Apple's security engineering chief Ivan Krstic will be making a reappearance at the Black Hat security conference in August, discussing the technologies protecting iOS 13 and macOS Catalina as well as how the Find My feature is kept secure.
Taking place on Aug. 8, the 50-minute talk "Behind the scenes of iOS and Mac Security" will have what is described as the "first public discussion of several key technologies new to iOS 13 and the Mac." The speaker, Krstic, is the Head of Apple Security Engineering and Architecture and is no stranger to Black Hat, having spoken at the conference in 2016 on iOS security mechanisms.
The upcoming talk will cover three main areas relating to security, starting with code integrity enforcement, a critical section of iOS' security architecture. Covering a history of code and memory integrity technologies in the iOS kernel, the talk will also cover Pointer Authentication Codes in the A12 Bionic and S4 chips, which prohibit the modification of important elements that could result in exploitable memory corruption bugs.
The implementation in iOS 13 will be discussed, including improvements, as well as previously-undisclosed VM permission and page protection technologies, which are part of the overall iOS code integrity architecture.
The T2 Security Chip, the second area, introduced security to the boot process that protected against direct memory access attacks at every point of the action. Krstic will walk attendees through the boot sequence and explain attack and defenses at every step, including "two industry-first security technologies" being disclosed for the first time.
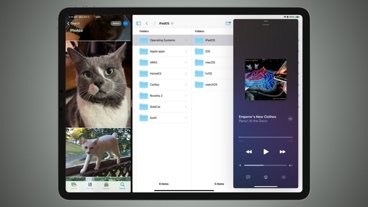
Lastly, the Find My feature in iOS 13 and macOS Catalina merges Find My Friends and Find My iPhone into a single function, but maintains privacy throughout in the latest incarnation via encryption. The talk will cover the "efficient elliptic curve key diversification system that derives short non-linkable public keys from a user's pair," that allows users to find their offline devices without needing any sensitive information to be passed to Apple.