Researcher accuses Apple of ignoring iCloud brute-force attack for 6 months
A security researcher who discovered a brute-force attack against Apple's iCloud service in March — similar to the "iBrute" vulnerability that surfaced in conjunction with the celebrity photo hacking scandal earlier this month — says that the company refused to address the flaw for months after he reported it.
Computer security expert Ibrahim Balic first notified members of Apple's product security team of the vulnerability in late March, according to copies of correspondence that Balic provided to The Daily Dot. At the time, Balic told company representatives that he had been able to test as many as 20,000 passwords against specific accounts.
Apple employees were still working with Balic to assess the situation as late as May, when they appeared to discount its severity.
"Using the information that you provided, it appears that it would take an extraordinarily long time to find a valid authentication token for an account," one Apple engineer wrote back to Balic. "Do you believe that you have a method for accessing an account in a reasonably short amount of time?"
It is unclear what relationship the bug that Balic discovered — Â which he believes went unresolved — has to the iBrute tool that allowed a similar attack against Find my iPhone. Apple later denied that the Find my iPhone vulnerability had been used in the now-infamous photo scandal, saying instead that it was the result of a "targeted attack" that likely involved years of social engineering against the targets.
 Sam Oliver
Sam Oliver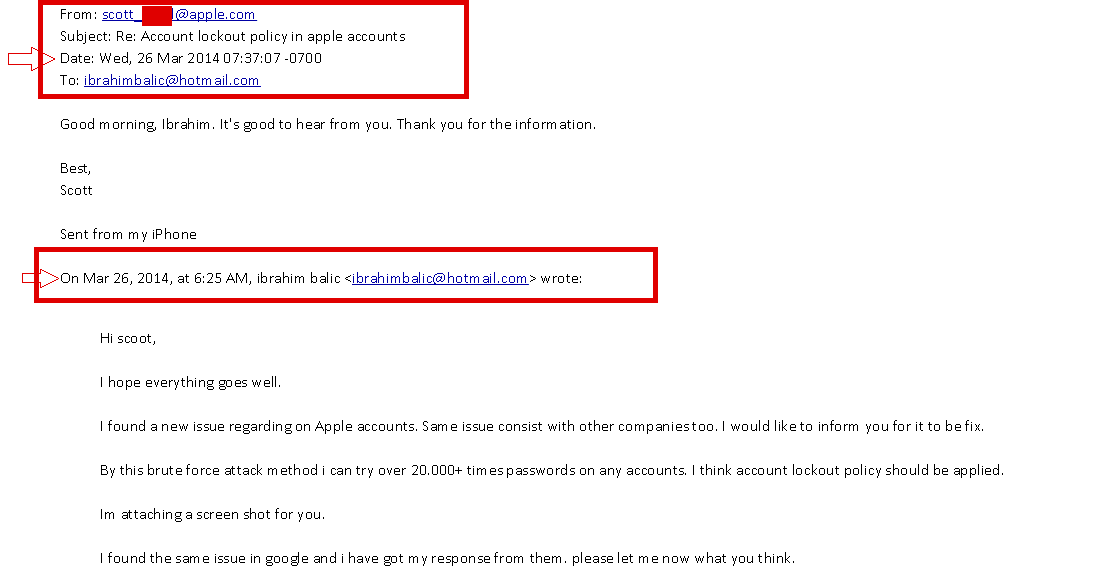








 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee









94 Comments
And I told Apple I want NFC in my iPhone for years and only now Apple releases a phone with NFC, talking about slow... and can you hear me, Apple, hello? I'm going to tell the world that you ignored me for two years... Hello?
"Apple later denied that the Find my iPhone vulnerability had been used in the now-infamous photo scandal, saying instead that it was the result of a "targeted attack" that likely involved years of social engineering against the targets." I'm not sure that's exactly what Apple said. As I recall they used some very specific wording that was perhaps meant to give that impression, but they did not issue a denial.
So they didnt ignore it. They were told about it. They responded. Just because tthey didn't put in s lockout doesn't mean they were doing nothing. Beside a lockout is a placebo in many respects because someone can still use piss poor security questions or phish for passwords. And there is still no proof of exactly how those few celeb accounts were accessed to know if this flaw was s factor. Heck we don't even know how many accounts there were that were actually iCloud ones
Unimportant individuals trying to achieve some level of importance before vaguely-qualified peers. Goal = income.
[quote name="Gatorguy" url="/t/182511/researcher-accuses-apple-of-ignoring-icloud-brute-force-attack-for-6-months#post_2606280"]"Apple later denied that the Find my iPhone vulnerability had been used in the now-infamous photo scandal, saying instead that it was the result of a "targeted attack" that likely involved years of social engineering against the targets." I'm not sure that's exactly what Apple said. As I recall they used some very specific wording that was perhaps meant to give that impression, but they did not issue a denial.[/quote] Supposedly it was this: [quote]CUPERTINO, Calif.–(BUSINESS WIRE)–We wanted to provide an update to our investigation into the theft of photos of certain celebrities. When we learned of the theft, we were outraged and immediately mobilized Apple’s engineers to discover the source. Our customers’ privacy and security are of utmost importance to us. After more than 40 hours of investigation, we have discovered that certain celebrity accounts were compromised by a very targeted attack on user names, passwords and security questions, a practice that has become all too common on the Internet. None of the cases we have investigated has resulted from any breach in any of Apple’s systems including iCloud® or Find my iPhone. We are continuing to work with law enforcement to help identify the criminals involved. To protect against this type of attack, we advise all users to always use a strong password and enable two-step verification. Both of these are addressed on our website at http://support.apple.com/kb/ht4232. [/quote]