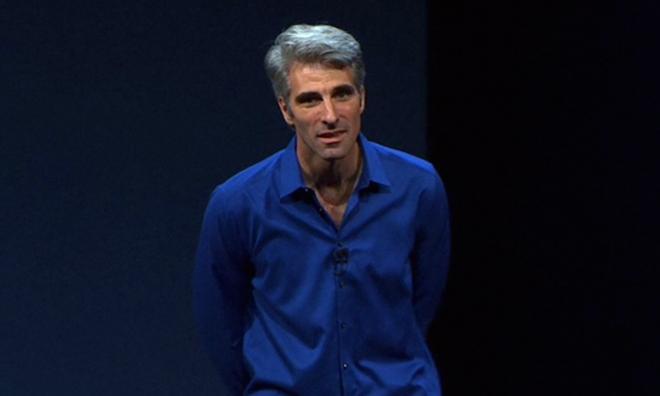
Apple's head of software engineering Craig Federighi published an opinion in the Washington Post today that clarified the company's reasoning behind refusing to weaken its products to appease a very public demand from the FBI.
Federighi emphasized that the security Apple has designed into its platforms is a continuous effort "to stay one step ahead of criminal attackers who seek to pry into personal information and even co-opt devices to commit broader assaults that endanger us all."
He noted that in just the last year and a half, criminals have attacked retailers, banks and even the federal government, stealing "credit card information, Social Security numbers and fingerprint records of millions of people."
"The encryption technology built into today's iPhone represents the best data security available to consumers," Federighi wrote. "And cryptographic protections on the device don't just help prevent unauthorized access to your personal data — they're also a critical line of defense against criminals who seek to implant malware or spyware and to use the device of an unsuspecting person to gain access to a business, public utility or government agency.""That's why it's so disappointing that the FBI, Justice Department and others in law enforcement are pressing us to turn back the clock to a less-secure time and less-secure technologies" - Craig Federighi
Any weaknesses found must be addressed "to keep customers safe," he continued, before noting, "That's why it's so disappointing that the FBI, Justice Department and others in law enforcement are pressing us to turn back the clock to a less-secure time and less-secure technologies."
He added, "to get around Apple's safeguards, the FBI wants us to create a backdoor in the form of special software that bypasses passcode protections, intentionally creating a vulnerability that would let the government force its way into an iPhone. Once created, this software — which law enforcement has conceded it wants to apply to many iPhones — would become a weakness that hackers and criminals could use to wreak havoc on the privacy and personal safety of us all."
Federighi concluded, "Security is an endless race — one that you can lead but never decisively win. Yesterday's best defenses cannot fend off the attacks of today or tomorrow. Software innovations of the future will depend on the foundation of strong device security. We cannot afford to fall behind those who would exploit technology in order to cause chaos. To slow our pace, or reverse our progress, puts everyone at risk."
Law enforcement praised Apple's iOS Activation Lock
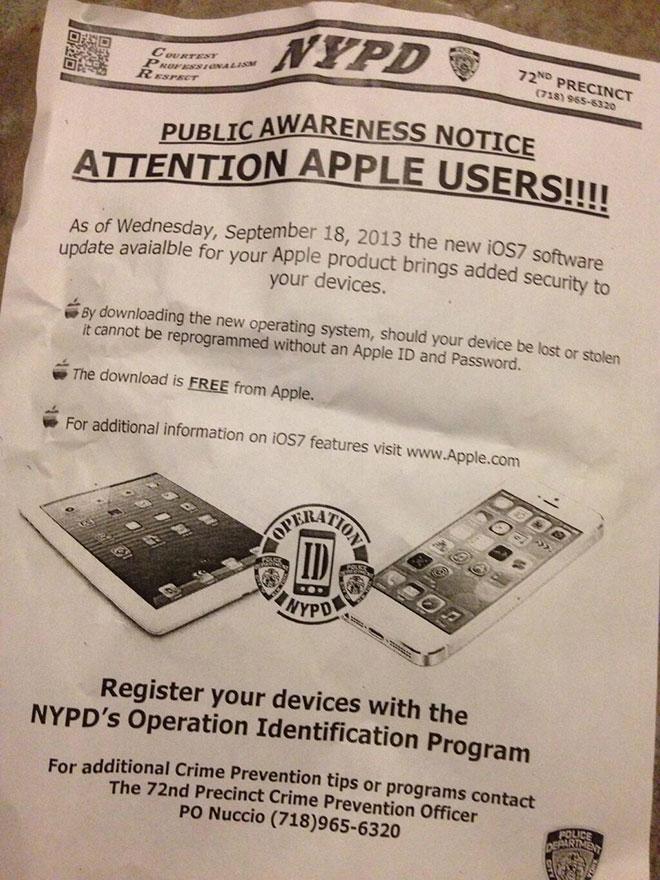
One issue Federighi didn't directly touch on is the fact that beginning in 2013, federal agencies and local law enforcement were praising Apple for its work in developing Activation Lock, a technology rooted in boot level OS security and device encryption that makes stolen phones difficult or impossible to reactivate without the user's credentials.
That advance in iOS security resulted in a dramatic drop in iPhone thefts and the related violent crime epidemic that had been erupting in association with iPhone muggings from San Francisco to New York City to London.
In 2014 and again last year, law enforcement groups pointed to significant drops in violent crime statistics directly related to the strong security employed in iOS Activation Lock— 25 percent in New York, and 40 percent in San Francisco.
Police in New York City were actively encouraging users to upgrade their iPhone software to take advantage of the increased security (below), which has been regularly enhanced with each major release since then.
Apple has stated that it plans to continue to enhance iOS security, a subject that may complicate some law enforcement efforts to obtain data associated with criminals, but which also protects far more victims from violent crime— and from identity theft and other digital attacks— in addition to device surveillance by extremist governments and terrorist groups.