Two new trojan horses threaten Mac software pirates
iWork '09
Mac security software maker Intego discovered last week what it calls "OSX.Trojan.iServices.A" in pirated copies of Apple's iWork '09 making the rounds on BitTorrent file sharing networks. An additional package not found in retail copies of the iWork installer called "iWorkServices.pkg" is installed as a startup item with read/write/execute abilities with the pirated versions.
According to Intego, the rogue software connects to a remote server to notify its creator that the trojan has been installed on different Macs, and he or she can "connect to them and perform various actions remotely", including downloading additional components to the machine.
Intego considers the risk of infection to be serious, warning of "extremely serious consequences" if a user's Mac is compromised by software. The security firm said 20,000 people had already downloaded the installer at the time of its alert. As of now, Intego counts 1,000 more since the initial warning.
In an update on the matter Monday morning, Intego said Macs infected with the trojan are being pushed new code that downloads in the background, which is then being used to facilitate a DDoS (distributed denial of service) attack on certain websites.
Photoshop CS4
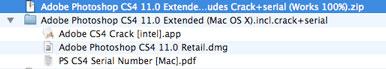
As part of its update, Intego also says it has discovered a new variant of the same Trojan horse called "OSX.Trojan.iServices.B", which can be found in pirated versions of Adobe Photoshop CS4. This installer has already been downloaded by 5,000 people who are now at risk, the firm says.
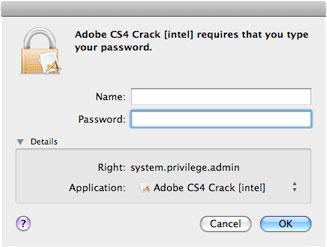
This installer compromises the system not by installing an additional package, but through a crack application that serializes the program for use without a purchased retail key. This app extracts an executable from its data and installs a backdoor in /var/tmp/. If the user runs the crack app again, a new executable with a different random name is created, making it difficult to safely remove the malware.
Once the administrator password is entered, a backdoor with root privileges is launched, copying the executable to /usr/bin/DivX and a startup item in /System/Library/StartupItems/DivX. It then makes repeated connections to two IP addresses, according to Intego.
A malicious user can then connect to the affected Macs and perform various actions and downloads remotely. Intego predicts this Trojan horse may also be used to execute similar DDoS attacks.
Warning
As a result of these two very serious risks, Intego is warning Mac users not to download any cracking software from sites that distribute it.
"The risk of infection is serious, due to the number of infected users, and these users may face extremely serious consequences if their Macs are accessible to malicious users," reads a notice on the security firm's website.
Intego recommends that users never download and install software from untrusted sources or questionable websites.  It says its own VirusBarrier X4 and X5 products with virus definitions dated January 22, 2009, or later will protect against these two Trojan horses.
 Zach Spear
Zach Spear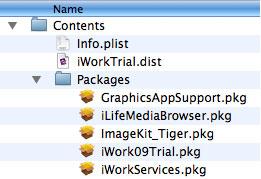













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee









91 Comments
Tens of thousands of users who've downloaded pirated versions of iWork '09 or Photoshop CS4 may have opened their Macs to remote attacks from malicious users.
*snip*
Stupid question: Why do these apps need an installer at all? Most OS X apps are .app folders that you simply need to drag and drop into the Applications folder. I understand there are exceptional cases like iTunes that need to write to the system folders, but why do iLife and iWork need to do so?
Stupid question: Why do these apps need an installer at all? Most OS X apps are .app folders that you simply need to drag and drop into the Applications folder. I understand there are exceptional cases like iTunes that need to write to the system folders, but why do iLife and iWork need to do so?
Well, it depends. IMO, there are two different kind of apps - one that have installer such as CS4, iWork, iLife, Apple Pros, etc. and other that doesn't have installers are FF3, AppZap, etc. that enable to drag and drop into App folder from DMG.
I may be wrong but that is what I think.
Tens of thousands of users who've downloaded pirated versions of iWork '09 or Photoshop CS4 may have opened their Macs to remote attacks from malicious users.
iWork '09
Mac security software maker Intego discovered last week what it calls "OSX.Trojan.iServices.A" in pirated copies of Apple's iWork '09 making the rounds on BitTorrent file sharing networks.* An additional package not found in retail copies of the iWork installer called "iWorkServices.pkg" is installed as a startup item with read/write/execute abilities with the pirated versions.
According to Intego, the rogue software connects to a remote server to notify its creator that the trojan has been installed on different Macs, and he or she can "connect to them and perform various actions remotely", including downloading additional components to the machine.
Intego considers the risk of infection to be serious, warning of "extremely serious consequences" if a user's Mac is compromised by software. The security firm said 20,000 people had already downloaded the installer at the time of its alert.* As of now, Intego counts 1,000 more since the initial warning.
In an update on the matter Monday morning, Intego said Macs infected with the trojan are being pushed new code that downloads in the background, which is then being used to facilitate a DDoS (distributed denial of service) attack on certain websites.
Photoshop CS4
As part of its update, Intego also says it has discovered a new variant of the same Trojan horse called "OSX.Trojan.iServices.B", which can be found in pirated versions of Adobe Photoshop CS4.* This installer has already been downloaded by 5,000 people who are now at risk, the firm says.
This installer compromises the system not by installing an additional package, but through a crack application that serializes the program for use without a purchased retail key.* This app extracts an executable from its data and installs a backdoor in /var/tmp/.* If the user runs the crack app again, a new executable with a different random name is created, making it difficult to safely remove the malware.
Once the administrator password is entered, a backdoor with root privileges is launched, copying the executable to /usr/bin/DivX and a startup item in /System/Library/StartupItems/DivX.* It then makes repeated connections to two IP addresses, according to Intego.
A malicious user can then connect to the affected Macs and perform various actions and downloads remotely.* Intego predicts this Trojan horse may also be used to execute similar DDoS attacks.
Warning
As a result of these two very serious risks, Intego is warning Mac users not to download any cracking software from sites that distribute it.
"The risk of infection is serious, due to the number of infected users, and these users may face extremely serious consequences if their Macs are accessible to malicious users," reads a notice on security firm's website.
Intego recommends that users never download and install software from untrusted sources or questionable websites.**It says its own VirusBarrier X4 and X5 products with virus definitions dated January 22, 2009, or later will protect against these two Trojan horses.
[ View this article at AppleInsider.com ]
HA! I don't feel sorry for those people. Pirate software will always come with Trojan, viruses, etc. I'd rather stick to legit software though.
The number of idiots downloading these astound me. Especially since they could both be downloaded directly from their respective manufacturer.
Honestly, they get what is coming to them.
Stupid question: Why do these apps need an installer at all? Most OS X apps are .app folders that you simply need to drag and drop into the Applications folder. I understand there are exceptional cases like iTunes that need to write to the system folders, but why do iLife and iWork need to do so?
If you try to run the apps without installing you'll get a dialog box that says something to the effect of "Pages is missing files iWork needs. Please run the iWork installer from your disc". You can choose to Run Anyway, or Quit, as I found out recently after reinstalling OS X. How did this happen? I bought my copy of iWork after using the trial download, but Apple no longer offers iWork '08 trial downloads now that iWork '09 is around. Unfortunately it wasn't as easy as I'd hoped.