Wireless features like AirDrop and Wi-Fi password sharing on iPhones, Macs, and other Apple devices can expose exploitable data, according to a recent report — but there are two easy solutions.
The technologies broadcast a partial cryptographic (SHA256) hash, which can be used to obtain details like an iPhone's phone number or a Mac's static MAC address, said security outfit Hexway. The underlying issue is data packets sent through Bluetooth Low Energy (BLE), which for all Apple devices transmit information such as name, OS version, battery status, and whether Wi-Fi is on.
This is often innocuous and necessary, but could be used by some parties to track people or launch a more serious attack. In one short video, Hexway demonstrated an AirDrop-based exploit that allows someone to send an SMS message to a target.
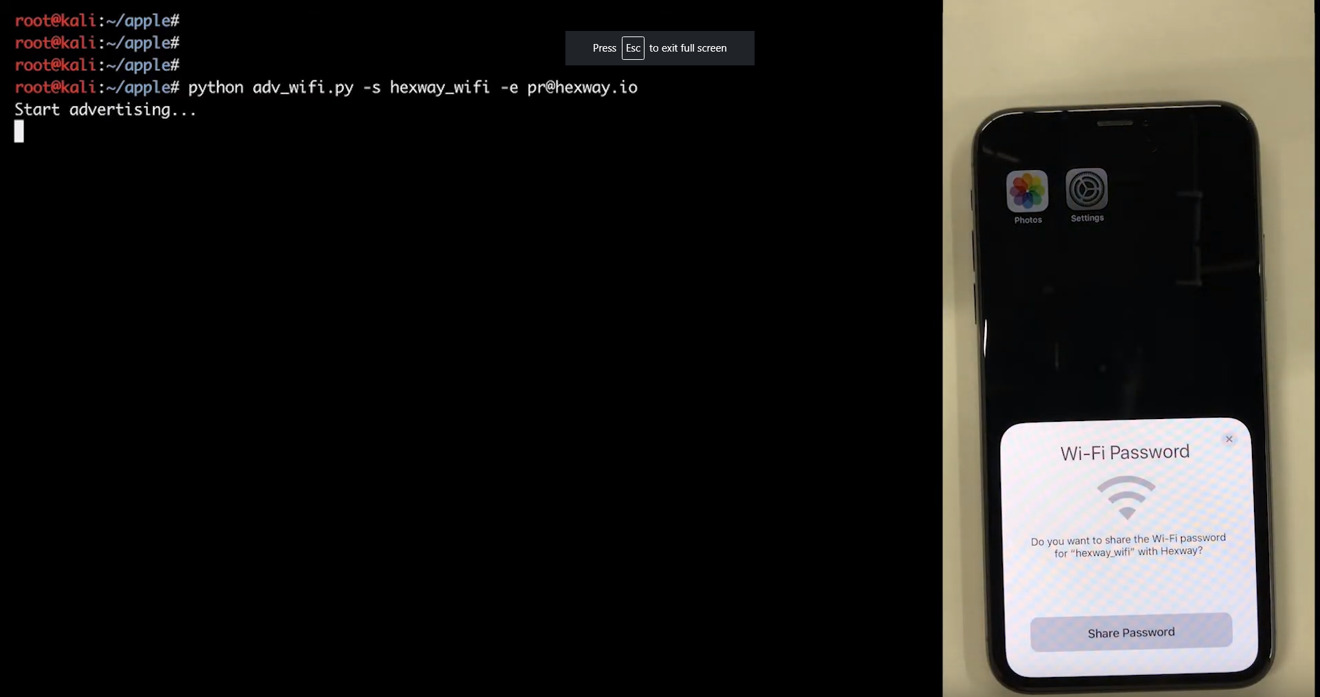
Attackers may also be able to send their own BLE requests and disguise themselves as devices like AirPods, or force target hardware to share a Wi-Fi password.
The issue is present on all iOS devices from iOS 10.3.1 onwards, Hexway said, though products prior to the iPhone 6s are only sending a limited number of messages instead of a continuous stream. Regardless, the only way of completely mitigating the threat is turning off Bluetooth, which may not be worth it — especially for people with accessories that depend on wireless, such as headphones or an Apple Watch.
"This behavior is more a feature of the work of the ecosystem than vulnerability," Hexway commented.
Much of this vector of attack is inherent to the BLE protocol, but AirDrop and similar sharing standards slightly expose the vector. It's recommended that Apple users lock down AirDrop as much as they can by setting it to "Contacts Only," or disabling it entirely, since strangers might otherwise be able send harassing images and other files.
The attack is still mostly a targeted one, and most users won't have to worry. There is no evidence that this vector is currently being exploited.