Apple is seemingly attempting to combat the problem of phone scammers and other types of nuisance callers, by coming up with a method to detect if the inbound call is using a spoofed number and warning the recipient before they answer.
Nuisance calls are continuing to be a major problem for phone users around the world, with telemarketing spam, scams, and other types of "robocalls" bombarding people with calls and messages they do not want to see. While there are ways to block regularly-received nuisance calls, such as with block lists, the callers have ways to work around the restrictions.
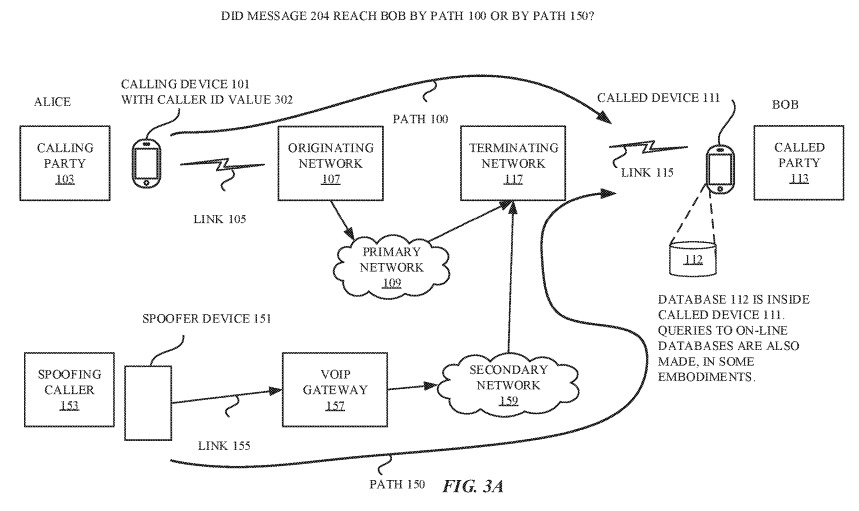
One way is to spoof phone numbers, namely to make the call seem like it is coming from a different number. Spoofing allows calls to pass through blocking systems if the number is not on the list, as well as preventing the user from seeing the actual source of the call via caller ID before answering, something which can even make them more likely to answer if it's supposedly from a local area code, a trusted company, or a government agency.
Hiding the number behind another also reduces the possibility of a scammer from being reported to the authorities. It also means that irate callers cannot phone the scammer or telemarketer back to complain.
Published on Thursday by the U.S. Patent and Trademark Office, Apple's patent application for "Detection of spoofed call information" proposes a system where an iPhone or other mobile device could perform checks on a call to ascertain if it is genuine, then either warn the user of the problematic call or prevent it from disturbing the phone user at all.
In some cases when a call is made, a session initiation protocol (SIP) invite is sent along between phone networks to the user's device. The SIP invite can contain a number of elements, with headers providing data meant to establish the call, such as speech codec information, network equipment identifiers, 3GPP VoLTE protocol information, server identifiers, and other elements.
While the spoofing caller can fill in some of the SIP invite fields, some are populated or overwritten by network servers as it travels. This automatically added or altered information constitutes a signature for that network, which could be used to compare with other existing call signatures to determine if the call itself is legitimate.
For example, the speech codec information could state the call is from a network's "internet multimedia subsystem" rather than VOIP, which would lean the device towards the call being legitimate due to VOIP being favored by nuisance callers. Identifiers could also be checked against a list of similar already-known identifiers, to confirm the call is passing through the correct phone networks and servers for the claimed origination point.
The system could also be used to determine if the spoofer is passing the call through a forwarding device, which is connected to a legitimate network and sends the SIP invite itself, potentially through a number from the user's address book. Using VIA headers, the device can check the number against the address book of the user, or a previously-established list, to verify the call is coming from the correct identified source.
In cases where the phone believes there to be too many discrepancies in the SIP invite, it can refer the "call record" to a database of other call records online. The database includes templates for different types of call initiation messages, which could be used to either confirm the call as legitimate or provide where it is really coming from.
Apple files numerous patent applications each week, and while the appearance of a granted patent or an application at the USPTO may be promising, there is no guarantee the concepts in the filing will become available in a future consumer product.
In this case, it is plausible for such a detection system to be enacted, but it would require cooperation between telecommunications firms to set up and operate. Apple does have influence over mobile networks due to the popularity of the iPhone, which could be used to implement the system in this way.
Apple is involved in an FCC "Robocall Strike Force," along with Google, AT&T, and 30 other companies, aiming to cut down on the number of nuisance calls made and received in the United States.
During Wednesday's launch of the Google Pixel 3, Google revealed the smartphone will include Call Screen, a screening feature that uses Google Assistant to answer and transcribe the caller's request and display the text to the user. The transcription is then provided to the user, who can answer, decline the call, or report the call as spam.
Apple is also currently in a legal battle with India's TRAI, where the regulator is threatening to ban iPhones from all of the country's networks if Apple does not enable its Do Not Disturb anti-spam app to be installed on iOS devices.