A newly-discovered flaw in some implementations of cryptographic protocols SSL and TLS — including those used by Apple's Safari and Google's Android AOSP browsers — could allow an attacker to force clients to use older, weaker encryption that would make it significantly easier to intercept secure communications.
Dubbed the "FREAK" attack, for "Factoring RSA Export Keys," the exploit relies on long-deprecated "export grade" encryption support mandated by the NSA during the crypto wars of the early 1990s. As noted by the Washington Post, the agency attempted to cap the strength of encryption software that could be exported outside the U.S., forcing engineers to design cryptographic libraries that could accept connections from both domestic clients with stronger encryption and foreign clients with weaker encryption.
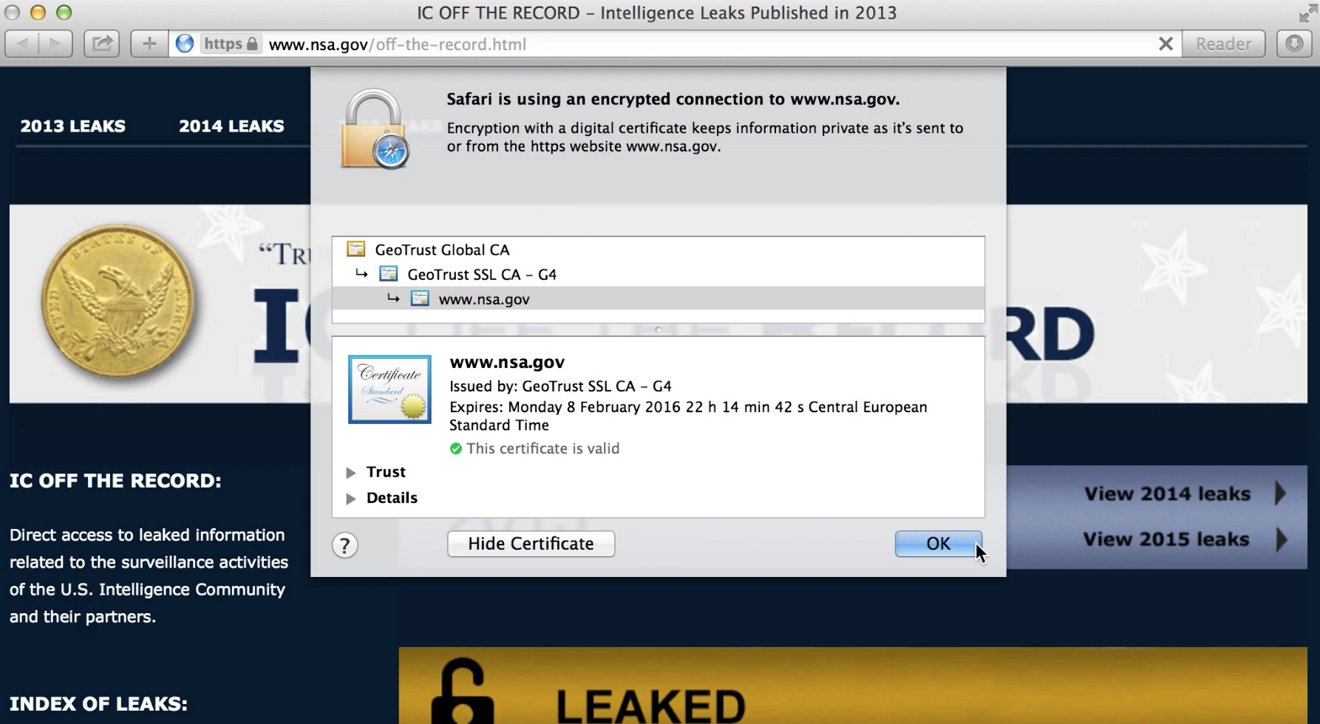
Though the NSA abandoned this strategy in 2000, legacy support for such connections remains in many SSL/TLS clients and servers. The strength of encryption for a particular session is negotiated between the client — for example, Safari — and the server during the first "handshake;" researchers discovered that some clients would still accept the weaker export grade ciphers, even if they requested stronger encryption during the handshake.
This presents a problem when a vulnerable client attempts to connect to a host that still makes export ciphers available. An attacker can acquire and pre-crack the weaker export key from the server, then use it to masquerade as the legitimate host in a man-in-the-middle attack.
Apple has promised to distribute a client-side patch for the issue on both iOS and OS X by next week, while the researchers who discovered the flaw — from INRIA, IMDEA, and Microsoft Research — have been working to notify hosts who still serve export ciphers. Many of the latter, including content delivery network Akamai and Facebook, have disabled support for export ciphers on their servers.