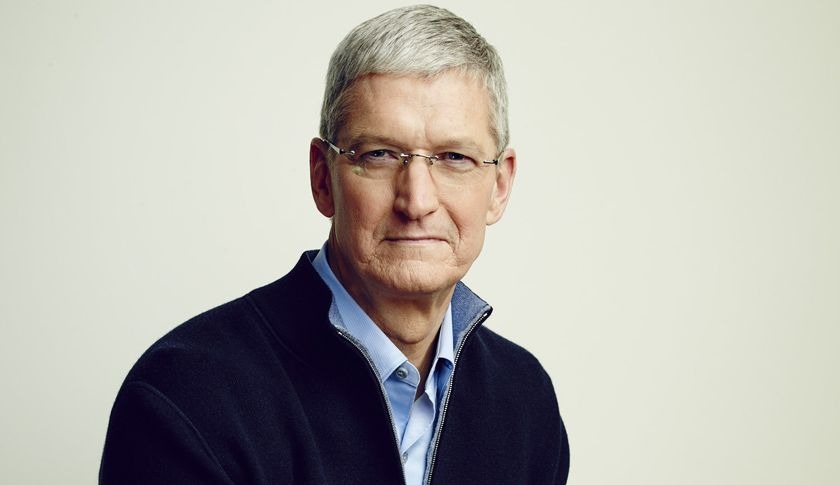
The resolute position of Apple's chief executive Tim Cook to defend the security of iOS encryption has drawn a sharp contrast with the deafening silence from Google, Microsoft and their hardware partners in Korea and China, where individuals' security and privacy are commonly overlooked as being a critical feature.
Apple standing alone for encryption and user privacy
Cook published a public letter stating that "we have done everything that is both within our power and within the law to help" the U.S. Federal Bureau of Investigations to recover data from an iPhone left behind by a terrorist involved in the San Bernardino shootings.
However, he opposed an order from a Federal court that "demanded that Apple take an unprecedented step which threatens the security of our customers."
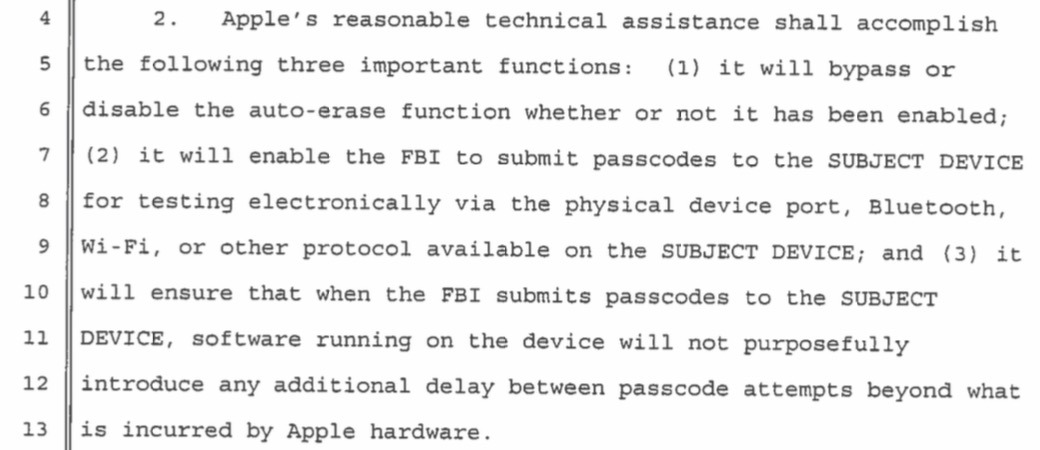
That order requests that Apple develop a new version of iOS capable of allowing law enforcement to bypass key security settings in order to rapidly "brute force" a series of password guesses to unlock its encryption. Among other things, this would erase the time delays between false password attempts and allow for automated, electronic submission of a string of potential passwords rather than requiring that each be keyed in manually by a real person.
"Once the information is known, or a way to bypass the code is revealed, the encryption can be defeated by anyone with that knowledge," Cook stated, adding, "The government suggests this tool could only be used once, on one phone. But that's simply not true."
Cook stated that "in the wrong hands, this software — which does not exist today — would have the potential to unlock any iPhone in someone's physical possession."
"Apple employees should feel incredibly proud today"
Earlier today, WhiteHat Security founder Jeremiah Grossman tweeted, "if Apple 'technically' could comply, yet they still resist, it says even more good things about the Tim Cook and company character," adding, "Apple employees should feel incredibly proud today."
"Apple is nearly unique of tech firms in it's high profile, has revenue that don't rely on compromising privacy... " https://t.co/F7IIlb4shL
— Jeremiah Grossman (@jeremiahg) February 17, 2016
"How do Apple shareholders feel today? Does their fierce protection of customer security & privacy drive extra iPhone sales? I hope so," he added, followed by, "And don't GOV officials also use iPhones themselves? Did they think through that they'd also undermine the security of their own devices?"
He also drew a contrast between Apple's high profile pushback to maintain the security of its encryption with other companies. "Today would be the perfect day for Sundar Pichai (Google, CEO) to back up Tim Cook (Apple, CEO)," he noted.
Google says nothing
Google declined to comment on the issue in a USA Today article written by Jessica Guynn, which cited Former National Security Agency contractor Edward Snowden as stating, "The FBI is creating a world where citizens rely on Apple to defend their rights, rather than the other way around.""Silence means Google picked a side, but it's not the public's" - Edward Snowden
Snowden called the issue "the most important tech case in a decade," and specifically pointed out that, "Silence means Google picked a side, but it's not the public's."
