A new version of the long-running Genieo adware has brought with it a new technique for accessing the OS X Keychain without user intervention, a security gray area that could be used by other malicious actors to make off with sensitive data stored in the Mac credential manager.
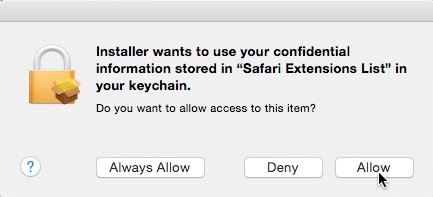
The adware depends on an OS X feature that is designed to prevent users from being forced to enter their account password multiple times in quick succession. As discovered by Malwarebytes, the Genieo installer asks users to authenticate with their password prior to installation — Â but it later mounts a special app that asks for keychain access, prompting a different dialog that asks the user whether to allow or deny that access.
This secondary dialog does not prompt for a password, and the installer simulates a mouse click on the "Allow" button. The entire process takes just a fraction of a second.
Many users are unlikely to notice the window, and even those that do could be prone to ignore it.
Because this behavior does not rely on an OS X flaw, it is particularly dangerous and comes with a high potential for abuse. Such a request could be embedded in any seemingly innocuous file and is difficult to guard against without changing the behavior of the Keychain request dialog.
Even more worrying, OS X apps can, by design, request access to any Keychain entry they desire. It's left up to the user to decide whether that app should be allowed to have access, so this technique could be used to steal nearly anything that has a known Keychain entry.
Apple has not yet responded to these reports, though they may address the problem before the release of OS X El Capitan.
As always, users should follow common-sense security practices: do not download files from unknown sources, and be wary of e-mails or websites that seem suspicious or non-authentic.