According to a court filing prepared by Apple, the company first received — and responded to — FBI requests for information related to last year's deadly shootings in San Bernardino, Calif., just three days after the attack.
As noted in the declaration of Lisa Olle, manager of Apple's Global Privacy & Law Enforcement Compliance Team, law enforcement officials contacted the company's 24-hour emergency call center on the afternoon of Dec. 5, three days after Syed Rizwan Farook and his wife Tashfeen Malik killed 14 people in a self-proclaimed act of terrorism. Farook's iPhone 5c now sits at the heart of a contentious debate between privacy advocates and national security hawks.
The information sheds new light on Apple's efforts to cooperate with FBI investigatory operations prior to being served a federal court order compelling assistance in breaking into Farook's iPhone. It was previously learned that by early January Apple was in regular discussions with government officials over how best to extract the phone's data, though information stored on Apple's end was apparently provided weeks earlier.
On Dec. 5, Apple handed over two parcels of information after receiving legal notice seeking subscriber information (likely iCloud subscriber data, though it's not specified in Olle's declaration) attached to three names and nine specific accounts. A day later, Apple received a search warrant for emails, messages and other information associated with three separate accounts. Another request on Dec. 16 sought information related to one name and seven different accounts. Apple was able to provide same-day turnaround on each of the three requests.
As for the iCloud account attached to Farook's iPhone, Olle states the official search warrant was served on Jan. 22 seeking the same communications and customer information requested in December. Apple complied and on Jan. 26 provided the government with whatever data it had in its possession.
It was later revealed that the FBI ordered the San Bernardino County Department of Health, Farook's former employer and owner of the iPhone 5c in question, to reset the associated Apple ID password on Dec. 6 without first consulting Apple. Company representatives, including CEO Tim Cook, said the move was a misstep as it nullified the possibility of using iCloud's automatic sync feature to procure a backup without unlocking the device.
It appears Olle was part of the team responsible for handling alternatives extract data from Farook's iPhone 5c.
"Throughout the investigation, I and other Apple representatives, including a senior engineer, continually made ourselves available to the government, on a 24/7 basis, participating in teleconferences, providing technical assistance, answering questions from the FBI, and suggesting potential alternatives for the government to attempt to obtain data from the Subject Device," Olle's declaration reads.
Investigators have been unsuccessful in their attempts to break into Farook's iPhone 5c, which is protected by a strong encryption method designed to thwart brute-force attacks. To circumvent this particular security layer Apple would need to write a new, compromised version of its iOS operating system, sign the code and install it on the device. But Apple is refusing to comply, citing an overreach of federal authority and potential First Amendment rights implications.
With all other options apparently exhausted, and Apple refusing to create compromised code Cook likened to an iOS encryption "master key," the FBI filed an ex parte application to compel Apple's assistance. Federal Magistrate Judge Sheri Pym subsequently converted the motion into an order but, unlike the FBI, allowed Apple a chance to respond.
In a footnote to Apple's legal response, filed yesterday, the company said:
The government obtained the Order without notice to Apple and without allowing Apple an opportunity to be heard. [...] But this was not a case where the government needed to proceed in secret to safeguard its investigation; indeed, Apple understands that the government alerted reporters before filing its ex parte application, and then, immediately after it was signed and confirmed to be on the docket, distributed the application and Order to the public at about the same time it notified Apple. Moreover, this is the only case in counsel's memory in which an FBI Director has blogged in real-time about pending litigation, suggesting that the government does not believe the data on the phone will yield critical evidence about other suspects.
For its part, Apple says it has complied with thousands of valid search warrants seeking customer data deemed vital to criminal investigations, a fact the DOJ also noted in its motion to compel. Until the San Bernardino case, however, the company has not been asked to build a software workaround that ostensibly defeats iOS encryption.
Apple and its lawyers argue that the government, if allowed to set precedent in this case, would be granted "limitless" power that could one day infringe on basic civil rights. On the flip side, the FBI, Justice Department and White House content an Apple-created exploit would be strictly limited to a single device.
A hearing on the matter is scheduled to for March 22.
 Mikey Campbell
Mikey Campbell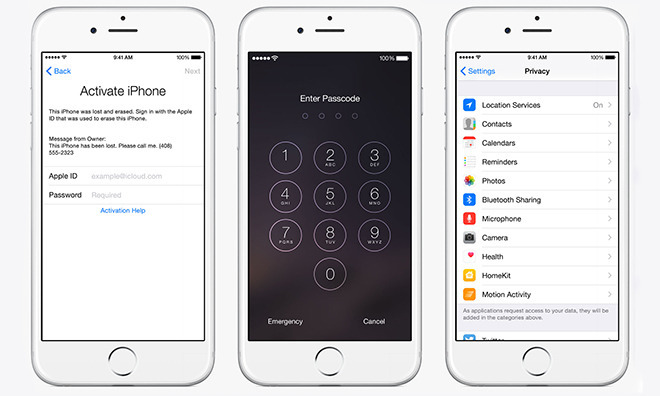







-m.jpg)






 Marko Zivkovic
Marko Zivkovic
 Mike Wuerthele
Mike Wuerthele
 Christine McKee
Christine McKee
 Amber Neely
Amber Neely
 Sponsored Content
Sponsored Content
 Wesley Hilliard
Wesley Hilliard

 William Gallagher
William Gallagher









67 Comments
Of course it will be limited to this device. But when precedence is set, anyone can ask Apple to re-do it.. again and again.
Comey is very cunning. He's also a lying bag of sh1t.
It's time to face facts: The FBI rigged this investigation to set a precedence. They broke the iPhone 5c so there would be no way for Apple to get the data off it. They are trying to use Apple as an example, but they underestimated Apple as most people do. Now there is an accurate timeline and we can see how the FBI is trying to mislead the American public to take away our privacy and liberty.
As the evidence and timeline became public, it is clear that the FBI are incompetent, and liars.
Perhaps millions of us should sign on letters of support for Apple's position and submit them to Apple's legal team to bolster their case?
EDIT: Well, heck look what I just found!
https://www.google.com/amp/cpt-amp.production.gannettdigital.com/story/80935714/?client=safari#fpstate=amp_viewer