A "huge" number of third-party Mac apps are under threat of man-in-the-middle attacks due to a recently discovered vulnerability in Sparkle, an open source framework used to facilitate software updates.
As reported by Ars Technica, a flawed WebKit rendering engine implementation found in certain Sparkle builds is to blame for the newly discovered attack that allows malicious users to insert and execute JavaScript code when affected app check for software updates.
Along with a flawed Sparkle version, vulnerable apps must also be running an unencrypted HTTP channel to receive software updates from offsite servers. Nefarious users capable of capturing network traffic, perhaps over an unsecured Wi-Fi connection, can leverage the Sparkle exploit to run malicious code remotely on a target computer. The publication cited work from a software engineer called Radek, who confirmed the exploit affects apps running on the latest versions of OS X 10.11 El Capitan and OS X 10.10 Yosemite.
While an exhaustive list of impacted Mac apps is unavailable, researchers successfully applied the exploit to Camtasia, uTorrent and a recent version VLC Media Player. It should be noted that developers are aware of the Sparkle vulnerability, as VLC patched the hole in an update last week. A running list of apps that use Sparkle as an update framework has been posted to GitHub
Sparkle Updater has pushed out a fix in its latest version release, but it remains up to third-party app developers to integrate the patched framework.
 Mikey Campbell
Mikey Campbell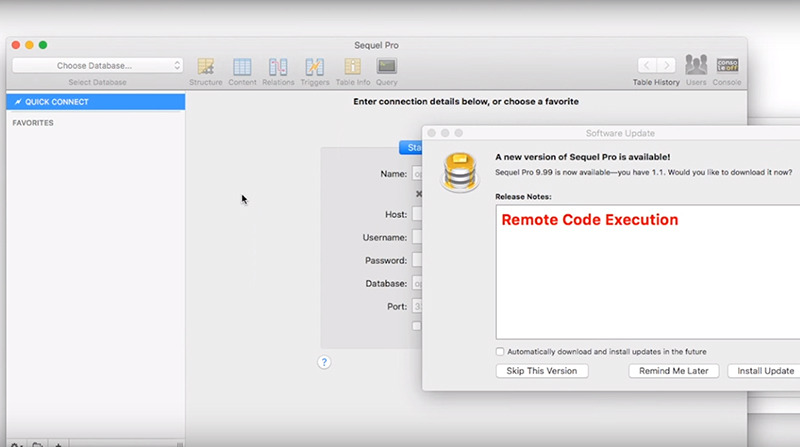







 Malcolm Owen
Malcolm Owen

 William Gallagher
William Gallagher




 Christine McKee
Christine McKee






21 Comments
I love it! I get this crap about how secure open source is because there are so many "eyes" on it. That total nonsense. Open source is as vulnerable as any proprietary software is, often more so.
Nice terminal command found on GitHub that searches your Applications folder and returns a list of those apps using the Sparkle framework. From that list you can check to see if any of your apps have updates available to patch the vulnerability. I tried it and it works like a charm.
Nope. Abject FAIL if there's an app using Sparkle framework in /Applications/Utilities:
find /Applications -name Sparkle.framework | awk -F'/' '{print $3}' | awk -F'.' '{print $1}'
Utilities
Utilities
VLC
Try this one-liner instead:
find /Applications -name Sparkle.framework | sed 's,/Applications/\(.*\)\.app/.*,\1,'
Utilities/Carbon Copy Cloner
Utilities/Mactracker
VLC
If Apple detects this vulnerability, they should shut down the computer and force the user to buy a new one! Anything short of that is a security risk!!! They could display something on the screen which clearly communicates the issue and the options a user has available to them - something clear and concise - like "Error 54" maybe...
/s