A report on Monday suggests Apple's recently modified OS X app signing policy is the result of an undisclosed Developer Portal security breach that leaked keys for multiple services, including Gatekeeper.
Noting tweets by user @SomeoneSW and one corroborating source, TUAW claims Apple's newly instituted policy forcing developers to re-sign app credentials is the result of a security breach that not only released Gatekeeper keys, but also "many other keys for many other things."
As seen in the tweets embedded below, @SomeoneSW, whose account was seemingly created today, claims inside knowledge of a data breach that released "virtually every key Apple used for anything." The Twitter user said they were approached with a proposal to buy said keys shortly after the undisclosed theft.
Apple could not be reached for comment on the issue.
@marczak @cabel @danielpunkass @mikeash The keys used for Gatekeeper* were stolen in that Developer Portal breach a while back. Consider thi
— Somebody Somewhere (@SomebodySW) August 18, 2014@marczak @cabel @danielpunkass @mikeash s your heads up. *and many other keys for many other things
— Somebody Somewhere (@SomebodySW) August 18, 2014According to the publication, also pilfered was Apple's Enterprise Signing Key, an asset used to sign activation tickets for bypassing iCloud locks. This particular key was used in a previously reported iCloud exploit that supposedly allowed hackers to defeat Activation Lock, the anonymous Twitter user said.
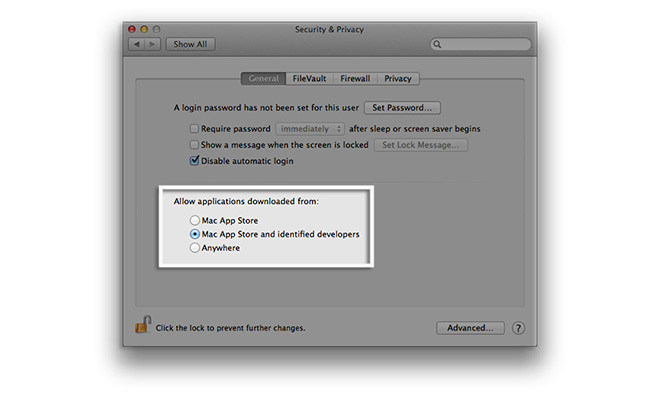
Gatekeeper is a security tool first offered in OS X 10.8 Mountain Lion that protects users from malicious software by placing restrictions on app installation. At its default setting, for example, Gatekeeper allows installation of apps from the Mac App Store and titles signed by developers who have registered through company's Developer ID Program.
The supposed Developer Portal breach would technically let nefarious users sign malicious apps as kosher, prompting Apple to change the way apps are recognized by Gatekeeper in OS X 10.9.5 Mavericks and the upcoming OS X 10.10 Yosemite.