Despite vehement denials, virtual iOS tool creator Corellium allegedly sold its software to spyware and malware distributors, including the makers of the infamous Pegasus.
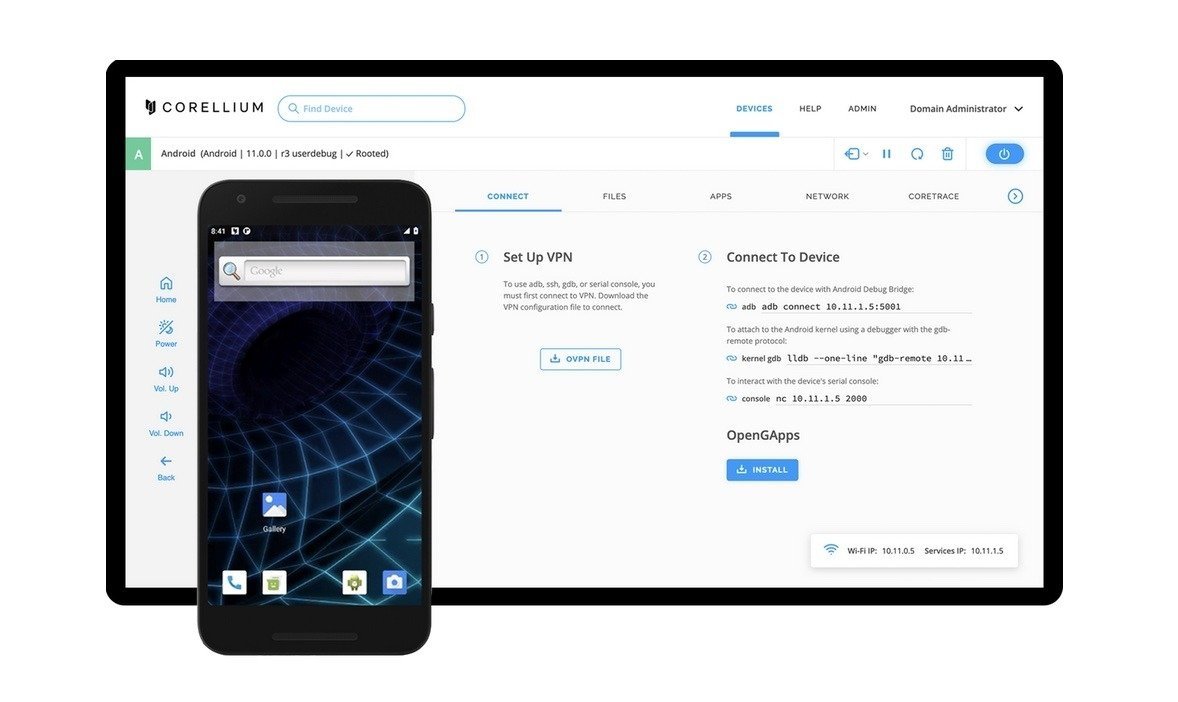
Corellium became known for producing a virtualized version of iOS to enable security firms and researchers to sniff out bugs and weaknesses. The firm has previously caught the attention of Apple, prompting a copyright lawsuit that was settled in 2021 but appealed against by Apple shortly after.
A leaked document prepared by Apple for the lawsuit seen by Wired has revealed that Corellium's tools are not used for good reasons. Internal communications in the 507-page tome indicates that Corellium's tools have been used by entities considered to be a threat to privacy and security.
The list includes NSO Group, an infamous security firm behind the Pegasus spyware, used to monitor activists, journalists, and other people of interest. The document mentions how NSO Group was provided a trial of its tool in 2019.
The lengthy document was created by Apple as part of its lawsuit, with the intention of showing Corellium has a history of providing its tools to bad actors in malware, including regimes with poor human rights records.
"Far from assisting in fixing vulnerabilities, Corellium encourages its users to sell any discovered information on the open market to the highest bidder," Apple said in its legal complaint against the firm.
This is the opposite of Corellium's continued insistence it's one of the good guys, with its tools intended to discover and report bugs in software.
Communications from Corellium's sales teams also offered a quote to supply the software to DarkMatter, a cybersecurity outfit. DarkMatter, now closed, had links to the UAE government, which has a history of clamping down on human rights activists and journalists.
Corellium told the publication NSO Group and Dark Matter had access to the "limited time/limited functionality trial version" of its software, but both companies were denied the ability to purchase after a vetting process.
The document also said the company also sold its software to Paragon in 2019, a firm thought to be a surveillance tech provider to governments around the world.
It also allegedly licensed the tools to Pwnzen Infotech, which was founded by part of the Chinese iOS and iPhone hacking group Pangu Team. In 2019, when Pwnzen was a customer of Corellium's tools, a sales rep for Pwnzen apparently said the company had assisted the Chinese government in hacking a person suspected of "subverting the government."
The list also includes Elcomsoft, a Russian iPhone hacking company. While Corellium says it vets to make sure companies aren't linked to countries sanctioned by the US government, Elcomsoft is apparently a customer despite being headquartered in the country.
It has also supposedly sold tools to Cellebrite, best known as the creator of devices sold to unlock iPhones. Cellebrite's hardware has been bought by many law enforcement agencies around the world, especially in the United States.
Practically all of the firms mentioned have links to countries who have extensive surveillance operations for monitoring potential critics of the government, including China, Saudi Arabia, and Bahrain.
Corellium insists it had "big opportunities to profit from these bad actors and have chosen not to," and that it restricts sales of its cloud product to "fewer than sixty countries," and has a "block list" for certain organizations.
The problem for Corellium is that its tool, while seemingly intended as a force for good, it has the potential to be used for criminal or underhanded reasons.
"While Corellium is a reverse-engineering tool that doesn't intrinsically create risks through its sale, the core purpose of the tool is to reverse malware," said independent privacy and security researcher Zach Edwards. "And if you sell the product to malware developers in countries averse to Western interests, we should assume that this tool will be used to improve malware."