A recently-discovered vulnerability in Apple's mobile operating system could allow attackers to trick users into replacing legitimate apps that have access to a variety of personal information — Â such as banking apps — Â with hacked versions that relay that information to malicious actors.
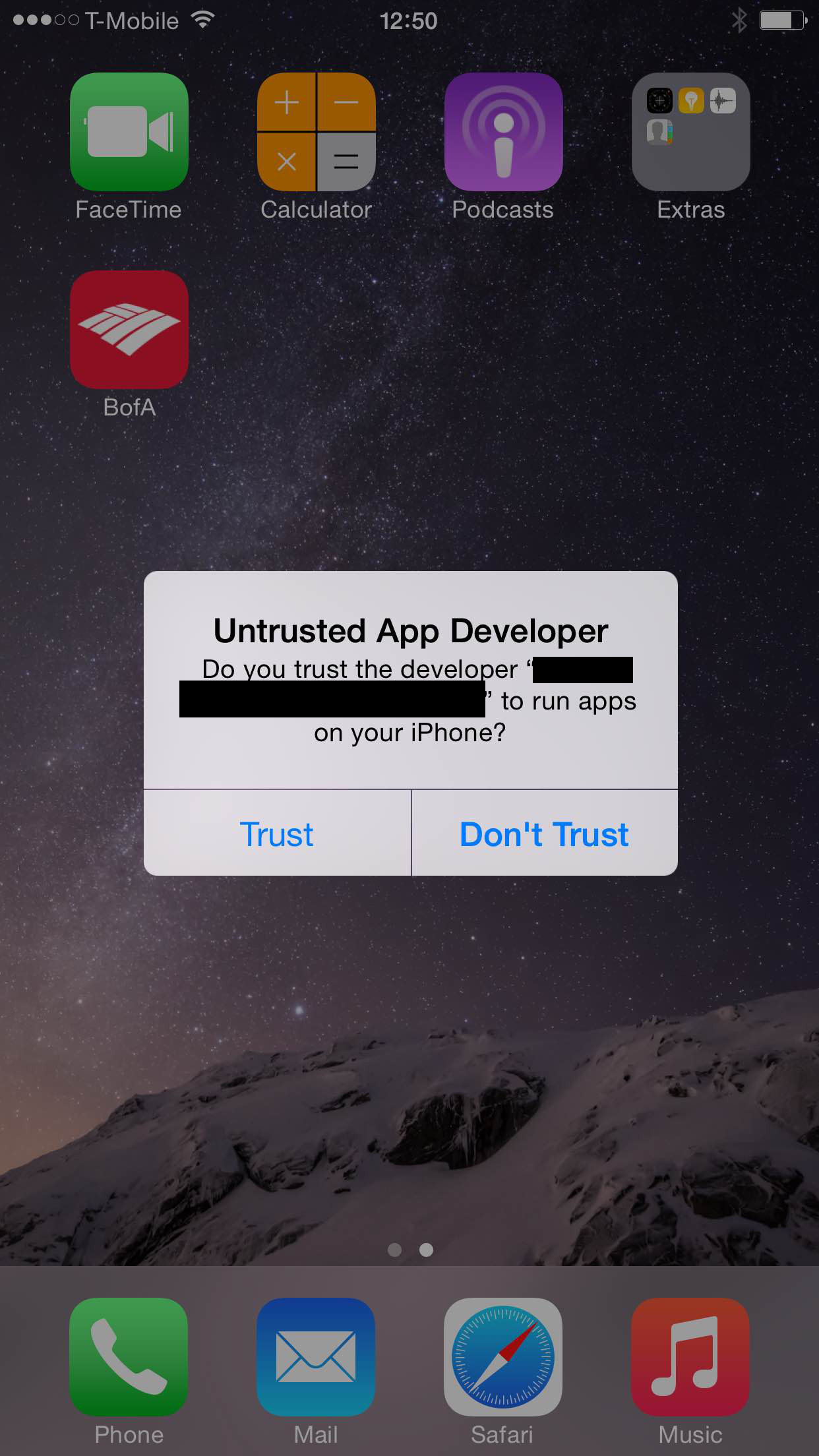
Hacked apps could be distributed via email or through web links and installed using iOS's enterprise provisioning system, which allows apps to be added to the device from outside of the App Store. The vulnerability, dubbed a "Masque attack" by security firm FireEye, is possible because iOS does not verify that the code signing certificate is the same for apps that use the same bundle identifier.
An app with the same bundle identifier as Bank of America's mobile banking, for example, could be installed over top of the legitimate Bank of America app, mimicking the latter's user interface but sending login data back to the attackers' servers. Default apps like Safari and Mail are not affected.
FireEye notified Apple of the issue on July 26, but iOS versions up to and including iOS 8.1.1. beta continue to be vulnerable. Apple has yet to respond to the public disclosure.
The Masque attack could be considered an advanced form of phishing, a social engineering attack usually propagated via email in which users are tricked into submitting sensitive information to real-looking but ultimately fake websites. Phishing continues to be a huge problem, despite special protections built into web browsers and email clients designed to thwart the attack.