Security firm Kaspersky says that in 2019 the Shlayer Trojan infected one in ten Mac users, opening the door to malicious apps that hide behind fake error messages about users needing to update Flash.
According to security firm Kapersky, Macs have been the frequent target of what's called the Shlayer Trojan. The company reports that this has been active since at least early 2018, but in 2019 specifically it was the most common threat to macOS. Around 10% of all Macs were attacked with it, and by itself, Shlayer represents 30% of all the Trojans detected on macOS.
The Shlayer Trojan is a delivery mechanism for a variety of malware payloads. It gets onto a Mac and then while not specifically harming the machine itself, it fetches other malicious code, typically adware.
From the user's perspective, there are three stages to what happens. The first is that they click on a link to a site which initiates a download of the Shlayer Trojan to the user's Mac. Kaspersky's report says that "thousands of websites" include this download, typically because the sites partner with cyber criminals.
However, legitimate sites could have this added, too.
"[These include] YouTube, where links to the malicious website were included in video descriptions," says Kaspersky in its report, "and Wikipedia, where such links were hidden in the articles' references."
Typically links take users to advertising pages which try to persuade them to download software. According to Kaspersky, a common method is to display faked messages about Adobe Flash being out of date. The "Download Flash" button actually downloads the Trojan.
Once downloaded, the user is prompted to install an application. It doesn't follow macOS's regular installation procedure though. Rather than double-clicking to install, the user is directed to first right-click and choose Open Package.
Then when it has been installed, the Shlayer Trojan itself downloads adware or other such malicious apps. These are still new apps being downloaded onto a Mac and so in theory they cannot be installed without the user's permission — but there is a way around it.
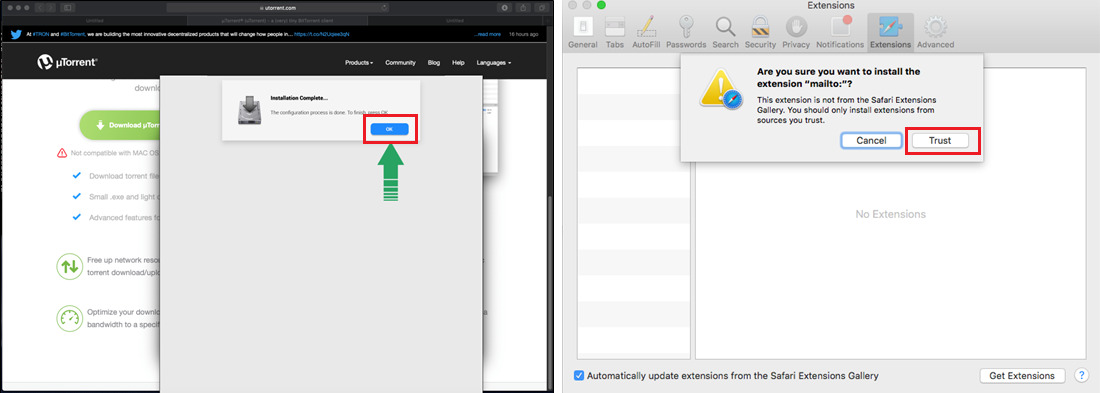
One type of malware that the Shlayer Trojan installs is a Safari Extension and the Mac does ask if you are sure that you want to use it. However, while macOS is warning that this is an unrecognized extension, Shlayer is overlaying that message with a fake dialog box saying that the installation is complete.
Users see an "Okay" button and click it, but in reality they are clicking a Trust button that macOS was actually displaying. They are telling the Mac that it is okay to install this software, so it does.
The final stage is that, at present, the Mac user can be bombarded with ads. Any browsing can also be affected by targeted ads being presented.
"[Since February 2018] we have collected almost 32,000 different malicious samples of the Trojan," says Kaspersky. "Having studied the Shlayer family, we can conclude that the macOS platform is a good source of revenue for cybercriminals."
Significantly, Kaspersky says that even though the Trojan was detected almost two years ago, it is still prevalent.
"The operation algorithm has changed little since Shlayer was first discovered, nor has its activity decreased much," the company continues. "[The] number of detections remains at the same level as in the first months after the malware was uncovered."
While Kaspersky reports that this particular Trojan is operating at around the same level as it always has, a separate report from Malwarebytes in April 2019 claims that Mac malware overall has grown enormously.