The unlocking procedure used by the Federal Bureau of Investigation to break into an iPhone 5c at the center of the San Bernardino case cannot be used on new devices, the bureau's director said on Wednesday.
Comey told a group of students and educators at Kenyon College in Ohio that his department had "purchased a tool" from a third party to unlock the iPhone in question, according to CNN Money. Though he stopped short of revealing the exact process, he did note that it would not work on more modern handsets.
"This doesn't work on 6S, doesn't work on a 5S, and so we have a tool that works on a narrow slice of phones," Comey said.
Discussing Apple's request that the bureau unveil its method, Comey was noncommittal but said he was worried about losing what little access the bureau does have.
"We tell Apple, then they're going to fix it, then we're back where we started from," he said. "We may end up there, we just haven't decided yet."
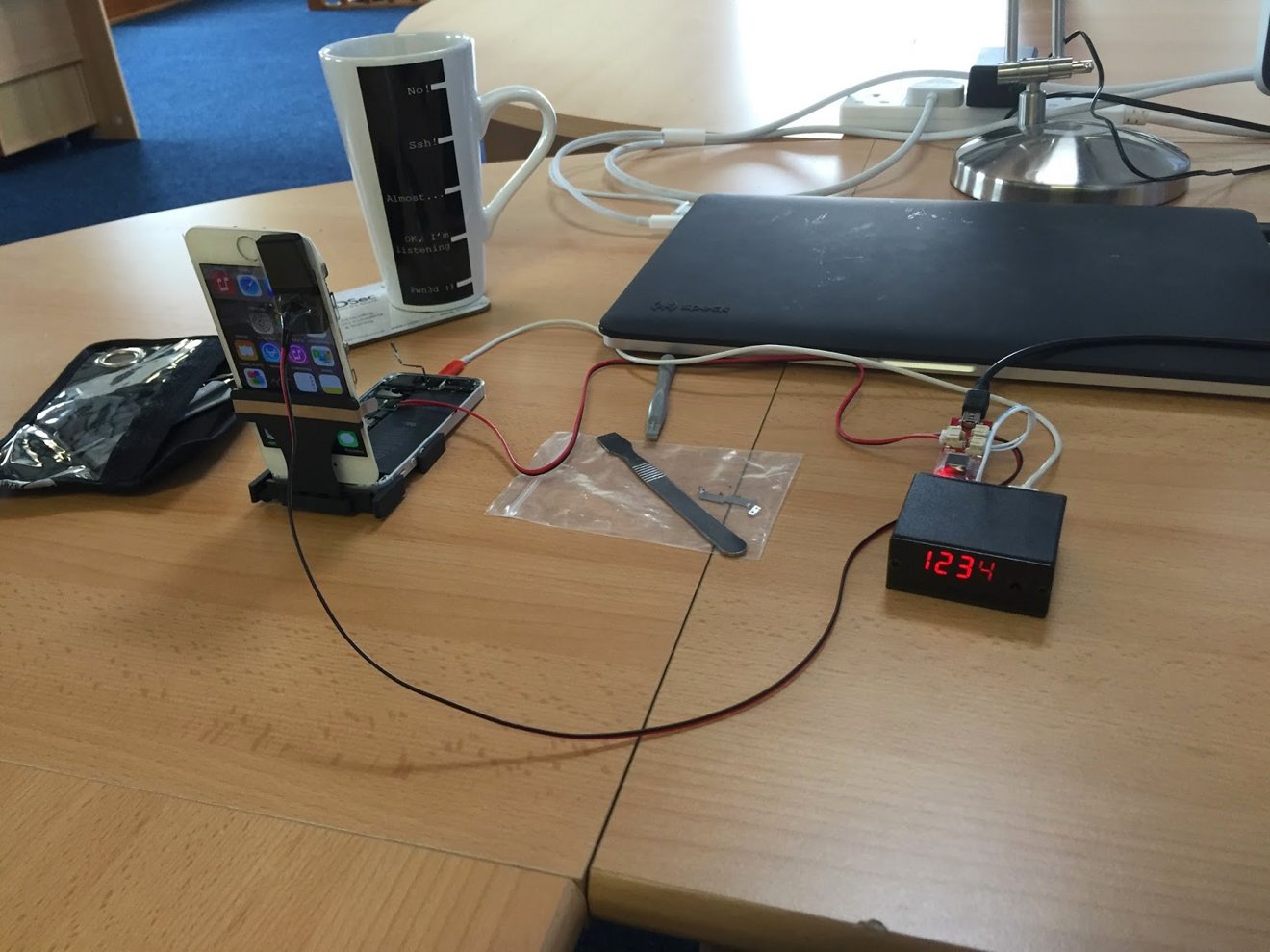
Since the FBI revealed its success late last month, most speculation regarding their method has centered around the so-called "IP Box" that first appeared last spring. That tool — which retails for less than $300 — latches onto a susceptible iPhone's power circuitry and enters PINs over USB.
When a wrong guess is detected, the tool aggressively cuts power to the iPhone's logic board before the guess is recorded, defeating the 10-try limit.
Apple is believed to have patched this hole in older iPhones with iOS 8.1.1; as the iPhone 5c in question is thought to be running iOS 9, the FBI has either chosen a different method or has purchased the device from a company that has discovered an as-yet unreported flaw in later software.
Beginning with the iPhone 5S, PIN guesses are managed in the hardware Secure Enclave, rendering such an attack useless.