Apple on Friday commented on the discovery of so-called cross-app resource access (XARA) exploits, saying it rolled out a server-side security update earlier this week and is currently working with researchers on additional fixes.
In a statement provided to iMore, Apple confirmed knowledge of XARA vulnerabilities and the potential exploits they enable through malicious software on OS X and iOS. Downloaded malware, or nefarious URL schemes, intercepts data being transferred between sandboxed apps, including sensitive information like passwords and authentication keys.
"Earlier this week we implemented a server-side app security update that secures app data and blocks apps with sandbox configuration issues from the Mac App Store. We have additional fixes in progress and are working with the researchers to investigate the claims in their paper," an Apple spokesman said.
The vulnerabilities were discovered last year by a team of researchers working out of Indiana University, Georgia Tech and China's Peking University, who subsequently informed Apple of their findings last October. Apple requested details of the exploits be withheld from publication for six months.
As explained in the group's research paper, which was published this week, malicious apps take advantage of flaws in the way OS X and iOS move and store inter-app data. In the case of OS X, malware downloaded from the App Store is able to access and modify the Keychain database and Bundle IDs, the latter of which are used as a form of access control. Other attacks involve WebSockets and URL schemes.
While the threat is very real, some news outlets have perhaps overhyped XARA's danger, iMore says. In order to implement a fix, however, both Apple and developers need to rework data handling methods with more stringent protocols.
 AppleInsider Staff
AppleInsider Staff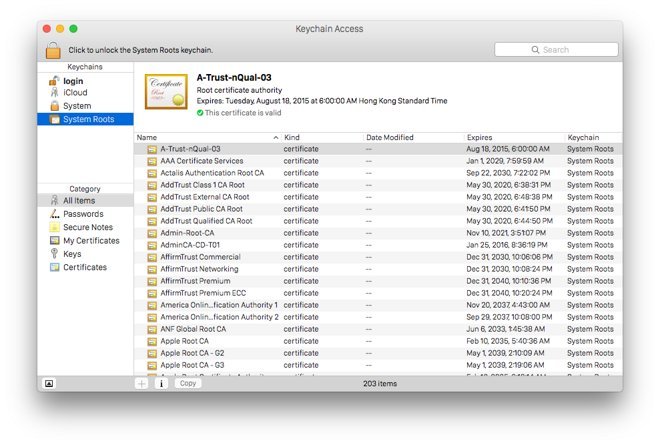








 Wesley Hilliard
Wesley Hilliard
 Marko Zivkovic
Marko Zivkovic
 Andrew O'Hara
Andrew O'Hara
 Christine McKee
Christine McKee


 Amber Neely
Amber Neely
 Malcolm Owen
Malcolm Owen






31 Comments
Perhaps overhyped? They've blasted it everywhere. The Flipboard resident trolls have had a field week.
[quote name="TheWhiteFalcon" url="/t/186842/apple-addresses-xara-vulnerabilities-says-fixes-on-the-way#post_2737860"]Perhaps overhyped? They've blasted it everywhere. The Flipboard resident trolls have had a field week.[/quote] They need something to jerk off about.
Apple is so doomed, it's already dead. The media just hasn't picked up the story yet. Apple, Inc 1976-2015. May you rest in eternal doom.
It affects Android too.... your turn Google.
Dag Nabbit! They got me again! Every year I fall for ONE Apple Security Apocalypse story, and think "this is it--the big one." It never is. But they up their game every year, hyping harder and obscuring the details just to fool me one more time... But even so, if this is just "another little one" (possibly affecting zero users), it's still important to catch and fix the issues.