A relatively new $300 device could allow attackers to crack the PIN codes on out-of-date iPhones or iPads, taking advantage of a flaw in iOS versions older than 8.1.1 that allows unlimited attempts at PIN entry, even when users enable Apple's 10-try limit.
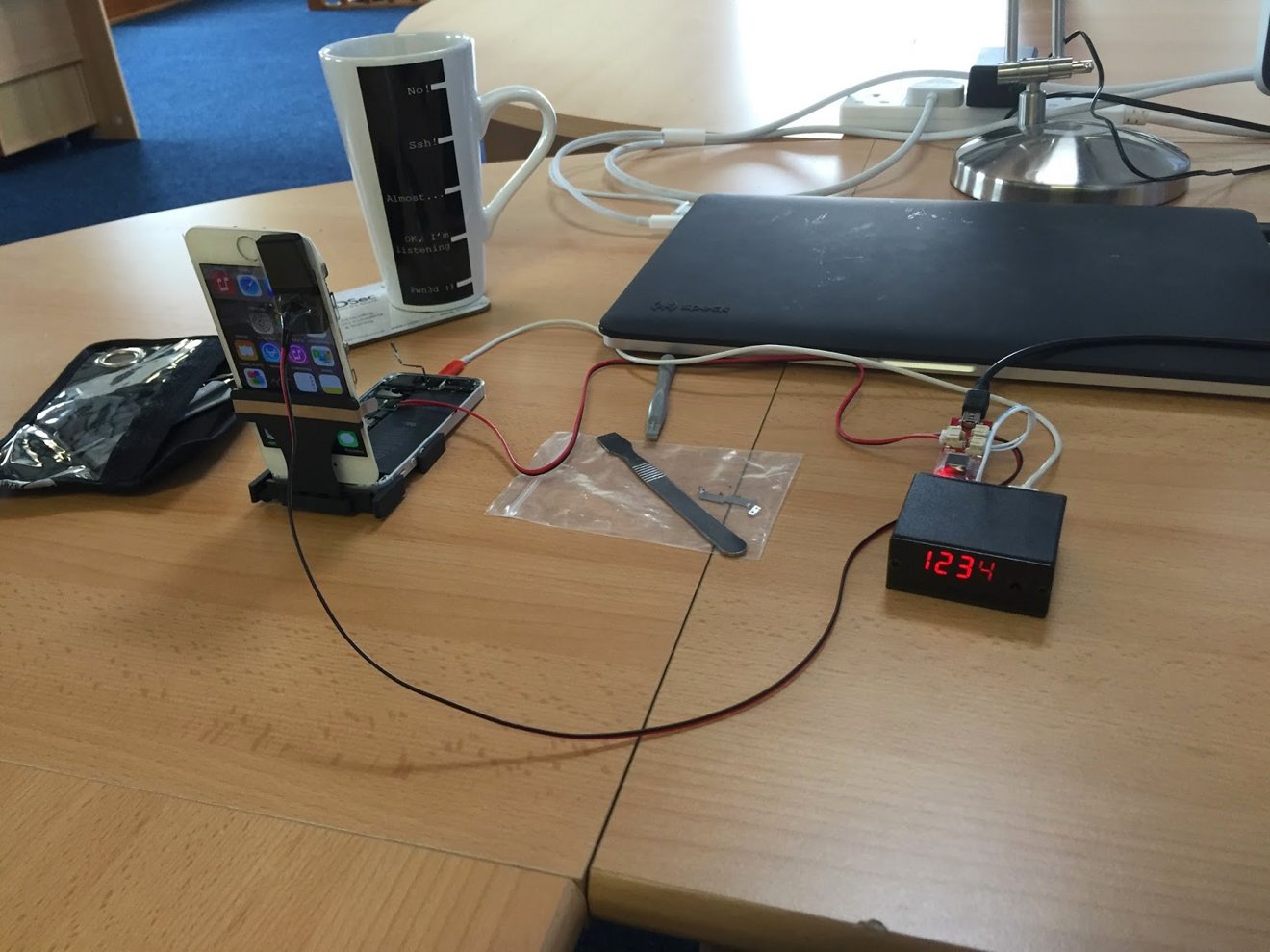
The so-called "IP Box" tested by security consultancy MDSec works by entering a PIN over USB, then immediately cutting power to the iOS device before the attempt is recorded. This has the effect of eliminating the 10-try limit, at the expense of significant time lost to iOS device reboots.
MDSec places the time per attempt at nearly 40 seconds. While this long interval may seem likely to discourage brute force attempts in all but a few scenarios, research suggests that more than 25 percent of the population use one of 20 similar PINs, potentially cutting the mean time to crack a PIN down to minutes.
Additionally, such tools are readily available over the internet, with some models costing as little as $175.
As the firm notes, this appears to be an automated method to exploit a flaw described last November in CVE-2014-4451. Apple patched that bug in iOS 8.1.1, but older iOS versions remain vulnerable.
Users running unpatched versions of iOS are advised to move to a more complex passcode to mitigate the danger from similar attacks. This can be done by navigating to Settings → Passcode and turning off "Simple Passcode," which will allow the selection of a longer alphanumeric code.