Security review finds 68% of top iPhone apps transmit UDIDs
A review of the "Most Popular" and "Top Free" categories on the iPhone App Store found that 68 percent of software would transmit UDIDs from devices. In addition, 18 percent of applications encrypted their communications, so it could not be determined what kind of data is being shared.
The findings were published last week by Eric Smith, network administrator with Bucknell University and a two-time DefCon wardriving champion. The security report, publicized by Engadget, claims that UDIDs can be "readily linked to personally-identifiable information."
The review was based on 57 applications available for the iPhone, and determined that personal information was sent out in plain text, posing a potential security concern.
The UDID is a unique identifier assigned to each iOS device, including iPhones, iPads and iPod touches. The number is used to prevent piracy with software available on the App Store.
In his findings, Smith compared the UDID assigned to iOS devices to the controversial Processor Serial Number that Intel attached to its Pentium 3 chips. He noted that the Pentium 3 PSN "elicited a storm of outrage from privacy groups," and questioned why those same concerns have not been expressed with the iPhone.
Among the applications that were found to transmit the iPhone UDID were software from Amazon, Chase Bank, Target, and Sams Club. The CBS News application goes even further, transmitting the UDID along with the user-assigned name for the iPhone, which typically includes the owner's real name.
"Most iPhone application vendors are collecting and remotely storing UDID data, and some of these vendors also have the ability to correlate UDID to a real-world identity," Smith wrote. "For example, Amazon's application communicates the logged-in user's real name in plain text, along with the UDID, permitting both Amazon.com and network eavesdroppers to easily match a phone's UDID with the name of the phone's owner."
Of course, to its credit, Apple has been very up front with security on iOS, requiring that users approve when applications access information like GPS or the phone's address book. In addition, the company has also allowed users to opt out of data collection with services like iAds.
The company even called out one mobile analytics firm, after data about the iPad was obtained from devices in testing on Apple's Cupertino, Calif., campus without the company knowing. The incident prompted Apple to revise some of the rules in its iPhone Developer Agreement.
 Slash Lane
Slash Lane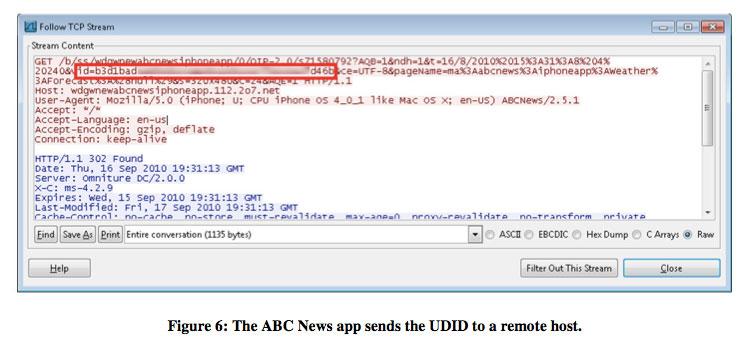











 Malcolm Owen
Malcolm Owen
 William Gallagher
William Gallagher
 Christine McKee
Christine McKee
 Michael Stroup
Michael Stroup
 William Gallagher and Mike Wuerthele
William Gallagher and Mike Wuerthele


 Chip Loder
Chip Loder






