential malware but unless users are sure they trust the site they're viewing, simply disabling Java in the browser may provide the best protection while Apple works on a fix.
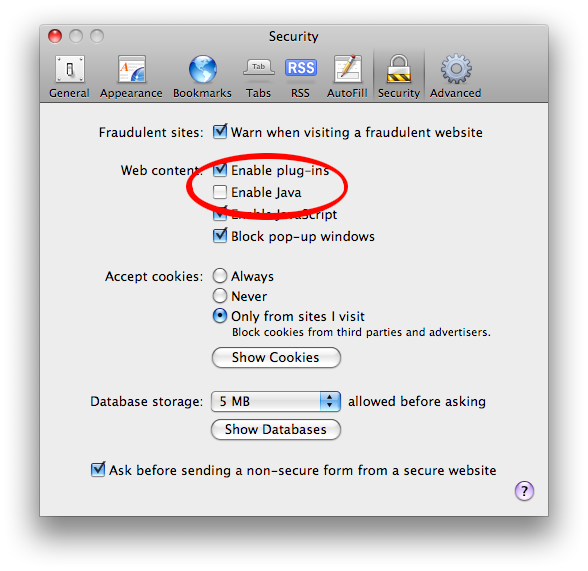
To do this, launch Safari, choose Safari > Preferences, click the Security tab, and uncheck Enable Java if it is checked. In Firefox, this setting is found on the Content tab of the program’s preferences. It is safe to leave JavaScript activated, since the vulnerability only affects Java applets.