Apple's Enterprise Certificate program continues to be abused for unauthorized purposes with the discovery of a disguised spyware app that has the capability to acquire a considerable amount of data from a user's iPhone, one that may have been created by a government surveillance app developer.
Apple's program enables enterprise customers to create and distribute apps within an organization without being subjected to the App Store's content guidelines. The system allows for apps with far greater access to data within iOS than normal consumer versions, but the rules for the program means it cannot be used outside of an organization.
Despite it being against the rules, this hasn't stopped unscrupulous organizations from taking advantage of the Enterprise Certificate system to distribute apps that don't have to abide by the consumer-protecting App Store guidelines.
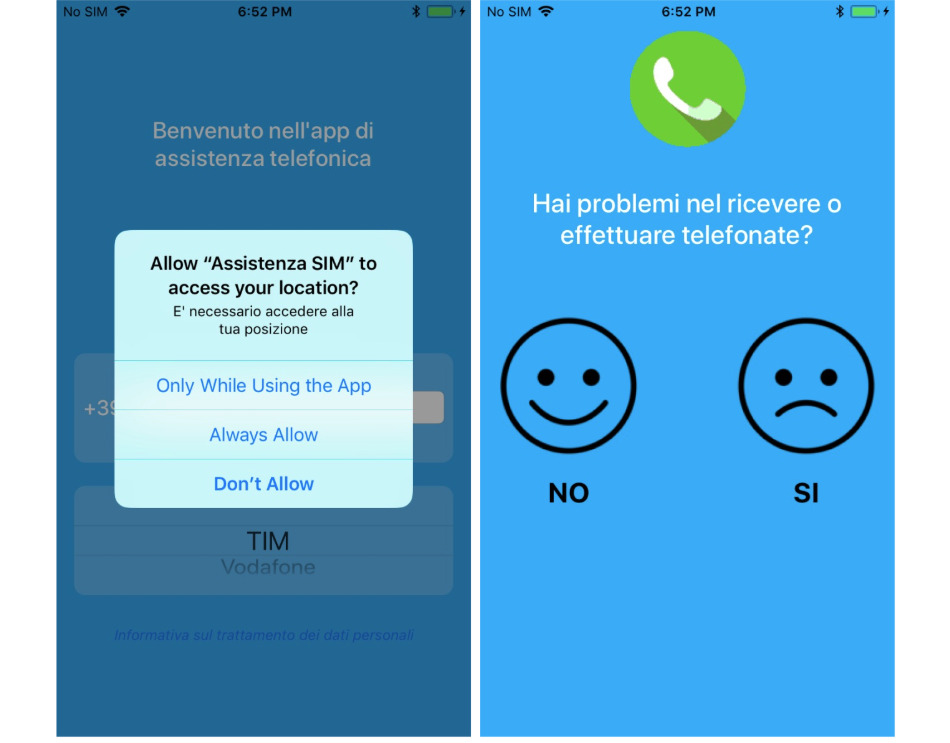
Mobile security outfit Lookout advised to TechCrunch a spy app was discovered pretending to be a carrier assistance app for mobile networks in Italy and Turkmenistan. Once installed, the app us capable of quietly acquiring contacts stored on an iPhone, as well as audio recordings, photos and video, real-time location data, and can even be used to listen in to conversations.
It is believed to have been developed by Connexxa, the creators of a similar Android app named Exodus that has been used by Italian authorities for surveillance purposes. The Android version had more reach than the latest iOS discovery, via the use of an exploit to gain root access.
Both the iOS and Android apps used the same backend, indicating the two are linked. The use of certificate pinning and other techniques to disguise its network traffic is thought to be a sign that the app was created by a professional group.
Once Apple was informed of the app's unauthorized activity by the researchers, Apple revoked the app's certificate, preventing it from functioning. It is unknown how many iOS users were affected by the attack.
The misuse of Apple's Enterprise Certificates program has become an issue for the company since the start of 2019. Early stories focused on how Google and Facebook were providing end users with Enterprise Certificate-equipped apps that monitored their usage habits, a situation that led to Apple revoking the certificates and, in Facebook's case, causing internal issues.
In February, it was discovered developers were also abusing the program to offer apps that would normally be banned from the App Store, including porn and gambling apps. Many were found to have acquired the certificates using another firm's details, allowing them to work around limitations to the number of users allowed under a certificate.
It was also found some developers were distributing hacked versions of popular apps, with users capable of streaming music without paying subscription fees, blocking advertisements, and bypassing in-app purchases. It also meant the developers of the legitimate versions of the apps were missing out on revenue, along with Apple failing to receive its usual 15 or 30 percent cut of all App Store Purchases.