Guynn also cited WhatsApp founder and Facebook board member Jan Koum, who posted on Facebook: "I have always admired Tim Cook for his stance on privacy and Apple's efforts to protect user data and couldn't agree more with everything said in their Customer Letter today. We must not allow this dangerous precedent to be set. Today our freedom and our liberty is at stake."
Update: Google's chief executive Sundar Pichai just issued four tweets later in the day recognizing the "important post" from Cook and stating, "forcing companies to enable hacking could compromise users' privacy."
Pichai added, "We know that law enforcement and intelligence agencies face significant challenges in protecting the public against crime and terrorism. We build secure products to keep your information safe and we give law enforcement access to data based on valid legal orders. But that's wholly different than requiring companies to enable hacking of customer devices & data. Could be a troubling precedent."
Several users on Twitter took issue with Pichai's phasing "could be," one emphasizing, "Could be a troubling precedent? No, it IS a troubling precedent. Your position is troubling bc your statement is lukewarm."
Security is a key issue for Apple
While Google's chairman Eric Schmidt boasted to the media in 2014 that "our systems are far more secure and encrypted than anyone else, including Apple," groups that take privacy and security seriously, like the Electronic Frontier Foundation, have recommended Apple's messaging products for their end-to-end encryption while cautioning that Google did not provide similar security for its users.
Last November, Chris Soghioan, the principal technologist for the American Civil Liberties Union, went even further to state that Apple's efforts to protect the privacy of its users, including end-to-end encryption of their communications, effectively separated its more affluent iOS users from the poor and disadvantaged forced to use Android.
"The security people I know at Google are embarrassed by Android," Soghioan noted.
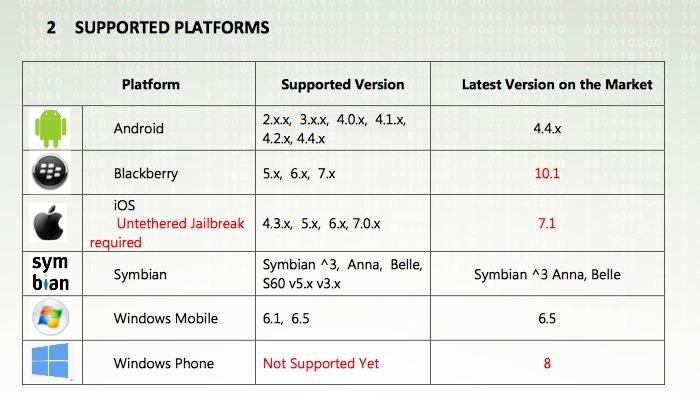
Both Android devices and Windows PCs have a wide variety of over the counter spyware tools and privacy exploits that are easy for even amateurs to find, while even tools sold to law enforcement (including FinSpy, above, from global surveillance firm Gamma Group) note that they won't work on iPhones and other iOS devices unless their security has been jailbroken by the user.
Without any commercial interest in collecting user data for marketing purposes, Apple is in a unique position to defend user privacy and security. While both Google and Microsoft have made headlines for their lax efforts to protect user data on their Android and Windows platforms, their licensees have gone even further. Last year, China's Lenovo— the largest producer of both Windows PCs and Android smartphones — bundled Superfish adware on some of its products using a self-signed root certificate, without considering that this practice opened up its users to having their encrypted communications being intercepted.
Security firm Bluebox Labs found that virtually all of the discount Android tablets sold by from major retailers including Amazon, Best Buy, Kmart, Kohl's, Staples, Target and Walmart similarly shipped with "shocking" security flaws, malware and even active backdoors installed to spy on users.
FBI's request will likely be replicated by Communist, Islamic states
Apple now sells most of its products outside the U.S. That means if it were to allow the FBI to demand a security bypass that effectively destroyed iOS security, it would also face similar pressures in the U.K., Saudi Arabia, and of course the People's Republic of China, now Apple's largest sales territory. The company is also working to establish a sales presence in Iran.
The New York Times: @FBI's war on #Apple will aid China. https://t.co/URWamc702q pic.twitter.com/KnHDsWIENY
— Edward Snowden (@Snowden) February 17, 2016
If the U.S. can demand that Apple tear down its entire security system to facilitate an investigation to see whether a single phone might have some potentially useful data on it, it won't be long before every country on earth demands access to this same software tool in order to hunt down their own enemies, many of whom might be Americans, or even members of the FBI or NSA.
Those are all issues Apple considers, because unlike Google, it earns significant profits in China and has a long term strategy that doesn't get rebooted every year after failing to make any progress.
U.S. Government and data security
While the FBI continues to insist that Apple could write a security-free version of iOS for use in investigating just the one phone involved in this case, somehow without spreading to malicious actors or repressive foreign governments that may use this tool against the U.S. itself, the government's track record in securing or even caring about citizens' privacy, making reasonable use of user data, and safeguarding the private data of individuals it collects— and even of its own FBI employees— is atrociously incompetent.
Just last summer, the U.S. government suffered a "colossal breach of government computer systems" that exposed sensitive information, including the fingerprints, health and financial history of 19.7 million people who had subjected themselves to government background checks. That came just weeks after data on 4.2 million federal employees had earlier been compromised, as noted by a report in the New York Times.
"Both attacks are believed to have originated in China," the report stated, citing senior administration officials.
Members of the U.S. Congress have so little confidence in their own government's ability to hold detainees under arrest that they signed a law preventing the Obama Administration from transferring "Guantanamo Bay detainees to the United States for any reason, including prosecution."
If the government can't be trusted to lock up individuals on U.S. soil in maximum security prisons, how can it expect to guarantee that it can somehow safeguard a far more commercially valuable software mechanism capable of exploiting encrypted data stored on the only secure mobile platform left?