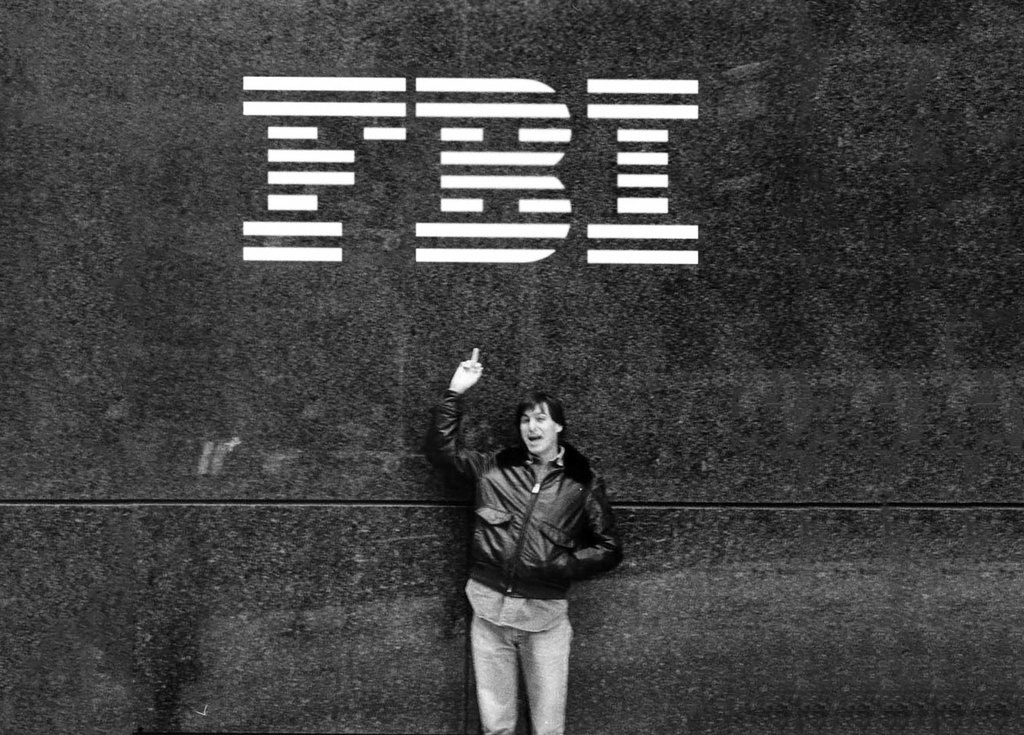
Actions by the leadership of the Federal Bureau of Investigation over the past month related to the San Bernardino encryption issue demonstrate a shocking level of dishonest and callous disregard for the nation's core principles of democracy. FBI director James B. Comey should issue a formal apology or resign his post, AppleInsider's Daniel Eran Dilger argues.
The role of the FBI — Â policing and solving a spectrum of federal crimes involving serial killers, terrorists, gangs that exploit children, government corruption and civil rights violations — is far too important to be besmirched by a manifestly dishonest smear campaign against Apple, created to spook and fool the public into accepting the creation of dangerous new legal powers without any respect for the role of elected representatives.
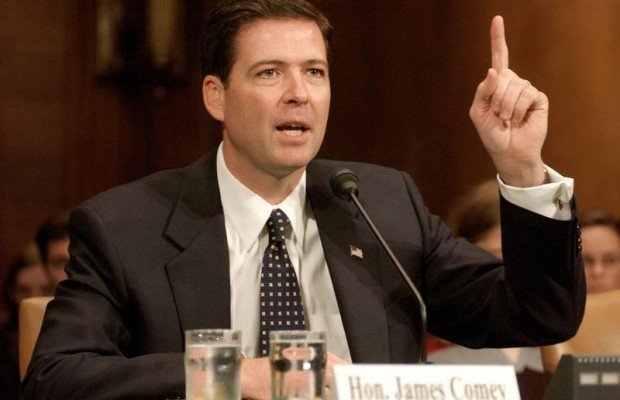
FBI director James Comey has a vast public record of desperately wanting to break encryption.
It is now clear that virtually every material statement made by the FBI about the encryption issue was flat-out false. While there is some controversy involving differences of opinion on the proper role and reach of government, the FBI has an obligation to be honest and genuine in its public communications, and in this case it has been everything but.
The FBI must not misrepresent its true intent
Last week, Comey issued a press release that began with "the San Bernardino litigation isn't about trying to set a precedent or send any kind of message."
