Through a Los Angeles court, the FBI recently obtained a warrant forcing a woman to unlock an iPhone equipped with Apple's Touch ID fingerprint technology, according to a report.
The woman, Paytsar Bkhchadzhyan, pleaded no contest to a felony charge of identity theft earlier this year, and was sentenced on Feb. 25, the Los Angeles Times said. Just 45 minutes after Bkhchadzhyan was taken into custody, U.S. Magistrate Judge Alicia Rosenberg approved a warrant forcing the Touch ID unlock. By 1 p.m. the same day an FBI agent had managed to take Bkhchadzhyan's print.
The iPhone was confiscated from a home in Glendale belonging to Sevak Mesrobian, a member of the Armenian Power gang, and Bkhchadzhyan's boyfriend. It's not known exactly why the FBI wanted access to Bkhchadzhyan's device, although Assistant U.S. Attorney Vicki Chou indicated that the search was part of an ongoing investigation, and an attorney that previously represented Bkhchadzhyan and Mesrobian — George Mgdesyan — said that while he isn't defending Bkhchadzhyan at the moment, the FBI may be looking into hacking and "other issues." Mesrobian has been in prison since Feb. 12.
The Glendale case isn't the first in which U.S. court officials have ordered someone to unlock a device with their fingerprint, but such incidents are relatively rare and still controversial. While fingerprints don't normally require warrants, for instance, the issue becomes more complex when they serve as a "key" to personal information. Some critics suggest this is a violation of the Fifth Amendment's protection against self-incrimination.
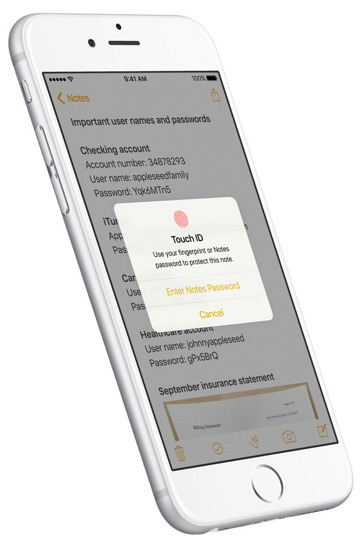
The Fifth Amendment means that a person can't be forced to supply a passcode, and indeed that's a particular problem for law enforcement when it comes to iPhones and iPads. iOS requires that a Touch ID user re-enter their passcode if a device is rebooted or hasn't been unlocked for 48 hours, which could potentially put data out of police reach.
The FBI has been managing to crack into some iPhones, but the techniques used may not apply to Touch ID devices, which have a "Secure Enclave" making hardware detours around encryption either difficult or impossible.