Among the privacy policies outlined by Apple in a new privacy policy webpage on Wednesday is an iOS 8 feature that makes it technically impossible for the company to decrypt a device to harvest user data, even if law enforcement agencies request it.
As noted by The Washington Post, iOS 8 marks a new, more aggressive stance in protecting customer data from prying eyes, as Apple engineered an encryption system even it is unable to break.
In a document (PDF link) meant to guide law enforcement officers in requesting user information, Apple notes that it no longer stores encryption keys for devices with iOS 8, meaning agencies are unable to gain access even with a valid search warrant. This includes data store on a physical device protected by a passcode, including photos, call history, contacts and more.
"Unlike our competitors, Apple cannot bypass your passcode and therefore cannot access this data," Apple said on its new webpage dedicated to privacy policies. "So it's not technically feasible for us to respond to government warrants for the extraction of this data from devices in their possession running iOS 8."
The safeguards do not apply to other services including iCloud, however, meaning any data stored offsite is fair game for government seizure. Still, the security implementation will likely be seen as a step in the right direction, especially given the current political climate following revelations of governmental "snooping" activities.
In an open letter to consumers posted on Apple's new privacy policies webpage, CEO Tim Cook reaffirmed the company's stance on personal data, saying the company does not allow server backdoors and only handles with legitimate requests backed by the proper authorities.
"I want to be absolutely clear that we have never worked with any government agency from any country to create a backdoor in any of our products or services," Cook wrote, adding, "We have also never allowed access to our servers. And we never will."
 AppleInsider Staff
AppleInsider Staff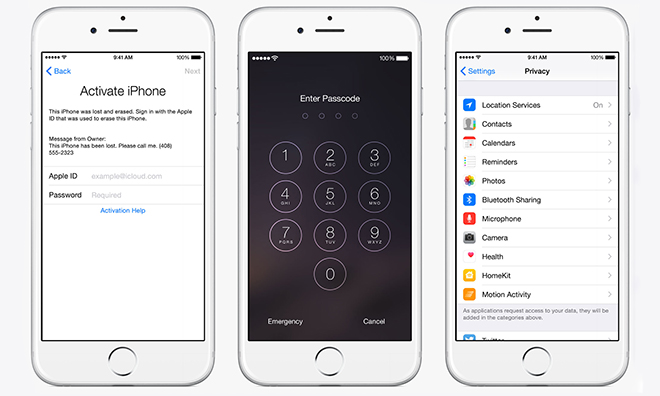








 Charles Martin
Charles Martin
 Christine McKee
Christine McKee
 Wesley Hilliard
Wesley Hilliard
 Malcolm Owen
Malcolm Owen
 Andrew Orr
Andrew Orr
 William Gallagher
William Gallagher
 Sponsored Content
Sponsored Content








87 Comments
THis is an awesome claim Android will never be able to make.
[quote name="AppleInsider" url="/t/182357/apple-says-incapable-of-decrypting-ios-8-user-data-even-for-government-agencies#post_2601066"] The safeguards do not apply to other services including iCloud, however, meaning any data stored offsite is fair game for government seizure. Still, the security implementation will likely be seen as a step in the right direction, especially given the current political climate surrounding government "snooping."[/quote] What about iCloud backups?
A little disingenuous of Cook since almost all of this data is duplicated in iCloud, that is within the government's reach.
Cool, iOS 8, the system for terrorists!
[quote name="iaeen" url="/t/182357/apple-says-incapable-of-decrypting-ios-8-user-data-even-for-government-agencies#post_2601075"] What about iCloud backups?[/quote] Did you bother to read the story?