Lookout, Retrevo warn of growing Android malware epidemic, note Apple's iOS is far safer
Last updated
Lookout collects information from ten million devices globally via integration with more than 700,000 apps. The firm reports an 85 percent increase in the number of mobile malware detections among its monitored users, noting that Android users are 2.5 times as likely to encounter malware than just six months ago.
In the first half of the year, Lookout reports that unique Android apps tainted with malware had grown from 80 to more than 400 titles by June. Even so, Lookout noted that "while [Android] malware has increased at a faster rate then spyware, Android users are still slightly more likely to encounter spyware than malware."
In contrast, there are no known iOS malware or spyware apps in the App Store. As Lookout states, "currently, malware and spyware have primarily targeted Android devices, though there are commercial spyware applications available for jailbroken iOS devices."
The open nature of Android's official Google Market, Amazon's Appstore, and other alternative download sites has enabled malicious users to easily add malware to existing legitimate apps and then repost them for sale or free distribution. One example of this, known as DroidDream, has been added to at least 80 different Android titles, using a process illustrated by Lookout (below).
Lookout also drew attention to a new risk for Android Market users it refers to as an "update attack." The firm notes that "recently, malware writers have begun using application updates as an attack method in the Android Market. A malware writer first releases a legitimate application containing no malware. Once they have a large enough user base, the malware writer updates the application with a malicious version."
Malvertizing also unique to Android
Another vector for malware distribution on Android devices is tainted web links, where users are directed to click on links (sometimes through legitimate looking mobile ads) that open up a web page and cause tainted software to automatically be downloaded to the device.
Lookout warns the this new threat, referred to as "malvertizing," has successfully ensnared about three out of ten users and that the practice is growing.
The design of iOS prevents software from being directly downloaded off the web, although web based exploits can be used to attack Apple's devices. "Thankfully," Lookout notes, "we haven't seen evidence of these exploits being used maliciously; they were primarily used to allow users to jailbreak their devices."
Both iOS and Android users can fall prey to phishing scams, which don't necessarily involve any breech of security or installation of malware. Instead, users are simply tricked into supplying their login credentials, credit card information, or other data through a social engineering scam.
Mobile security through software patches
Protection from the potential security threats of exploitable software is delivered through firmware and OS updates. Lookout notes that among Android devices, "it is up to device manufacturers to produce a device-specific firmware update incorporating the vulnerability fix, which can take a significant amount of time if there are proprietary modifications to the device's software."
Android licensees often take between three to six months to deliver the latest updates to their users. Apple provides updates that users can install the same day they are made available, as there are no middleman hardware makers or carriers to hold up the rollout of such software. Still, many users fail to update their iOS devices, Lookout notes.
"Many users simply plug their iOS devices into an outlet to charge them and rarely sync. According to one report, as many as 50 percent of iPhone users do not regularly sync with iTunes and thus are unlikely to receive critical security updates," Lookout states.
The firm adds that "Apple has announced that its upcoming iOS 5 will support firmware updates downloaded over the air and will not require syncing with a computer to apply them."
Mobile security from physical threats
An additional risk noted by Lookout involves physical threats, where a user's phone is lost or stolen and sensitive information can be recovered. In this respect, users can protect themselves using password protection or other precautions to protect their data.
A report by Retrevo notes that out of a 1,000 users, 61-62 percent of iPhone and BlackBerry users were using password protection, while only 49 percent of Android users were. Conversely, only 29 percent of iPhone users said they having done anything to prevent others from misusing data on their phone, while 39 percent of Androids users said they weren't doing anything.
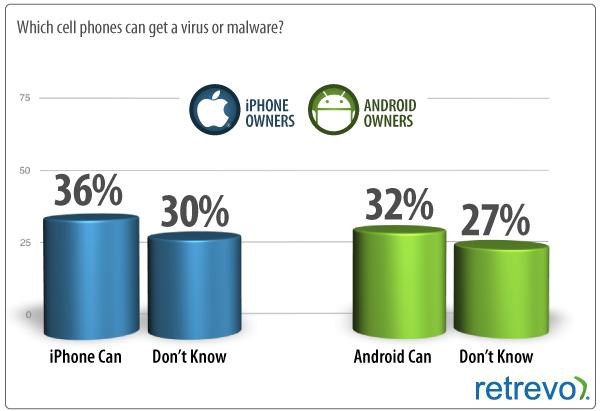
The firm reported similar numbers on the awareness of viruses and malware, stating, "Apple iPhones are much less susceptible to malware partly because more stringent oversight from Apple keeps iPhone owners out of harm's way. The open sourced-based Android phones are much more susceptible to malware however it appears that fewer Android owners are aware of this."
While 36 percent of iPhone owners reported thinking that their phone could be infected by malware, only 32 percent of Android users were aware of any risk, despite the sharply growing threat among Android phones and the far greater likelihood of infection due to the permissiveness of Google's software platform design.
In terms of recovering a lost phone, only 26 percent of iPhone users said they didn't know how to use a recovery service (such as Apple's Find My iPhone), while 39 percent of Android users didn't know about recovery options. Conversely, 37 percent of iPhone users said they would use a recovery service, while only 18 percent of Android users said they would.
 Daniel Eran Dilger
Daniel Eran Dilger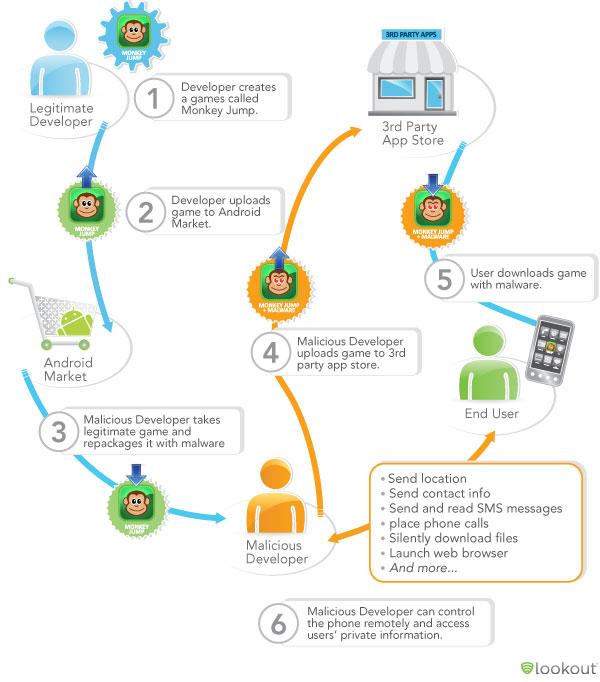













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee









52 Comments
iOS is only more secure since it has lower market share than Android. Once iOS market share increases closer to that of Android, it will see far more virii and malware since it is not more inherently secure on the os level...
ok whats new in this post? anyone?
iOS is only more secure since it has lower market share than Android. Once iOS market share increases closer to that of Android, it will see far more virii and malware since it is not more inherently secure on the os level...
idiot...
idiot...
I second that motion.
idiot...
Sarcasm - maybe you've heard of it?