A long-known flaw in Safari's implementation of private browsing that saves the address of each and every website users visit to a file on their local drive, even after closing private browsing windows and quitting Safari, is still present in the latest pre-release versions of OS X Yosemite.
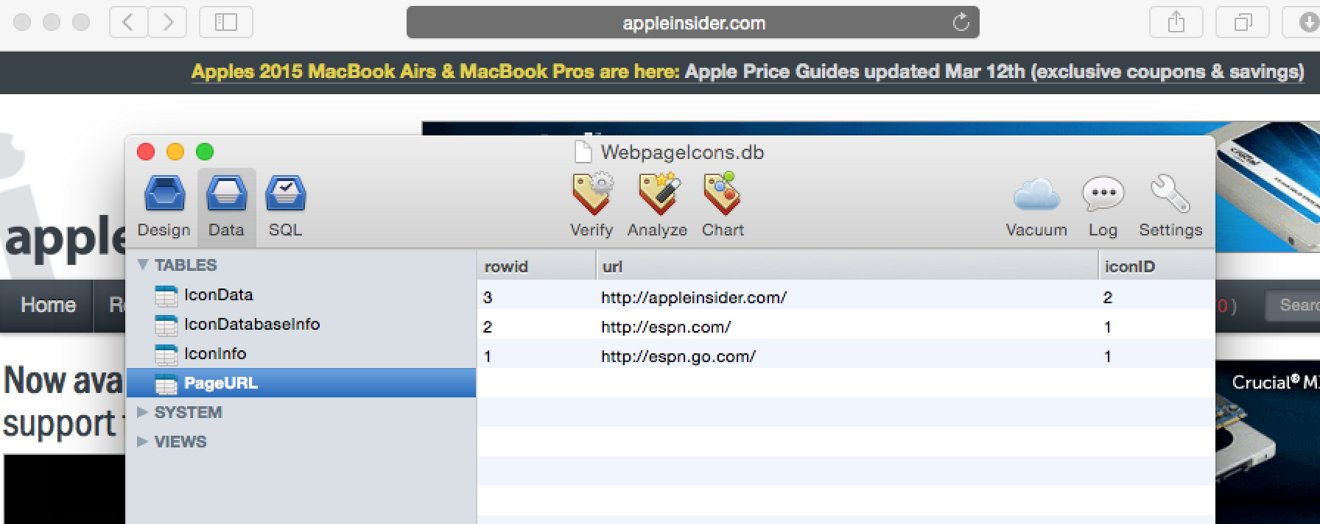
The bug manifests itself as part of Safari's cache mechanism for favicons, the small pictures that appear beside web addresses in the URL bar, bookmarks, and the favorites view. The favicon and accompanying web address for every visited site — Â including those opened in a private browsing window — Â are stored in an SQLite database within the user's home folder.
This database, located at ~/Library/Safari/WebpageIcons.db, is not encrypted or obfuscated in any manner.
Issues with improper data retention in Safari's favicon database have been known for years, but were pointed out again by AppleInsider reader @tylerc on Friday. A 2013 article on forensic browser analysis published in the EURASIP Journal on Information Security found that "the easiest way to view the browsing history for Safari private browsing sessions was to locate the 'WebpageIcons' database under Safari artifacts."
"This database provided a good log of every visited URL along with other pertinent information," authors Donny J Ohana and Narasimha Shashidhar concluded.
Tests conducted by AppleInsider on OS X Yosemite 10.10.3 build 14D98g, released to developers earlier this week, confirm that the flaw remains unaddressed. Trashing the WebpageIcons.db file, re-launching Safari, and visiting a web page in private browsing mode logs that visit to the database, and the data persists following a browser reboot.
The relatively easy accessibility of this information could pose problems not just for users whose computers have been compromised by malware or other targeted attacks, but even for those who share their computer with friends or significant others. By reading the database, an operation trivially performed with any of a variety of easy-to-obtain tools, information that users thought was safe could be extracted and used against them.
Until the problem is addressed, users can clear the data held in WebpageIcons.db manually by using the "Clear History and Website Data..." dialog found in the Safari menu, or by dragging the ~/Library/Safari/WebpageIcons.db file to the trash, forcing Safari to recreate it.