'KeyRaider' malware harvests 225,000 Apple IDs from jailbroken iOS devices
A new form of iOS malware making its way around the jailbreak scene has resulted in the theft of credentials linked to at least 225,000 Apple IDs, resulting in fraudulent app purchases and in some cases ransom demands.
KeyRaider — Â discovered by researchers at Palo Alto Networks and WeipTech — is primarily distributed via Cydia repositories in China, but has been found on devices owned by users throughout the world, including the UK and the U.S. Those firms began investigating earlier this summer, after some users of jailbroken iOS devices found unauthorized purchases or other abnormalities in their Apple account.
The malware collects a number of other items in addition to Apple ID usernames and passwords. It also targets the device's unique identifier, or GUID, alongside security certificates and private keys for Apple push notification service as well as App Store purchase data.
KeyRaider also disables the ability to unlock iOS devices on which it's installed, a feature occasionally used to remotely hold devices for ransom.
The researchers say KeyRaider is linked to two other jailbreak tweaks that let users download App Store apps for free. Using the stolen credentials, those tweaks impersonate legitimate users in App Store purchase requests.
KeyRaider's appearance underscores that jailbreaking, despite being occasionally useful, represents a significant security risk for users. While iOS is impressively secure in its default configuration, jailbreaking necessarily removes some protections and opens devices up to unwanted data exfiltration.
 AppleInsider Staff
AppleInsider Staff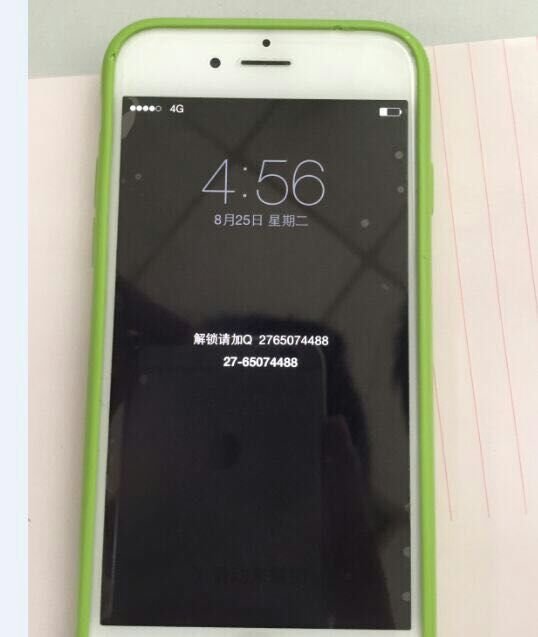








 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly

 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee










48 Comments
The iOS "Walled Garden" doesn't seem so bad now, does it? :)
KeyRaider's appearance underscores that jailbreaking, despite being occasionally useful, represents a significant security risk for users. While iOS is impressively secure in its default configuration, jailbreaking necessarily removes some protections and opens devices up to unwanted data exfiltration.
At this point I have no sympathy for the jailbreaking community. Even in the early days of jailbreaking when you could make an argument for doing it I never saw the value of hacking something that contains the amount of personal information the average smartphone contains...
Imagine that. A jailbroken device has a flaw that can be exploited.
I'm surprised there aren't anti-virus software on Cydia by now.
At this point I have no sympathy for the jailbreaking community. Even in the early days of jailbreaking when you could make an argument for doing it I never saw the value of hacking something that contains the amount of personal information the average smartphone contains...
The weakest link in security is stupid users. This is akin to walking up to a stranger on the street -- borrowing a dirty needle and injecting yourself with it....