It also characterized the legal issue in stating "the relief we seek is limited and its value increasingly obsolete because the technology continues to evolve." It described the FBI's demand that Apple develop for it a new version of iOS that disables key security features in the words, "we simply want the chance, with a search warrant, to try to guess the terrorist's passcode without the phone essentially self-destructing and without it taking a decade to guess correctly. That's it.
"We don't want to break anyone's encryption or set a master key loose on the land," he added. He just repeated those same comments earlier today.
However, Comey has a vast public record of desperately wanting to break encryption. That comes on top of the obvious reality that of course police always want every avenue available to track down criminals and stop or solve crimes.
End-to-end encryption of communications and of stored data is a clear and obvious barrier for law enforcement doing their jobs, just as it is an impediment to totalitarian governments trying to track down dissidents or hackers trying to steal individuals' identities, firms' trade secrets, or commit all sorts of fraud.
Along with encryption, law enforcement is also stymied by criminals bearing arms, refusing to testify against themselves, or simply committing crimes in the dark without arousing any probable cause that might justify a search warrant to allow police to enter their home to investigate. The U.S. Constitution erects a number of limits on what the government can do, many of which directly make the jobs of law enforcement more difficult.
However, Comey knows a precedent-setting back door that effectively neutralizes iOS encryption is not a popular idea among Americans. So instead of lobbying for it in Congress, he's waging a populist campaign that disingenuously claims to only need the opposite of what he's actually after.
The Obama White House and the Department of Justice are also being disingenuous and even dishonest as accomplices to this charade.
It's not just misleading about the true intent. Also at issue is the fact that all three are working to shove through a legal demand that "actually harms American safety and security," as observed by the former head of both the Central Intelligence Agency and the National Security Agency.
Comey testified to Senators that he wants to stop encryption
As he testified to the Senate Judiciary Committee last July, Comey has a particular problem with encryption because it has, as he testified, "eroded our ability to obtain electronic information and evidence pursuant to a court order or warrant." He referred to this problem as "Going Dark."
In his testimony, Comey acknowledged that "American citizens care deeply about privacy, and rightly so," and stated that "we have always respected the fundamental right of people to engage in private communications," adding, "citizens have the right to communicate with one another in private without unauthorized government surveillance— not simply because the Constitution demands it, but because the free flow of information is vital to a thriving democracy."
After those platitudes, Comey got real. He noted the arrival of a "new scale" of "mainstream products and services designed in a way that gives users sole control over access to their data. As a result, law enforcement is sometimes unable to recover the content of electronic communications from the technology provider even in response to a court order or duly-authorized warrant issued by a federal judge."
Comey presented an example of a truck driver who was convicted of kidnapping and rape. He had captured his own crimes on video on his smartphone, and those videos were presented as evidence at trial.
"In a world where users have sole control over access to their devices and communications, and so can easily block all lawfully authorized access to their data, the jury would not have been able to consider that evidence, unless the truck driver, against his own interest, provided the data," Comey announced.
Comey then stated, "we would like to emphasize that the Going Dark problem is, at base, one of technological choices and capability.
"We are not asking to expand the government's surveillance authority, but rather we are asking to ensure that we can continue to obtain electronic information and evidence pursuant to the legal authority that Congress has provided to us to keep America safe."
He described at length the "demanding" nature of obtaining a wiretap warrant, then complained that "the evolution and operation of technology today has led to recent trends that threaten this time-honored approach."
Comey tried to pass a law against encryption, but failed
Further calling into question the claim that "we don't want to break anyone's encryption," Comey's FBI worked with the White House on a legal strategy designed to force Apple to build a backdoor into iOS — right up until last October, when the Obama administration apparently decided that there would be too much political opposition to achieve that.
In November, Josh Gerstein reported for Politico that "the White House decided last month not to press for legislation that would force American companies like Apple to provide a mechanism for authorities to de-crypt an encrypted phone."
Gerstein added, "Much of the recent concern appears to have been spurred by the latest generation of Apple phones, where encryption is on by default and the company claims to have no ability to crack the encryption."
He cited Comey as stating, "The position of the administration is it didn't make sense to seek legislation now. There was more work to do before we figured out what was the way forward."
After failing to mandate an iOS backdoor, FBI was looking for "the way forward"
On December 2, the San Bernardino shooting resulted in 16 deaths and 24 injuries — the largest since the Sandy Hook shootings killed 26 people three years prior. Investigators concluded the assailants were inspired by the radical Islamic State, making the incident a political hotbed for national security implications.
