Safari for iOS URL spoofing exploit revealed, with no documented fix
A security researcher has revealed an issue that can allow website addresses to be spoofed in Safari for iOS and Microsoft's Edge browser, but while Microsoft has since fixed the flaw, it is unclear if Apple has updated Safari, potentially leaving the iOS browser vulnerable to attack.
Researcher Rafay Baloch explains the vulnerability involves a specially created webpage that would load one set of content while showing a specific URL in the address bar, then rewriting the code for the body of the page without updating the URL at all, reports The Register.
The spoofing flaw, now identified as CVE-2018-8383 in relation to Edge, allowed javascript to update the address bar while the page was loading, said Baloch. When data was requested from a "non-existent port," the address was preserved, and due to a "race condition over a resource requested from non-existent port combined with the delay induced by setInterval function," was able to be spoofed.
To end users, this could allow for a malicious page to show what appears to be a genuine website page, complete with what appears to be the correct URL. This could be employed in attacks where a fake log-in page for a service could be presented to the user, under the pretense that it is a real authentication request.
Due to the closed source nature of the browsers, it is unknown why Safari for iOS and Edge are affected by this issue, but Chrome and Firefox remain unaffected.
The vulnerability was reported to both Apple and Microsoft on June 2, with Baloch issuing a 90-day deadline to create a fix before publication, a typical policy by security researchers. On August 11, a reminder of the 90-day deadline was issued, with Microsoft then releasing a fix as part of August 14 "Patch Tuesday."
Baloch released details of the flaw on September 10, with Apple yet to have confirmed publicly or to the researcher that it has been repaired. As a result, Baloch is openly discussing the flaw, but will not publish proof-of-concept code until such a patch has been released.
AppleInsider has contacted Apple about the flaw and the status of an update to fix it.
 Malcolm Owen
Malcolm Owen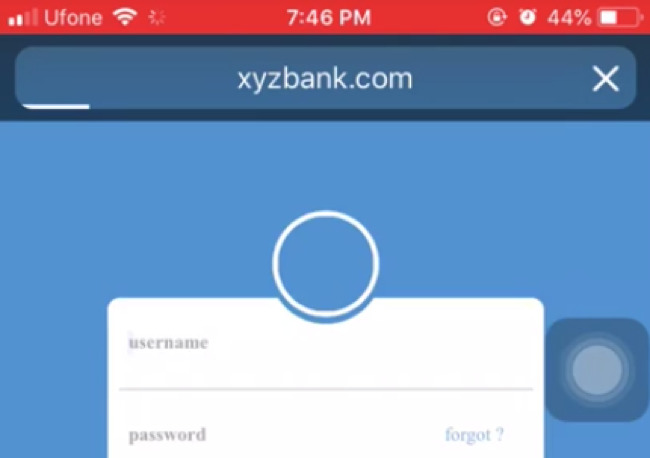











 Amber Neely
Amber Neely

 Marko Zivkovic
Marko Zivkovic
 David Schloss
David Schloss
 Wesley Hilliard
Wesley Hilliard
 Mike Wuerthele and Malcolm Owen
Mike Wuerthele and Malcolm Owen








14 Comments
I'll take a wild guess that it will be fixed tomorrow (?)
That's a really scary spoof because I always check the URL when I am asked for credentials. Hope Apple fixes it asap.
Yesterday I was trying to shop on eBay (with my iPad Pro, iOS 11), but every time I arrived on the eBay search results page I was within seconds redirected (without clicking anything) to a fraudulent external website. I tried to tell ebay customer service what was happening, but the poor woman was completely out of her league and could only think in terms of helping a customer who doesn’t understand how to properly use eBay. It’s an interesting hack/exploit though.