A report claiming Chinese spy chips were secretly implanted into Super Micro servers used by Apple and other tech firms has been dealt another blow, with a delve into how secure servers work criticizing the report's lack of detail for the hack and insisting the claimed technique would have been implausible to pull off.
The original Bloomberg report alleging the existence of the spy chips has been refuted by many companies already, but while there have been declarations that it hasn't happened and doubts from both security experts and government agencies over its occurrence, there has been little explanation as to why the report is incorrect.
The deep dive by server-focused publication Serve The Home is a detailed and technical exploration over some of the report's claims, with the site noting numerous issues with Bloomberg's account. The description of how the hack worked is said to include "some fairly astounding plausibility and feasibility gaps," and is notably light on details and difficult to navigate.
The main issue with the report's claims is the description that the chips are "connected to the baseboard management controller, a kind of superchip that administrators use to remotely log in to problematic servers, giving them access to the most sensitive code even on machines that have crashed or are turned off." The chips are also claimed to be able to tell the connected device to connect to external computers, and to install code received from these servers into the device's operating system.
The claim of telling the device to communicate externally is noted as false due to basic industry security practices, namely that BMCs are typically networked separately from Internet-facing connections. The firms identified in the report, including Apple and Amazon, are also likely to have better security protections than the average small to medium enterprise, which would include hardened security for BMCs, making such attacks as described practically impossible.
The accessing of sensitive code on crashed or turned-off machines is also dismissed, as "This is not how this technology works." When the BMC is powered on, data stores and the processor are not turned on, and are not able to be directly communicated with in this state. In short, if the server storage is not on, it is inaccessible, and no supposed code injection could be performed at all.
Another section objected to in the investigation is the claim the spy chips would manipulate instructions that tells the server what to do when data moves across the motherboard, tweaking code in temporary memory en route to the processor. This is seemingly not plausible as the supposed implanted hardware "does not have the pin count nor the processing power to perform this interception."
In summing up the lengthy examination, Serve The Home insists Bloomberg needs to "present credible and verifiable information to prove this story is true," as the presented hack simply would not work. If such evidence or information is not available, Bloomberg should retract the story and investigate how it passed editorial muster.
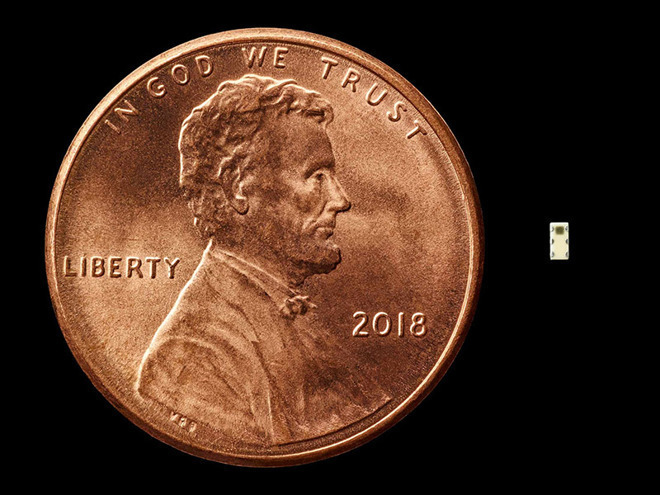
Graphic illustrating size of supposed Chinese spy chip allegedly embedded in Apple servers.
Source: Bloomberg Businessweek
On October 4, a Bloomberg report based on a multi-year investigation claimed that Apple, Amazon, and 30 other companies had been the victim of an espionage campaign in which rice-sized chips had been planted on motherboards made by Super Micro. Once delivered, the motherboards supposedly created a backdoor into infrastructure like Apple's iCloud.
Apple was quick to deny allegations, insisting that it had conducted a "massive, granular, and siloed investigation."
Amazon also issued a very clear denial of the story.
"There are so many inaccuracies in this article as it relates to Amazon that they're hard to count," Amazon said in its statement, refuting several specific claims, and specifically citing that there was no modified hardware found.
Several subsequent accounts have cast further doubt, such as one from the senior advisor for Cybersecurity Strategy to the director of the U.S. National Security Agency. Additionally, The U.S. Department of Homeland Security commented that it had "no reason to doubt" the positions of Apple and Amazon.
On Friday, Tim Cook also spoke about Bloomberg's allegations. Apple's CEO denied the report, and took issue with how the story's reporters communicated with Apple.
"There is no truth in their story about Apple," Cook said on Friday. "They need to do that right thing and retract it."
"I was involved in our response to this story from the beginning," said Cook. "I personally talked to the Bloomberg reporters along with Bruce Sewell who was then our general counsel. We were very clear with them that this did not happen, and answered all their questions. Each time they brought this up to us, the story changed and each time we investigated we found nothing."
"We turned the company upside down. Email searches, datacenter records, financial records, shipment records," Cook added. "We really forensically whipped through the company to dig very deep and each time we came back to the same conclusion: This did not happen. There's no truth to this."
On Monday, Super Micro said that it would continue to investigate the allegations found in the report. At the same time, Super Micro CEO Charles Liang echoed Cook's call for a retraction.
"Bloomberg's recent story has created unwarranted confusion and concern for our customers, and has caused our customers, and us, harm," Liang said. "Bloomberg should act responsibly and retract its unsupported allegations that malicious hardware components were implanted on our motherboards during the manufacturing process."
Bloomberg hasn't backed down from its claims, and U.S. senators have asked Super Micro for answers.
AppleInsider will be at the fall "There's more in the making" event, where we expect new iPad Pros, and maybe even new Macs! Keep up with our coverage by downloading the AppleInsider app for iOS, and follow us on YouTube, Twitter @appleinsider and Facebook for live, late-breaking coverage. You can also check out our official Instagram account for exclusive photos.