Data on the killers' phones that might have helped police was irretrievable, but not because of encryption. It was because the phones had intentionally been physically destroyed by the killers. However, a work phone also possessed by one of the killers was found. It was encrypted.
Apple worked with the FBI to advise the police on ways that the discovered phone could have data retrieved from it, but the FBI admitted that it instead instructed San Bernardino County (the owner of the device) to reset the phone's Apple ID, which had the effect of making it impossible to trigger a backup of additional data that might be retrievable.
This appeared to be incompetence. However, the FBI later issued a bizarre statement that suggested this was done with an understanding of the consequences, stating, "Even if the password had not been changed and Apple could have turned on the auto-backup and loaded it to the cloud, there might be information on the phone that would not be accessible without Apple's assistance as required by the All Writs Act order, since the iCloud backup does not contain everything on an iPhone."
Two months after the phone was recovered, the FBI launched the issue into the public sphere by that demand for "assistance as required by the All Writs Act order," a shaky legal theory based on a slavery-era law from 1789 that the FBI interpreted as a catch-all for demanding, via the courts, anything "necessary or appropriate in aid of their respective jurisdictions and agreeable to the usages and principles of law."
It's not surprising that the FBI wants a backdoor for iOS. However, it is dishonest for its director — Â and the White House itself — to insist that this issue needs help from Apple that is "not a backdoor" and is limited to "this one case," when both have been working for months, looking for "a way forward" on how to bring an end to iOS encryption.
Why Tim Cook is recommending Congress address this issue
The White House, via the Department of Justice, is suddenly pressing for emergency action. Is this because there are fresh leads potentially locked on the employer's iPhone 5c two months after shootings occurred? Or because they know they may not get another opportunity to wrap up their demands for an iOS backdoor under the veil of terrorism?
The Obama administration, the DOJ and the FBI also know — Â because they came to that conclusion in October — that elected members of the Senate and House of Representatives are not likely to be sympathetic to a demand by the police for Apple to deliver a back door into the device being used by the majority of Americans. As Comey testified, "American citizens care deeply about privacy."
The FBI didn't just stumble upon the All Writs Act over the last month, however. A filing by Apple unsealed on Tuesday showed that the federal government has previously pursued nine other cases— going right back into last October, the same month that the FBI and the White House gave up on the possibility of getting Congress to force Apple to build a backdoor into its products for the convenience of police.
Even Michael Hayden, a former chief of both the CIA and the NSA — Â who served as the NSA's director as it conducted the controversial surveillance program that collected telephone metadata on millions of Americans — Â called out Comey as not shooting straight about his real intent.
"In general I oppose the government's effort, personified by FBI Director Jim Comey," Hayden said in an interview. "Jim would like a back door available to American law enforcement in all devices globally. And, frankly, I think on balance that actually harms American safety and security, even though it might make Jim's job a bit easier in some specific circumstances."
Hayden added, "when you step back and look at the whole question of American security and safety writ large, we are a safer, more secure nation without back doors." If there's a back door, he said, "a lot of other people would take advantage of it."
[At the same time, Hayden also prefaced his concerns with, "In this specific case, I'm trending toward the government," showing how easy it is— even for those who are aware of the consequences— to relax their principles when short term appearances are weighed as more important than true safety and security.]
Not about unlocking
Comey's FBI and the Obama administration are gaining some cover from the media as well, which keeps suggesting that the issue in question is whether or not "Apple should help the police to unlock a terrorist phone."
This is also absolutely untrue. Apple isn't being asked to unlock a device.
The FBI knows Apple can't unlock it, because there is no master key that exists anywhere. What it is demanding is new software that would bypass iOS's existing security features to allow the FBI itself to guess the passcode for as long as it needed to access the device.
Apple Chief Executive Tim Cook called this new software a "cancer," suggesting that once unleashed, it would be impossible to control. And of course, if the U.S. federal government already has nine other requests in the queue for a security bypassing back door to get past encryption, setting a new precedent for the "Mother of All Back Doors" means that there will be a steady stream of new demands.
And if the U.S. can achieve its goals via a court order, clearly any other country Apple does business in can also demand access to the same capabilities, without even needing to establish any sort of democratically-originated legal basis in law.
That alone is reason enough for Comey to immediately dial down the FBI's rhetoric and withdraw the demands for a back door from Apple, made without the consultation of Congress having the opportunity to fully debate the issues involved without the fervent, rushed emotionalism this public smear campaign is attempting to leverage.