iPhone and iPad owners should be careful about which Shortcuts they run in iOS 12, since malicious app creators could use them to scrape valuable data, a developer warns.
An example shortcut is capable of scooping up contacts, browser history, app usage, names typed in Messages, and even file contents, according to one of the developers of the iPad programming app Codea. Critically the shortcut masquerades as a memory cleaner, but in truth it compresses data, uploads it, then sends a link to an attacker via Messages.
"You couldn't expect a reasonable user to know what they were agreeing to run when receiving an Apple-hosted link to this shortcut," said Simeon of Two Lives Left. "With automatic scheduling of shortcuts you could possibly trick someone into running a key logger."
Simeon noted that he's shared this information with Apple in the hopes of improving security. Given that Apple doesn't host all possible shortcuts, at present, it is impossible for Apple to guarantee security of all of the content produced, without clamping down on what the feature can do.
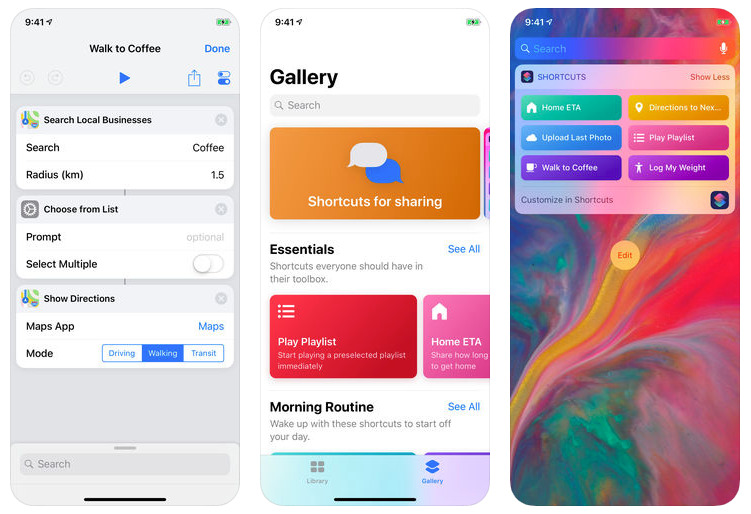
Shortcuts and their accompanying iOS app were introduced alongside iOS 12 in September. Users can build automations of regular tasks, such as an "I'm driving home" shortcut that launches Apple Maps, puts in the right directions, and starts playing NPR. Such shortcuts can be triggered quickly through a widget or Siri voice commands.
Apps can offer to enable their own shortcuts, but while they require permission, they don't necessarily identify all of the actions they plan to run.
For Apple Shortcuts are one way of competing with rival AI platforms, creating a Siri equivalent of Amazon Alexa's "skills." The company's strict privacy focus means that it taps on-device data processing whenever possible.