A vulnerability has been discovered in macOS that could allow an attacker to impersonate a mouse click, enabling for it to bypass security prompts and completely compromise a Mac, a flaw that was found by accident.
Revealed at the Defcon computer security conference, Digita Security's Chief Research Officer Patrick Wardle advised that "synthetic" events, namely software-based clicking of interface objects, are still a problem for macOS. While Apple has attempted to fix the flaw, the new discovery means synthetic clicks are still capable of working in certain circumstances, reports Threat Post.
A synthetic click in malware could be used to bypass security prompts that users must agree to, before allowing specific activities to take place. This can be anything from simply enabling access for sensitive elements, like the Keychain, to riskier activities like loading a kernel extension.
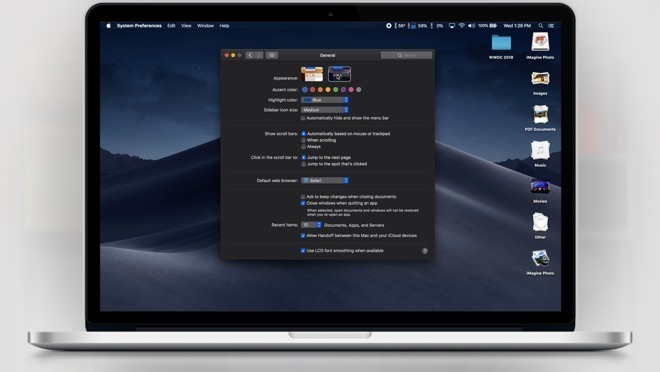
Previously, synthetic clicks were an issue that was solved in a new security feature called "User Assisted Kernel Extension Loading," which forced users to manually approve the loading of a kernel extension via an "allow" button in the security system interface. In macOS High Sierra, the operating system has been filtering out synthetic clicks that could affect security alerts, making the technique unusable by attackers.
At the presentation, Wardle admitted he discovered a flaw by accident while working in High Sierra, but noted that his code's actions worked around the restrictions.
A mouse click is interpreted as two actions in macOS, namely the "down" and "up" elements to click and to release. Wardle's discovery was that two consecutive synthetic "down" events were misinterpreted by High Sierra as a manual legitimate click, with the errant "up" event seemingly coming from macOS itself and bypassing the filtering system.
Wardle discovered it by making a mistake while copying and pasting code for synthetic mouse clicks, forgetting to change a flag value for an "up" event. After compiling the code, he discovered it allowed the synthetic click to function.
"Two lines of code completely break this security mechanism," said Wardle. "It is truly mind-boggling that such a trivial attack is successful. I'm almost embarrassed to talk about the bug as it's so simple - though I'm actually more embarrassed for Apple."
The flaw only affects High Sierra and not earlier versions, but it is likely to be shortlived. Wardle advised macOS 10.14 Mojave will block all synthetic events completely, which will prevent such attacks from occurring completely, though it could also affect legitimate apps that take advantage of synthetic clicks for various functions.